Welcome back to ATA’s Learn with Me series on securely managing Active Directory (AD) passwords with Specops! If you missed the previous posts, be sure to catch up here. Today, we’re going to cover enforcing AD password best practices using Specops’ Password Auditor tool.
Until the industry gets around to removing passwords for good, users will continue to provide their username and password to log into their AD domain-joined computers. And sysadmins and InfoSec professionals will continue to worry about maintaining that balance between convenience and security.
Ensuring secure passwords for all sensitive AD accounts is a major struggle for many organizations. That struggle only elevates as an organization grows. Users consistently write their passwords on sticky notes and keep their passwords written down in ‘password journals.’
If a domain admin password isn’t written in clear text in Joe, HR Director’s password book, a user may be using that same password across other online services. No matter how secure your AD passwords are, if that same password is compromised from an attack on a more vulnerable service, attackers have a big advantage coming into your organization.
Password Auditing To Stay in the Know
One of the best ways to ensure your AD passwords stay secure is enforcing strict password policies and consistent password auditing. Password policies limit insecure passwords while periodic auditing ensures the policies work as expected and can also compare your AD passwords against lists of known-compromised passwords.
Through my first-time experience with Specops’ Password Auditor tool, I’ve discovered that this tool not only scans and provides information about problematic password policies but can also compare known-compromised passwords with your AD passwords.
Password Auditor has both free and paid features. In this article, all features I cover are completely free.
Through its support of the National Cyber Security Centre (NCSC)’s compromised password list along with other sources, this tool looks like a great resource to help secure AD passwords!
If you prefer a screencast-based approach to getting to know Password Auditor, check out the video below.
Setting Up Specops’ Password Auditor Tool
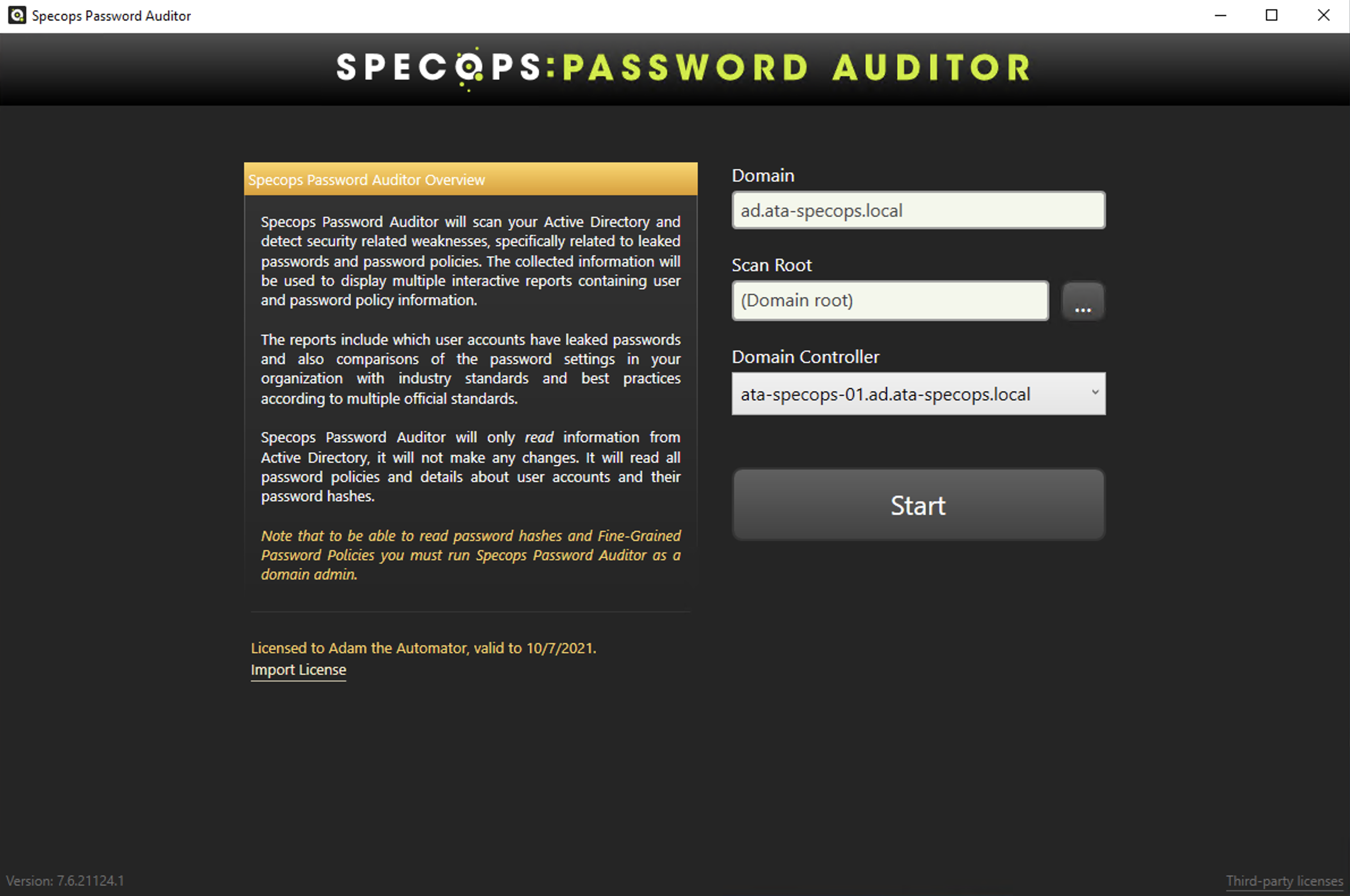
One thing I like about Password Auditor is its simplicity. For example, below is the first screen you see when opening the tool. You can’t beat a one-button page! Since I’m running this tool on my lab domain controller, it automatically picks up the domain and the domain controller I’m running it on.
