Using the ActiveDirectory PowerShell module, you can query AD groups with Get-AdGroup, add, update, and remove groups and group members. In this blog post, you’re going to learn a little about the Active Directory group PowerShell cmdlets with a ton of examples for reference.
Not a reader? Watch this related video tutorial!Active Directory Group Cmdlets
Once you install the ActiveDirectory PowerShell module, you’ll find a few cmdlets available to manage groups.
| Cmdlet Name | Description |
| Add-ADGroupMember | Used to add members to an AD group. |
| Add-ADPrincipalGroupMembership | Used to add an AD principal to AD groups. |
| Get-ADGroup | Used to return a group or groups from AD. |
| Get-ADGroupMember | Used to return the members of an AD group. |
| Get-ADPrincipalGroupMembership | Used to get the groups an AD principal is a member of. |
| New-ADGroup | Used to create a new AD group. |
| Remove-ADGroup | Used to delete an AD group. |
| Remove-ADGroupMember | Used to remove members from an AD group. |
| Remove-ADPrincipalGroupMembership | Used to remove an AD principal from AD groups. |
| Set-ADGroup | Used to set the properties of an AD group. |
Using these cmdlets and a little PowerShell kung-fu, you can manage every aspect of the Active Directory group with PowerShell.
Find the members of a group with Get-ADGroupMember
The Get-AdGroupMember cmdlet returns all members in a group.
PS51> Get-ADGroupMember -Identity <identity string or object>Alternatively, you could reference the memberOf property on a particular user using the Get-Aduser cmdlet. For a refresher on how to build filters, check out Learning Active Directory Directory and LDAP Filters in PowerShell.
Two examples are below.
PS51> Get-ADUser -Filter 'memberOf -eq ""'
PS51> Get-ADUser -LDAPFilter '(memberOf=)'This returns a collection of ADPrincipal objects.
Export the members of a group to a CSV file
This exports each users’ first name, surname and email address. Pipe the results fromGet-ADGroupMember to Get-ADUser because these are ADPrincipal objects that do not have all of the properties that ADUser objects have.
PS51> $GroupMembers = Get-ADGroupMember -Identity 'Professional Services Department'
PS51> $GroupMembers | Get-ADUser -Properties GivenName,Surname,Mail | Select-Object GivenName,Surname,Mail | Export-CSV -Path GroupMembers.CSV -NoTypeInformationNotice the use of the
NoTypeInformationparameter ofExport-CSVto ensure that the CSV file is compatible with other applications.
Find groups with no members with Get-ADGroup
Use Get-AdGroup to find groups using filters. Two examples below.
PS51> Get-ADGroup -Filter "Members -notlike '*'"
PS51> Get-ADGroup -LDAPFilter "(!(member=*))"Create a new security group with New-ADGroup
You create a new security group using the New-AdGroup command.
PS51> New-ADGroup -Name '<group name>' -GroupScope <scope of group> -Path '<path of the OU tht will host the new group>'If no Path parameter is supplied, the new group will be created in the Users container. The group scope must be either DomainLocal, Global or Universal.
Create a new distribution group with New-ADGroup
Use New-AdGroup again to create a distribution group. This time, choose a GroupCategory of Distribution.
PS51> New-ADGroup -Name '<group name>' -GroupScope <scope of group> -GroupCategory Distribution -Path '<path of the OU tht will host the new group>'Add members to a group with Add-ADGroupMember
Adding users to an Active Directory group with PowerShell can be done using the Add-AdGroupMember cmdlet or the Add-ADPrincipalGroupMembership cmdlet.
This command specifies the group as the Identity.
PS51> Add-ADGroupMember -Identity <identity string or object> -Members <identity string(s) or ADPrincipal(s)>This command specifies the AD principal as the Identity.
PS51> Add-ADPrincipalGroupMembership -Identity <identity string or object> -MemberOf <identity string(s) or ADGroup(s)>Write to the Notes property of a group with Set-AdGroup
The field labeled Notes in ADUC is represented by the Info property returned from Get-AdGroup.
First, find the group to change, set the Info property and then use Set-AdGroup to commit the change to AD.
PS51> $group = Get-ADGroup -Identity <identity string or object>
PS51> $group.Info = 'Important notes on this group'
PS51> Set-ADGroup $groupRemove group members with Remove-ADGroupMember
Like all PowerShell cmdlets, you can use the Confirm parameter to be prompted before a change is made. This behavior applies to the Remove-AdGroupMember and Remove-ADPrincipalGroupMembership cmdlets too.
Below you can remove group members with no confirmation.
PS51> Remove-ADGroupMember -Identity <identity string or object> -Members <identity string(s) or ADPrincipal(s)>
PS51> Remove-ADPrincipalGroupMembership -Identity <identity string or object> -MemberOf <identity string(s) or ADGroup(s)>Or you can choose to remove group members with confirmation using the Confirm parameter.
PS51> Remove-ADGroupMember -Identity <identity string or object> -Members <identity string(s) or ADPrincipal(s)> -Confirm
PS51> Remove-ADPrincipalGroupMembership -Identity <identity string or object> -MemberOf <identity string(s) or ADGroup(s)> -ConfirmDelete a group with Remove-ADGroup
Delete a group with no confirmation and with confirmation.
