A prerequisite for every PowerShell Active Directory (AD) task is to import the PowerShell Active Directory module. This popular module allows administrators to query and make changes to Active Directory with PowerShell.
Scan Your AD for 930+ Million Compromised Passwords. Download Specops Password Auditor, a FREE read only tool that identifies password-related vulnerabilities.
In this blog post, we’re going to dive into how to install the PowerShell Active Directory module on Windows 10. We’ll then cover how to connect to AD with PowerShell and go into the various ways you can authenticate to AD.
Install RSAT (Remote Server Administration Tools)
Before we begin, you should first be aware of the RSAT package. If you are using a workstation variant of Windows then you will need to install the Remote Server Administration Tools (RSAT) package. When using a Server variant of Windows, RSAT is available already.
Without RSAT you’ll get the annoying ‘the term Get-AD* is not recognized as the name of a cmdlet, function, script file, or operable program’ type messages when you attempt to run the commands we’ll be covering.
RSAT for Pre 1809 Windows 10
Download an RSAT package if you’re on Windows 10 pre-build 1809 from Microsoft. The install is simple and straightforward.
Learn how to find your Windows 10 build version here if you don’t know how.
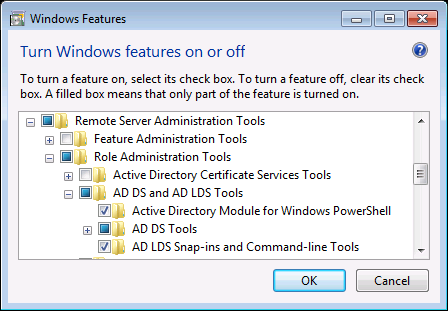
Once you have installed RSAT, ensure the Active Directory Module for Windows PowerShell is enabled in Windows Features. By default, it should be already.
RSAT for post-1809 Windows 10
In versions of Windows from 1809 onwards the RSAT capabilities are available as optional features. There’s no need to download an external package.
To import the PowerShell Active Directory module, you must first install it. On Windows 10 post-1809, use the Add-WindowsCapability cmdlet. This enables the Rsat.ActiveDirectory.DS-LDS.Tools optional feature as shown below.
PS51> Add-WindowsCapability -Online -Name Rsat.ActiveDirectory.DS-LDS.Tools~~~~0.0.1.0The above syntax was tested on Windows 10 Build 1903 and on Windows 7.
RSAT for Windows Server 2008R2 and Later
On Windows Server, use the PowerShell ServerManager module to enable the RSAT-AD-PowerShell feature in PowerShell.
PS51> Import-Module ServerManager
PS51> Install-WindowsFeature -Name RSAT-AD-PowerShellImport the PowerShell Active Directory Module
It’s likely PowerShell will auto-import the module when installed. But if you’d like to ensure it loads properly, you can also use the Import-Module command.
To import the PowerShell Active Directory module, run Import-Module ActiveDirectory. If the module is installed in the right place, you will receive no errors.
Connecting and Authenticating
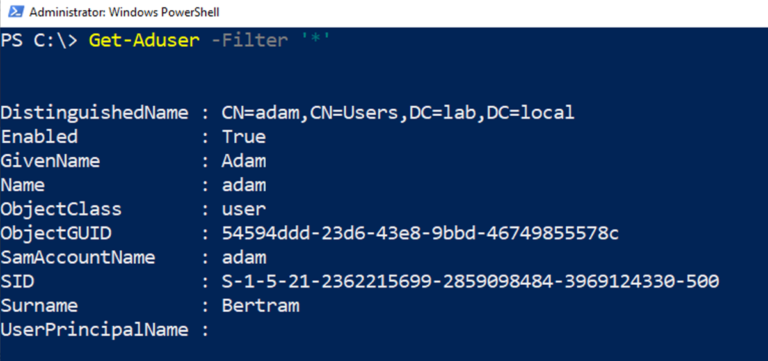
Once the ActiveDirectory module is set up, you can then use the Active Directory PowerShell cmdlets.
Although the cmdlets interact with different parts of AD, nearly all of them have common parameters. Two of those parameters are Server and Credential.
Connecting to a Specific Active Directory Domain Controller
By default, the AD cmdlets will find a domain controller for you. However, if you need to connect to a different domain controller, you can use the Server parameter.
The Server parameter isn’t mandatory. PowerShell will attempt to find a domain controller to connect to by default. The domain controller is determined by trying the following in the listed order:
- Use the
Serverproperty of objects passed in on the pipeline. - Use the server associated with the AD PowerShell provider drive, if in use.
- Use the domain of the client computer.
You can connect to a specific domain controller by providing a value for the Server parameter. You can specify several different ADDS objects in different formats such as:
- FQDN or NETBIOS name such as domain.local or DOMAIN which will be the domain name specified
- FQDN or NETBIOS name such as server.domain.local or SERVER that will be the domain controller.
- A fully-qualified domain controller and port such as server.domain.local:3268
Connecting to Active Directory with Alternate Credentials
By default, the Active Directory PowerShell cmdlets will use a two-step process for determining the user account to connect to AD.
- Use the credentials associated with the PowerShell AD provider drive, if the command is run from there.
- Utilizing the credentials of the logged-on user.
You can also specify alternate credentials using the Credential parameter.
The Credential parameter allows you to pass in a PSCredential object. If you provide a username, you will be prompted for a password and these credentials will be used.
You can see an example below of using the Get-AdUser cmdlet using an alternate credential.
PS51> $credential = Get-Credential
PS51> Get-Aduser -Filter * -Credential $credentialAre there compromised passwords in your Active Directory? Download Specops Password Auditor and scan for free.
You also have two possible authentication types available, controlled by the AuthType parameter. These types are Negotiate (the default) and Basic. Basic authentication is only possible over an SSL connection.
PS51> Get-Aduser -Filter * -Credential $credential -AuthType Negotiate|BasicSummary
To import the PowerShell Active Directory module is a straightforward and common process. Using the instructions provided in this article, you should be well on your way to automating all the Active Directory things!