I’ll click Start and see what happens.
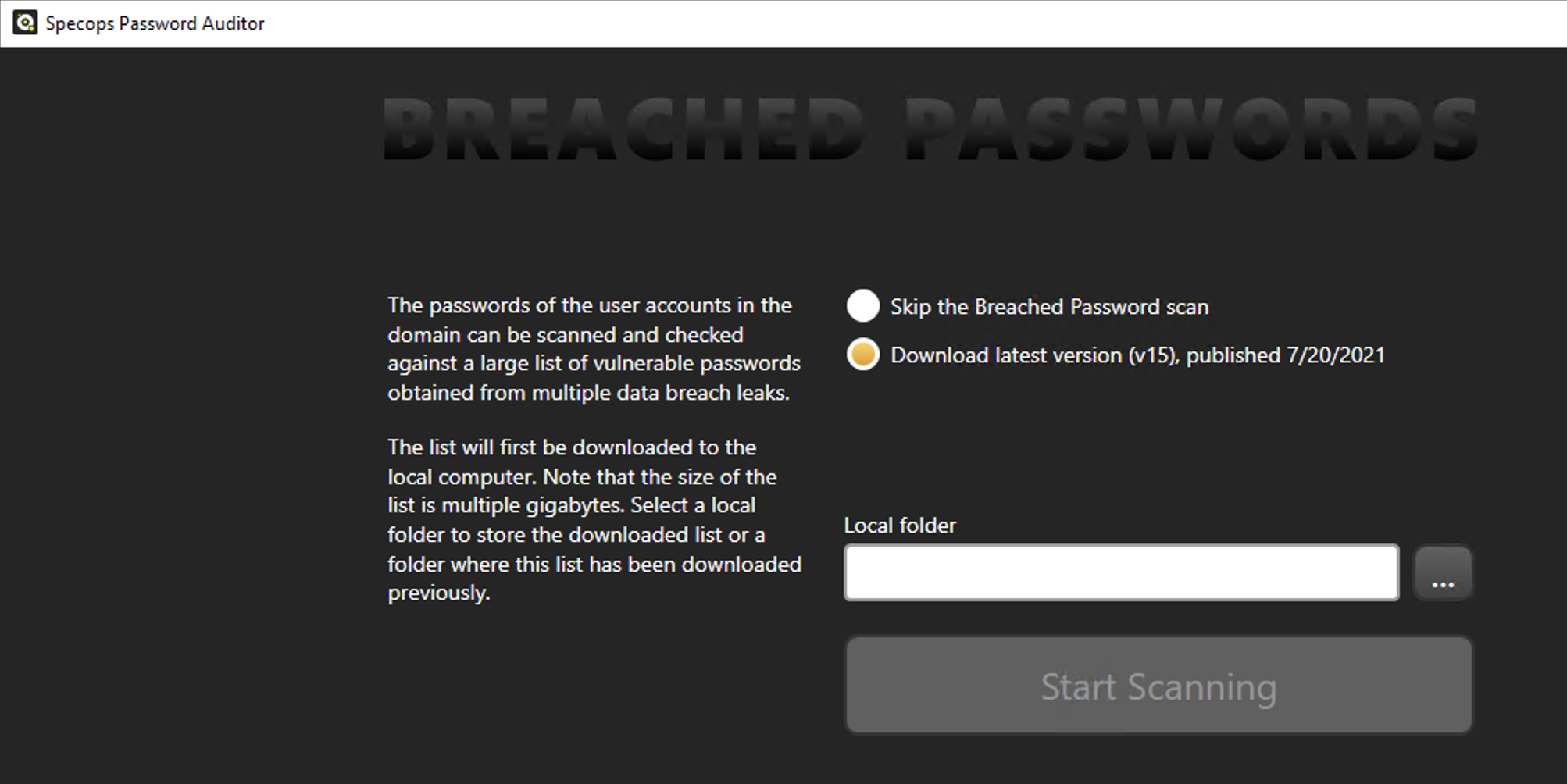
On the next screen, I can automatically download the latest list of breached passwords. These passwords are obtained from NCSC’s large password list and other sources. I’ll choose to download the list of files, provide a folder to download the passwords and click Start Scanning.
