Stop Leaving Money on the Table: IT Salary Negotiation
Learn salary negotiation strategies for IT professionals, from researching market rates with Levels.fyi to handling counteroffers and maximizing total compensation.
How to Ace the Modern Coding Interview as a SysAdmin
Master coding interviews for sysadmin and DevOps roles with practical preparation strategies. Learn Python, Bash, and platform-specific techniques that translate your operational experience into interview success.
How to Fix Active Directory’s #1 Weak Point in 2026: Passwords
It's 2026. Despite years of momentum around passwordless authentication, the reality in most enterprise environments is still the same: Active Directory remains at the core of identity infrastructure, and passwords are still the primary authentication mechanism. In that context, it's important to be clear: investing in an EDR or a SIEM does not automatically eliminate the biggest identity risks. A single credential leak, whether through phishing, password spraying, reuse, or data exposure, can be enough to compromise an entire Active Directory domain. At the same time, relying solely on traditional password best practices (complexity rules, uppercase letters, special characters, etc.) is no longer sufficient. That's not surprising: attack techniques have evolved significantly, while Active Directory's native security controls around credentials and authentication have seen limited evolution over the years. In this article, we'll break down the most common attack paths and the technical limitations of Active Directory, before exploring practical mitigation strategies and solutions that can effectively address these weaknesses. Why Active Directory Remains a Prime Target To understand why Active Directory remains one of the top targets, you need to look at the role it plays in enterprise environments. In most organizations, on-premises Active Directory is still the authoritative source of truth for authentication and access control. This remains true even in many hybrid setups, where Microsoft Entra ID (formerly Azure AD) handles cloud identities while AD continues to anchor the core identity layer. On a day-to-day basis, Active Directory is heavily involved in critical workflows: Kerberos authentication, access to file servers, RDP logons to servers, VPN authentication, and much more. In many cases, AD also extends into the cloud through Microsoft Entra Connect, synchronizing user objects, and often password hashes, to support hybrid identity scenarios. As a result, compromising Active Directory effectively means gaining control over the entire identity backbone: the "keys to the kingdom." That alone explains why AD remains a priority target wherever it is deployed.
EasyEntra: A Look at Hybrid User Management with Virtual Templates
EasyEntra consolidates Active Directory and Entra ID management into a single interface. This hands-on review explores Virtual User Templates—a feature that standardizes user provisioning across hybrid environments.
Active Directory: Add MFA to Windows with Specops Secure Access
Learn how to deploy Specops Secure Access to add multi-factor authentication (MFA) to Windows logins and Remote Desktop connections in Active Directory environments.
How to Block Known Bad Active Directory Passwords
In this article, we will explore why and how to block the use of certain passwords for Active Directory user accounts. In an Active Directory environment, password security is a critical factor in protecting user accounts against cyberattacks. However, even with a strict password policy in place, some users or administrators may still choose weak passwords or ones that can be easily guessed. To strengthen the security of your domain, it is possible to prevent the use of specific passwords.
Migrating from PowerShell 6 to 7.5: Breaking Changes/New Features
Migrate from PowerShell Core 6 to 7.5: breaking changes, features, and testing tips.
Boost your Active Directory Security with this Free Audit
Scan your Active Directory passwords for strength and find weaknesses with a free Specops audit.
Fortifying the Frontline: Protecting Helpdesks from Social Engineering
Helpdesks are prime targets for social engineering. Specops Secure Service Desk ensures only verified users gain access, stopping attackers at the source.
How to Add Timeouts to Pester Tests with PowerShell Runspaces
Prevent Pester tests from hanging indefinitely using PowerShell runspaces. Learn to handle variable scoping, module loading, TestDrive access, and stream capture challenges with timeout protection.
