How to Pass the AZ-500 Azure Security Exam in 2026
Complete AZ-500 Azure Security Technologies exam guide: study plan, hands-on labs, identity protection, network, data security, and security ops.
Survive the Azure AD B2C Sunset with Entra External ID
Learn how to migrate Azure AD B2C to Microsoft Entra External ID—covering JIT credential migration, custom policy translation, HSC mode decisions, and phased cutover strategies.
Slash SOC 2 Audit Prep with Azure Policy Automation
Learn how to automate SOC 2 Type II compliance on Azure using Azure Policy, Defender for Cloud, Entra PIM, and EPAC to continuously generate audit evidence.
How to Secure Azure Service Accounts with Managed Identities
Learn how to replace secret-based Azure service accounts with managed identities, grant least-privilege Azure RBAC access, validate token-based authentication, and remove stored secrets.
Entra Workload Identity on AKS: No More Secrets
Learn how to eliminate Kubernetes secrets by configuring Entra Workload Identity on AKS using OIDC federation, with Bicep and Terraform IaC examples.
Fix Azure Cost Reporting with a FinOps Tagging Strategy
Build an Azure resource tagging taxonomy, enforce it with Azure Policy, and automate remediation of untagged resources to enable accurate FinOps cost allocation and chargebacks.
Secure Azure OpenAI Deployments for the Enterprise
Learn how to deploy Azure OpenAI securely for enterprise use: configure private endpoints, replace API keys with Managed Identities, set up content filtering policies, and build comprehensive audit logging with Azure API Management.
Automate SOC 2 Compliance with PowerShell and Azure
Learn how to use Azure Policy, the EPAC framework, and PowerShell to automate SOC 2 compliance evidence collection, enforce controls across subscriptions, and build a continuous audit trail.
Avoid Entra ID Lockouts: Migrate Legacy MFA Policies
Learn how to migrate legacy MFA and SSPR policies to the unified Entra ID Authentication Methods policy, including audit, NPS extension fixes, and validation.
Secure Azure OpenAI Deployments for the Enterprise
Learn how to deploy Azure OpenAI securely for enterprise use: configure private endpoints, replace API keys with Managed Identities, set up content filtering policies, and build comprehensive audit logging with Azure API Management.
Microsoft 365 E7: Is the $99/User Price Tag Worth It?
Evaluate whether Microsoft 365 E7's $99 price justifies Agent 365 governance using PowerShell scripts to assess Copilot usage and automation risk exposure.
Stop Shadow AI with Microsoft Purview
With 80% of Fortune 500 companies now using active AI agents, employees are increasingly using unapproved generative AI tools that process sensitive corporate data outside of governance controls. This post demonstrates how to use Microsoft Purview and Defender for Cloud Apps to discover shadow AI usage, classify sensitive data, enforce data loss prevention policies, and build an AI governance framework that satisfies compliance requirements.
Build Production Multiagent AI Systems with Azure AI Foundry
Learn the orchestration patterns, security practices, and production engineering decisions for building multiagent AI systems on Azure AI Foundry.
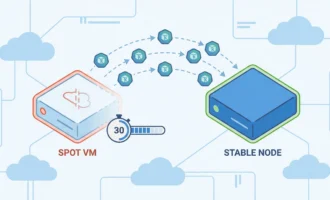
Build Auto-Migration Systems for Azure Spot VMs in AKS
Build automated migration systems to handle Azure Spot VM evictions in AKS, keeping workloads running within the 30-second window.
Azure Databricks Serverless Cost Optimization Guide
Learn to reduce Azure Databricks costs with serverless compute, Liquid Clustering, auto-termination tuning, and budget controls.
Transition from SysAdmin to Cloud Engineer
System administrators already have the networking, Linux, and operational expertise that cloud engineering demands. This guide maps the philosophy shift, technical domains, certifications, and portfolio steps to make the transition.