Adam Bertram
Adam Bertram is a 20+ year veteran of IT and an experienced online business professional. He’s a consultant, Microsoft MVP, blogger, trainer, published author, and content marketer for multiple technology companies.
Ready to Move Beyond Lift-and-Shift? An Azure Migration ROI Guide
Learn when to move beyond Azure lift-and-shift to PaaS services. Calculate ROI for modernization, optimize costs with Hybrid Benefit, and choose the right migration strategy for SQL Server and web apps.
Containers vs. gVisor vs. MicroVMs for Azure AI Agent Security
Compare standard containers, gVisor, and microVMs for securing Azure AI agents. Learn which isolation technology provides the right security/performance balance for your workload.
Replicate Data Across Zones with Azure NetApp Files
Configure cross-zone replication for Azure NetApp Files to protect against availability zone failures with asynchronous replication and zero network transfer fees.
How to Ace the Modern Coding Interview as a SysAdmin
Master coding interviews for sysadmin and DevOps roles with practical preparation strategies. Learn Python, Bash, and platform-specific techniques that translate your operational experience into interview success.
The Complete Guide to FIPS 140-2 on Azure Application Gateway v2
Learn how to enable and configure FIPS 140-2 compliance on Azure Application Gateway v2, including TLS policy restrictions, backend compatibility, and troubleshooting 502 errors.
Is Your Azure Service Retiring? Build a PowerShell Monitor
Build a PowerShell monitor that queries Azure Resource Graph to identify retiring services and alert your team before 90-day deadlines become 9-day emergencies.
Is Your Azure Service Retiring? Build a PowerShell Monitor
Build a PowerShell monitor that queries Azure Resource Graph to identify retiring services and alert your team before 90-day deadlines become 9-day emergencies.
5 Ways GitHub Copilot Supercharges Azure Boards
Learn how GitHub Copilot's coding agent integration with Azure Boards automates PR creation, ingests work item context, and clears backlog toil directly from your project management workflow.
Master the New Test Run Hub in Azure Test Plans
Learn how to use the Test Run Hub in Azure Test Plans to manage manual and automated test execution, filter runs, analyze results with embedded analytics, and triage failures.
Fortify Your Logs: A Guide to Secure, Cross-Zone Log Aggregation in Azure with Loki
Build a secure, pull-based log pipeline that centralizes DMZ logs without punching holes through your firewall using Grafana Loki, Azure Event Hubs, and Private Link.
How to Fix Active Directory’s #1 Weak Point in 2026: Passwords
It's 2026. Despite years of momentum around passwordless authentication, the reality in most enterprise environments is still the same: Active Directory remains at the core of identity infrastructure, and passwords are still the primary authentication mechanism. In that context, it's important to be clear: investing in an EDR or a SIEM does not automatically eliminate the biggest identity risks. A single credential leak, whether through phishing, password spraying, reuse, or data exposure, can be enough to compromise an entire Active Directory domain. At the same time, relying solely on traditional password best practices (complexity rules, uppercase letters, special characters, etc.) is no longer sufficient. That's not surprising: attack techniques have evolved significantly, while Active Directory's native security controls around credentials and authentication have seen limited evolution over the years. In this article, we'll break down the most common attack paths and the technical limitations of Active Directory, before exploring practical mitigation strategies and solutions that can effectively address these weaknesses. Why Active Directory Remains a Prime Target To understand why Active Directory remains one of the top targets, you need to look at the role it plays in enterprise environments. In most organizations, on-premises Active Directory is still the authoritative source of truth for authentication and access control. This remains true even in many hybrid setups, where Microsoft Entra ID (formerly Azure AD) handles cloud identities while AD continues to anchor the core identity layer. On a day-to-day basis, Active Directory is heavily involved in critical workflows: Kerberos authentication, access to file servers, RDP logons to servers, VPN authentication, and much more. In many cases, AD also extends into the cloud through Microsoft Entra Connect, synchronizing user objects, and often password hashes, to support hybrid identity scenarios. As a result, compromising Active Directory effectively means gaining control over the entire identity backbone: the "keys to the kingdom." That alone explains why AD remains a priority target wherever it is deployed.
How to Automate Azure VM Patching with Update Manager
Learn how Azure Update Manager automates patching across Azure VMs using native extensions, periodic assessment, and custom maintenance windows—without Log Analytics or Automation accounts.
A Practical Guide to Hosting and Managing Remote MCP Servers on Azure
Learn how to deploy MCP servers on Azure Container Apps, App Service, and Functions with proper authentication, SSE configuration, and production-ready infrastructure.
Effortless Spark: A Beginner\’s Guide to Serverless Workspaces in Azure Databricks
Learn how Azure Databricks serverless workspaces eliminate infrastructure complexity. This beginner's guide covers setup, costs, limitations, and when to use serverless vs traditional deployments.
EasyEntra: A Look at Hybrid User Management with Virtual Templates
EasyEntra consolidates Active Directory and Entra ID management into a single interface. This hands-on review explores Virtual User Templates—a feature that standardizes user provisioning across hybrid environments.
Outsmart Attackers: A Guide to Advanced Ransomware Protection with Azure NetApp Files
Learn how to configure advanced ransomware protection in Azure NetApp Files using ML-based detection to catch attacks before they destroy your data.
Active Directory: Add MFA to Windows with Specops Secure Access
Learn how to deploy Specops Secure Access to add multi-factor authentication (MFA) to Windows logins and Remote Desktop connections in Active Directory environments.
