In Linux, the sudoers file is where you grant users elevated privileges. By default, only the root user has these privileges. But, in some cases, it may be necessary for regular users to have elevated privileges as well.
Not a reader? Watch this related video tutorial!The sudoers file is primarily for system administrators to manage and can be a bit daunting for newcomers. Don’t let that discourage you! With patience and attention to detail, anyone can learn to manage the sudoers file effectively.
This guide will teach you how to edit the sudoers and give users elevated privileges securely. You will also learn some best practices to keep in mind when working with sudoers. Don’t go anywhere; get ready to take your Linux user privileges management to the next level!
Prerequisites
This tutorial will be a hands-on demonstration. If you’d like to follow along, be sure you have a Linux system with a regular user account that you can use. This guide uses a Ubuntu 20.04 system, but any other Linux distribution should also work.
The Linux Sudoers File Overview
The sudoers file lives in the /etc/sudoers, a plain text file containing the policies on what privileges a user gains when executing the sudo command. Before going any further, it is essential to familiarize yourself with the sudoers file default contents and sections.
The screenshot below shows the default sudoers file contents on Ubuntu 20.04. The sudoers file default contents may differ between Linux distros.
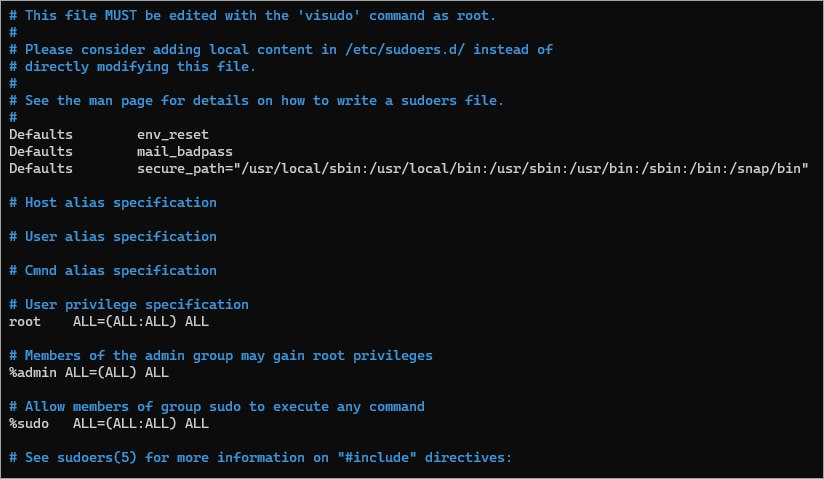
The following is a quick run down of the sections in the sudoers file.
Defaults Section

Defaults env_reset - Executing commands with sudo creates a new environment with minimal or default environment variables. In most Linux distros, sudo will load the environment variable in the /etc/environment file.
- Defaults mail_badpass – This line triggers sending an email to the root when a user enters a wrong password with sudo.
Defaults secure_path - This line defines the PATH environment variable that sudo uses instead of the user’s PATH environment.
User and Group Sudo Privileges
This line defines the sudo privileges for specific users or members of groups.
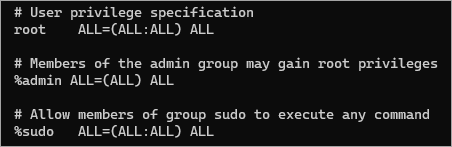
Note: The % at the beginning indicates that the policy applies to the group members.
- The first field defines that his policy applies to the
rootuser and the members of theadminandsudogroups. - The first
ALLmeans that the rule applies to all hosts. - The second
ALLallows therootaccount to run commands as any user. - The third
ALLallows therootaccount to run commands as any group. - The last
ALLmeans that this policy applies to command commands.
Include Directives
At the end of the file, you will see a line that looks like a comment but is not. The lines starting with #include and #includedir are called include directives.
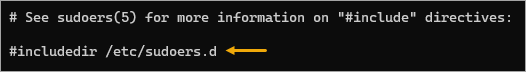
#includedir /etc/sudoers.d – This line tells sudo to look in the /etc/sudoers.d directory for any additional configuration files.
Editing the Sudoers File with the Right Tool
The sudoers file is a plain text file that you can open with your preferred text editor—but doing so is not advisable. Why? Because the sudoers file’s contents follow specific syntax, a regular text editor has no safeguards to prevent you from messing up the sudoers file.
Improper configuration can lead to security problems; worst, every user may lose the ability to elevate their privileges.
What’s the correct tool? — visudo. This tool opens the sudoers file in the default text editor. Additionally, visudo prevents concurrent editing and performs error-checking before exiting.
