Build Production Multiagent AI Systems with Azure AI Foundry
Learn the orchestration patterns, security practices, and production engineering decisions for building multiagent AI systems on Azure AI Foundry.
Prove Every Artifact: Supply Chain Security in Azure DevOps
Learn to implement software supply chain security in Azure DevOps with SBOM generation, artifact signing, dependency scanning, and deployment gate enforcement.
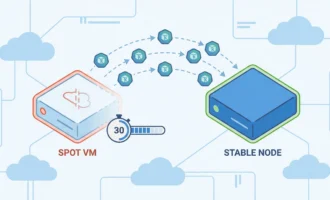
Build Auto-Migration Systems for Azure Spot VMs in AKS
Build automated migration systems to handle Azure Spot VM evictions in AKS, keeping workloads running within the 30-second window.
Azure Databricks Serverless Cost Optimization Guide
Learn to reduce Azure Databricks costs with serverless compute, Liquid Clustering, auto-termination tuning, and budget controls.
Transition from SysAdmin to Cloud Engineer
System administrators already have the networking, Linux, and operational expertise that cloud engineering demands. This guide maps the philosophy shift, technical domains, certifications, and portfolio steps to make the transition.
How to Migrate SQL Server to Azure SQL Database
Learn how to migrate SQL Server to Azure SQL Database using Azure DMS and SqlPackage, covering assessment with Azure Arc, schema migration, data movement, and post-migration validation.
How to Ace a DevOps Interview: DORA, Kubernetes, and Terraform
Learn what DevOps interviewers actually test: DORA metrics, Kubernetes pod lifecycle, Terraform state management, system design, and behavioral questions with quantified results.
How to Pass the AZ-104 Azure Administrator Exam
Study strategy for the AZ-104 Azure Administrator exam covering the five domains, study resources, practice tests, and time management tactics for exam day.
Control Traffic with Network Security Groups
Create and manage Azure NSG rules, service tags, and application security groups to control inbound and outbound traffic using Azure CLI.
Stop Leaving Money on the Table: IT Salary Negotiation
Learn salary negotiation strategies for IT professionals, from researching market rates with Levels.fyi to handling counteroffers and maximizing total compensation.
Azure Container Apps: Instant Preview Environments per PR
Build isolated preview environments for every pull request using Azure Container Apps revision labels and Azure DevOps pipelines with scale-to-zero economics.
Prevent Azure VM Outages with Load Balancer Health Probes
Create a Standard Azure Load Balancer with the Azure CLI, configure health probes and backend pools, and distribute traffic across zone-redundant VMs.
Fix Broken Azure DevOps Pipelines: A Systematic Guide
Azure DevOps pipeline failures rarely point to the real problem. Learn systematic troubleshooting techniques to diagnose cryptic errors, network issues, and infrastructure limits.
Ready to Move Beyond Lift-and-Shift? An Azure Migration ROI Guide
Learn when to move beyond Azure lift-and-shift to PaaS services. Calculate ROI for modernization, optimize costs with Hybrid Benefit, and choose the right migration strategy for SQL Server and web apps.
Containers vs. gVisor vs. MicroVMs for Azure AI Agent Security
Compare standard containers, gVisor, and microVMs for securing Azure AI agents. Learn which isolation technology provides the right security/performance balance for your workload.
Replicate Data Across Zones with Azure NetApp Files
Configure cross-zone replication for Azure NetApp Files to protect against availability zone failures with asynchronous replication and zero network transfer fees.