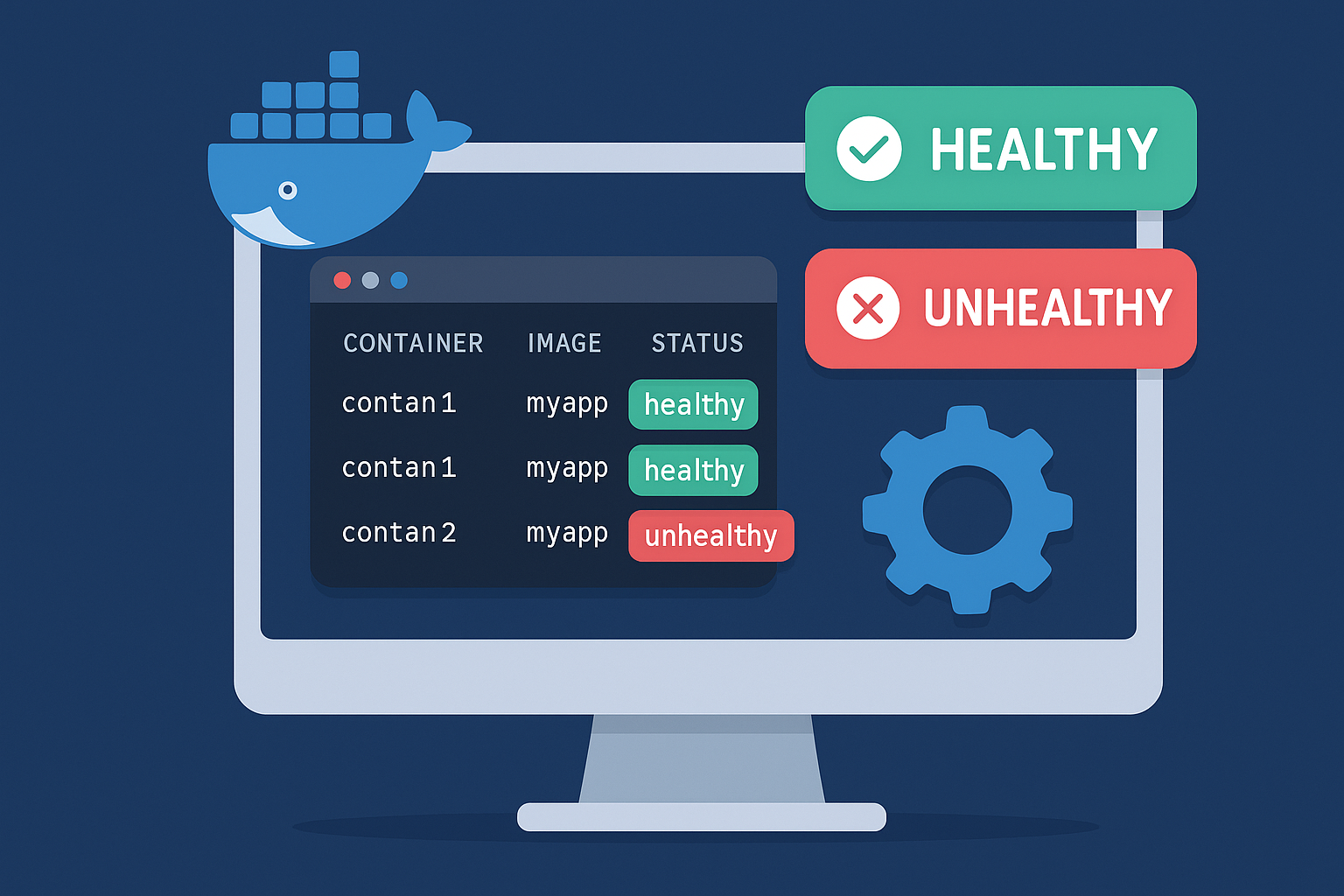
Automating Docker Container Health Checks with Python and Local Notifications
Docker's built-in health checks are passive—they tell Docker when a container fails, but do they tell you? In this tutorial, we'll build a lightweight Python monitoring system that runs entirely on your infrastructure with zero external dependencies. You'll learn to detect container failures in real-time, send instant alerts, and maintain a complete audit log of every state change.
How to Block Known Bad Active Directory Passwords
In this article, we will explore why and how to block the use of certain passwords for Active Directory user accounts. In an Active Directory environment, password security is a critical factor in protecting user accounts against cyberattacks. However, even with a strict password policy in place, some users or administrators may still choose weak passwords or ones that can be easily guessed. To strengthen the security of your domain, it is possible to prevent the use of specific passwords. If blocking bad Active Directory passwords is part of a larger identity-security learning plan, compare Udemy technical training courses for cloud, development, security, and business software skills before paying for another course library. Why block certain passwords? There are several scenarios in which it is advisable to prevent users or administrators from setting specific passwords. The larger and older an Active Directory environment becomes, the higher the likelihood of poor practices and notable weaknesses. Throughout my career as a pentester, I have conducted numerous internal penetration tests in companies of different sizes, levels of maturity, and industries. In many cases, password reuse across multiple user accounts allowed me to compromise several accounts, including privileged ones, which sometimes led to the complete compromise of the domain. To strengthen security and increase resilience against cyberattacks, it may be necessary to block specific passwords, especially when they arise from the following situations. Common initial password for all accounts A common practice within administration teams is to assign the same initial password (often referred to as a default password) to every new user, with the instruction to change it as soon as possible. A typical example of such a password could be “Welcome2024!”. However, this password change is not always enforced, especially when it is not technically required. In many cases, it is possible to find user accounts still configured with this password even years after their creation, either because they were never used, or because the password change requirement was not applied (e.g., technical accounts, test accounts, or so-called temporary accounts).