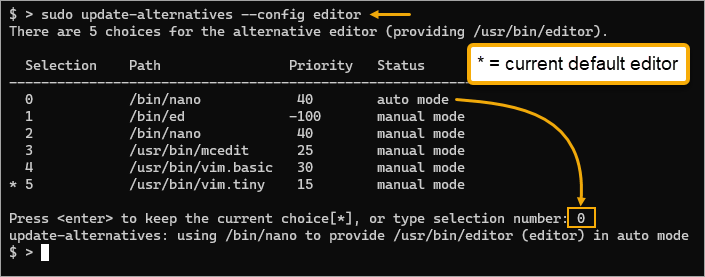
In Ubuntu 20.04, the default editor is vim, but you can set an alternative editor, such as nano, if you prefer.
1. Open a terminal session or SSH into your Linux machine.
2. Run the below command to list the available text editors on your computer.
sudo update-alternatives --config editorAs you can see, the current default editor is selection 5, which is vim. Suppose you prefer to keep the default, press Enter. If you prefer another editor, press the corresponding selection number, such as 0 for nano, and press Enter.
3. Now, run the below command to open the sudoers file in the default editor.
sudo visudoIf the sudoers file is open in another session, you will see the below error, and visudo will prevent you from opening the file. This way, no two users can make conflicting changes at the same time.
visudo: /etc/sudoers busy, try again later
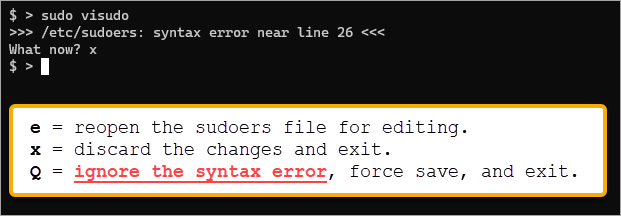
4. Once the sudoers file is open, deliberately cause a syntax error by deleting the last instance of ALL, then save and exit the editor.
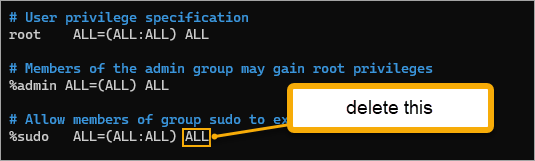
5. visudo will warn you that there’s a syntax error and asks, “What now?”. At this point, you have three options.
- Type
eand press Enter to re-edit the file. This option lets you correct the sudoers file in the editor again.
- Type
xand press Enter to discard the changes and exitvisudo.
- Type Q, press Enter to ignore the error, save the sudoers file, and exit visudo. Don’t choose this option unless you are sure of the consequences.
In this example, press x to discard the changes and retain the old sudoers file contents.
As you can see, it would be difficult to mess up the sudoers file with visudo permanently.
Granting Specific Privileges
Directly making changes to the sudoers file is doable but can become unmanageable as the policies and rules grow. The better alternative is to use include directives instead. This way, you can create multiple configuration files containing different custom policies and rules.
Suppose you want to give a group of users to run specific networking commands as root. To do so, you would need to create a file in the /etc/sudoers.d directory containing the custom rules for that group.
1. First, create the group you want that will be the target of the custom rule. In this example, the group’s name is netadmin.
sudo addgroup netadmin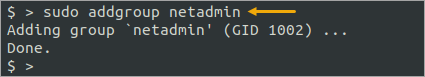
2. Next, create a regular user account and make it a member of the netadmin group.
sudo adduser ata
sudo usermod -aG netadmin ata
id ata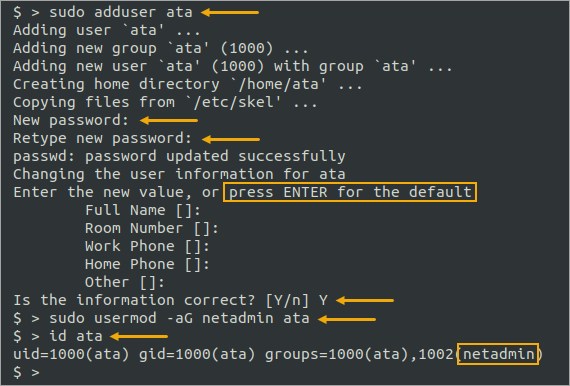
3. Now, create a new sudoers file called /etc/sudoers.d/networking and open it with visudo.
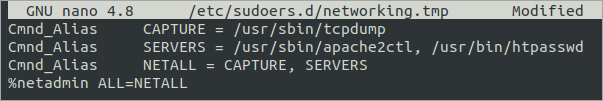
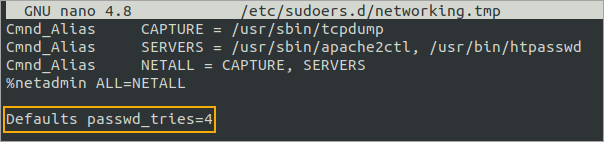
sudo visudo -f /etc/sudoers.d/networking4. Copy and paste the following lines into the networking file.