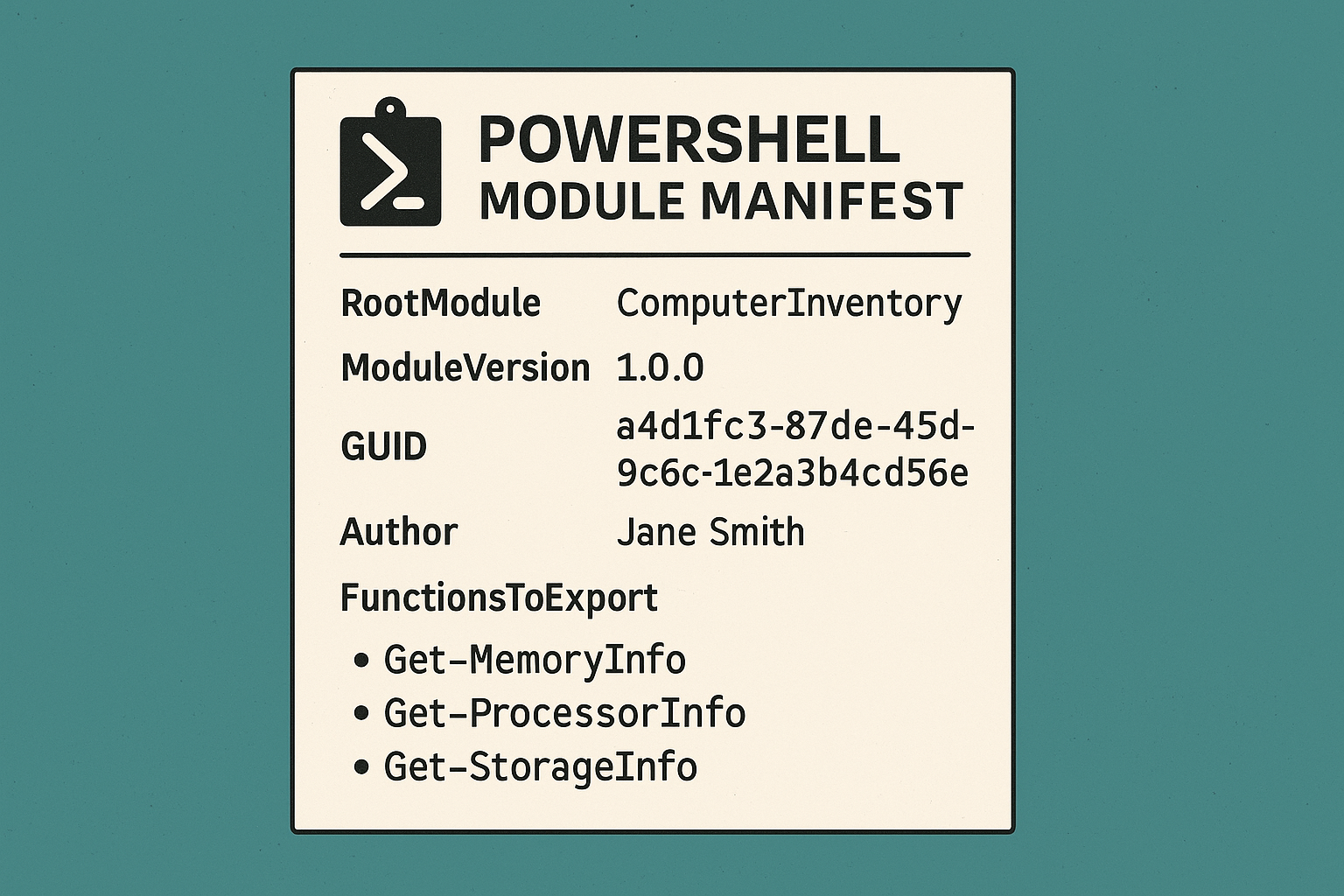
PowerShell 101: Creating a Module Manifest
Maybe you've put together some great functions but struggle to make them cohesive, intuitive, or shareable. Without a way to define your module's identity and functionality, managing or scaling as your scripts evolve into robust tools can be a headache. Not unless you have a module manifest in place.
Creating a Real-World Module: Creating Functions
Learn how to create PowerShell functions that gather memory, storage, and processor information from remote systems, transforming raw output into readable formats.
Creating a Real-World PowerShell Module: Scaffolding Functions
Learn how to create a custom PowerShell module for computer inventory management. This hands-on guide covers module structure, functions, and remote capabilities.
PowerShell 101: Creating a Real-World Module: Scaffolding Functions
Learn how to create powerful PowerShell modules from scratch by building a computer inventory tool. Perfect for sysadmins who need custom automation solutions.
PowerShell 101: Finding and Installing New Modules
Learn how to find, install, verify and remove PowerShell modules efficiently. Master module management to enhance your PowerShell automation capabilities.
PowerShell 101: Importing Modules
Learn how to manage PowerShell modules like a pro! From importing and removing modules to troubleshooting common issues, master PowerShell modules in this complete guide.