PS51> Remove-ADGroup -Identity <identity string or object>
PS51> Remove-ADGroup -Identity <identity string or object> -ConfirmRename a group with Rename-ADObject
You can rename a group via a one-liner using Rename-ADObject.
PS51> Rename-ADObject -Identity <identity string or object> -NewName '<new name>'Get the number of groups with Get-ADGroup
Do you need to find the total numbers of groups returned via Get-AdGroup? Use the Count property.
PS51> (Get-ADGroup -Filter '*').CountFind groups with a manager with Get-ADGroup
Filter all groups that have a manager assigned to them with Get-AdGroup and a well-crafted LDAP filter.
PS51> Get-ADGroup -LDAPFilter '(managedby=*)'There is no equivalent PowerShell filter for this.
Find groups managed by a specific user with Get-ADGroup
Up your filter skills and find all groups managed by a specific user using either a PowerShell filter or LDAP filter.
PS51> Get-ADGroup -Filter 'managedby -eq "<distinguished name of user>"'
PS51> Get-ADGroup -LDAPFilter '(managedby=<distinguished name of user>)'Set the group Manager with Set-ADGroup
The Managed By tab in ADUC for groups allows you to designate someone who is responsible for the membership of the group. This doesn’t automatically mean that the manager can alter the group membership of the group. For that to be possible, the security permissions need to be changed on the Member property for the group in question.
The act of ticking the Manager can update membership list box for a group in Active Directory Users and Computers (ADUC) changes the permissions to allow this.
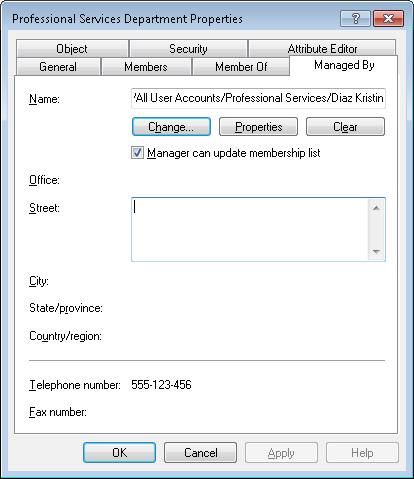
Use Set-ADGroup to set the ManagedBy attribute:
PS51> Set-ADGroup -ManagedBy '<distinguished name, GUID, SID or SAM Account name of manager>'Updating the Access Control list takes a few more steps. The following code snippet grants the user Kristin Diaz the ability to manage the membership of the group. bf9679c0-0de6-11d0-a285-00aa003049e2 is the GUID for the Member property of the group.
If Kristin is also set as the manager of the group then the tick box will be ticked. If not, Kristin will still be able to manage the membership of the group but will not be shown in ADUC as the manager.
Find leaked & unsafe passwords in your Active Directory by checking against the NCSC Password list.
$group = Get-ADGroup -Identity 'Professional Services Department'
$manager = Get-ADUser -Identity 'Kristin.Diaz'
$NTPrincipal = New-Object System.Security.Principal.NTAccount $manager.samAccountName
$objectGUID = New-Object GUID 'bf9679c0-0de6-11d0-a285-00aa003049e2'
$acl = Get-ACL "AD:$($group.distinguishedName)"
$ace = New-Object System.DirectoryServices.ActiveDirectoryAccessRule $NTPrincipal,'WriteProperty','Allow',$objectGUID
$acl.AddAccessRule($ace)
Set-ACL -AclObject $acl -Path "AD:$($group.distinguishedName)"Find all security groups
List all security groups in Active Directory with PowerShell by limiting your search query to only security groups with these two examples. What’s that LDAP filter, you ask? Learn all about LDAP filters.
PS51> Get-ADGroup -Filter 'groupcategory -eq "Security"'
PS51> Get-ADGroup -LDAPFilter '(groupType:1.2.840.113556.1.4.803:=2147483648)'Find Distribution groups
Use PowerShell to list Active Directory Groups (distribution) which excludes security groups using these two examples.
PS51> Get-ADGroup -Filter 'groupcategory -eq "Distribution"'
PS51> Get-ADGroup -LDAPFilter '(!(groupType:1.2.840.113556.1.4.803:=2147483648))'Find group membership for a user with Get-ADPrincipalGroupMembership
PS51> Get-ADPrincipalGroupMembership -Identity <identity string or object>Note that this command requires access to a global catalog.
Find groups in an OU, not including any sub-OUs
Get granular using the SearchBase parameter to limit your search to a single OU using these two examples.
PS51> Get-ADGroup -Filter '*' -SearchBase '<distinguished name of OU>' -SearchScope OneLevel
PS51> Get-ADGroup -LDAPFilter '(CN=*)' -SearchBase '<distinguished name of OU>' -SearchScope OneLevelFind groups in an OU, including any sub-OUs
Do you need to find all groups in child OUs? Use a SearchScope of SubTree.
PS51> Get-ADGroup -Filter '*' -SearchBase '<distinguished name of OU>' -SearchScope SubTree
PS51> Get-ADGroup -LDAPFilter '(CN=*)' -SearchBase '<distinguished name of OU>' -SearchScope SubTreeSummary
That concludes our example-driven demo of managing AD groups with PowerShell. Grab a few of these, try them out in your organization and start automating!