Cmnd_Alias CAPTURE = /usr/sbin/tcpdump
Cmnd_Alias SERVERS = /usr/sbin/apache2ctl, /usr/bin/htpasswd
Cmnd_Alias NETALL = CAPTURE, SERVERS
%netadmin ALL=NETALLThe Cmnd_Alias lines are creating aliases for the commands. In this example, you assign the alias CAPTURE for the tcpdump command and SERVERS for the apache2ctl and htpasswd commands. Think of these lines as grouping commands together and giving them a collective name.
The last line specifies that members of the netadmin group can run any command in the NETALL alias as root. This line must come after the Cmnd_Alias lines.
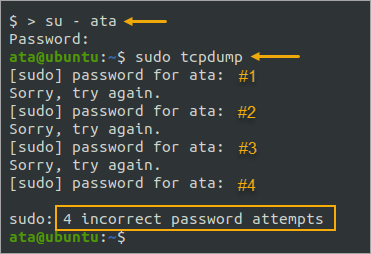
5. To test the ata account’s sudo privileges, switch to the ata user account.
su - ata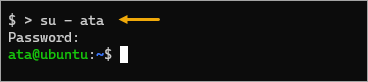
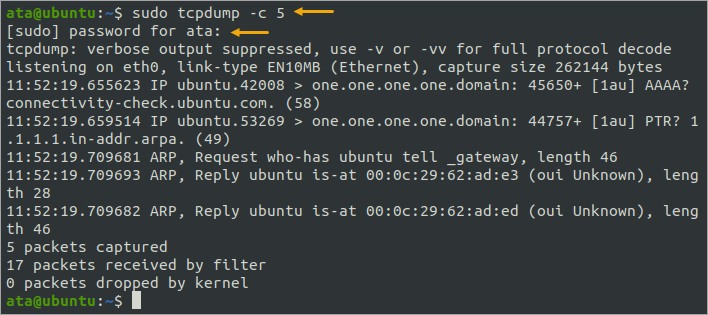
6. Now, run one of the commands that the user has sudo access, such as tcpdump.
sudo tcpdump -c 5As you can see below, the sudo command should work because the account has access to run it.
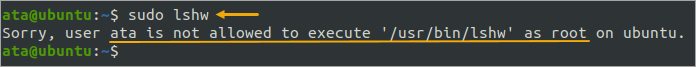
7. Next, test and confirm that the account cannot run any other commands that are not in the custom rule, like lshw.
sudo lshwAs a result, the sudo attempt fails because your account does not have the privilege to run the command as root.
8. Lastly, switch back to your account by running the below command.
exitHardening Security Using the passwd_tries Option
You can’t let anyone try entering a wrong password with sudo as often as they want—that would be an open invite for brute-force or password spraying attacks. As a preventive measure, you must set the maximum number of retries by adding the passwd_tries option inside the sudoers file.
1. First, open the custom sudoers file with visudo.
sudo visudo -f /etc/sudoers.d/networking2. Add the below line to the end of the sudoers file. This line will allow up to four incorrect sudo password attempts before preventing any more attempts.
Defaults passwd_tries=4The custom sudoers files should now look the same as the screenshot below. Ensure to save the file and exit the editor.
3. Now, switch to the ata user account and rerun the tcpdump command as root. But this time, enter an incorrect password until the password prompt ends.
sudo tcpdumpAfter your fourth attempt with a wrong password, you see that sudo stops you from entering another password for the fifth time.
Conclusion
In this tutorial, you learned the basics of the default sudoers file. You created custom rules in a separate sudoers file for granting custom privileges. Creating and applying custom rules is more secure than adding users to the sudo group.
You also learned how to apply the passwd_tries option to specify how many incorrect passwords attempts a user can make before sudo terminates the authentication attempt. You can increase granularly control which users have access to what commands.
Don’t stop here! You can do much more with the sudoers file, like adding a lecture file to spice up the user sudo experience. Thank you for reading, and have fun securing your Linux system!