One of the Password Auditor’s most useful features is its ability to compare known-breached passwords against your AD passwords and provide a report.
Scanning Active Directory for Password Issues
Once I got through the initial setup screens, Password Auditor immediately begins scanning AD. You’ll see below it:
- Pulls together all user accounts.
- Reads all password policies
- Discovers the password policies that apply to those users
- Downloads the current breached password lists.
Ensure you have at least 5GB of space on the drive you download the passwords to. Password Auditor downloads many .bin files in that folder.
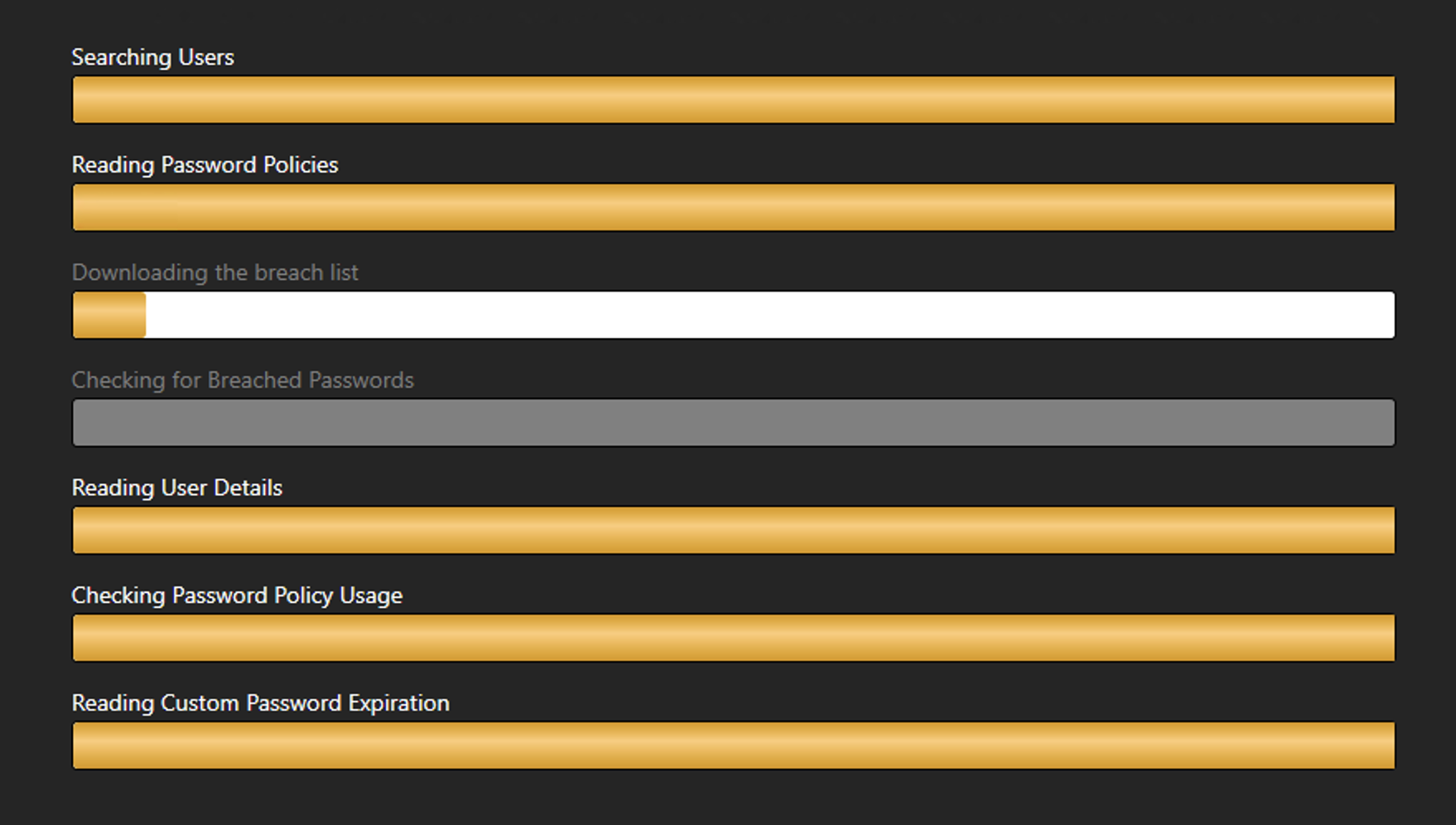
The total scan and breach list download will take a few minutes, depending on the size of your AD environment and the bandwidth speed of your Internet connection.
Inspecting Scan Results
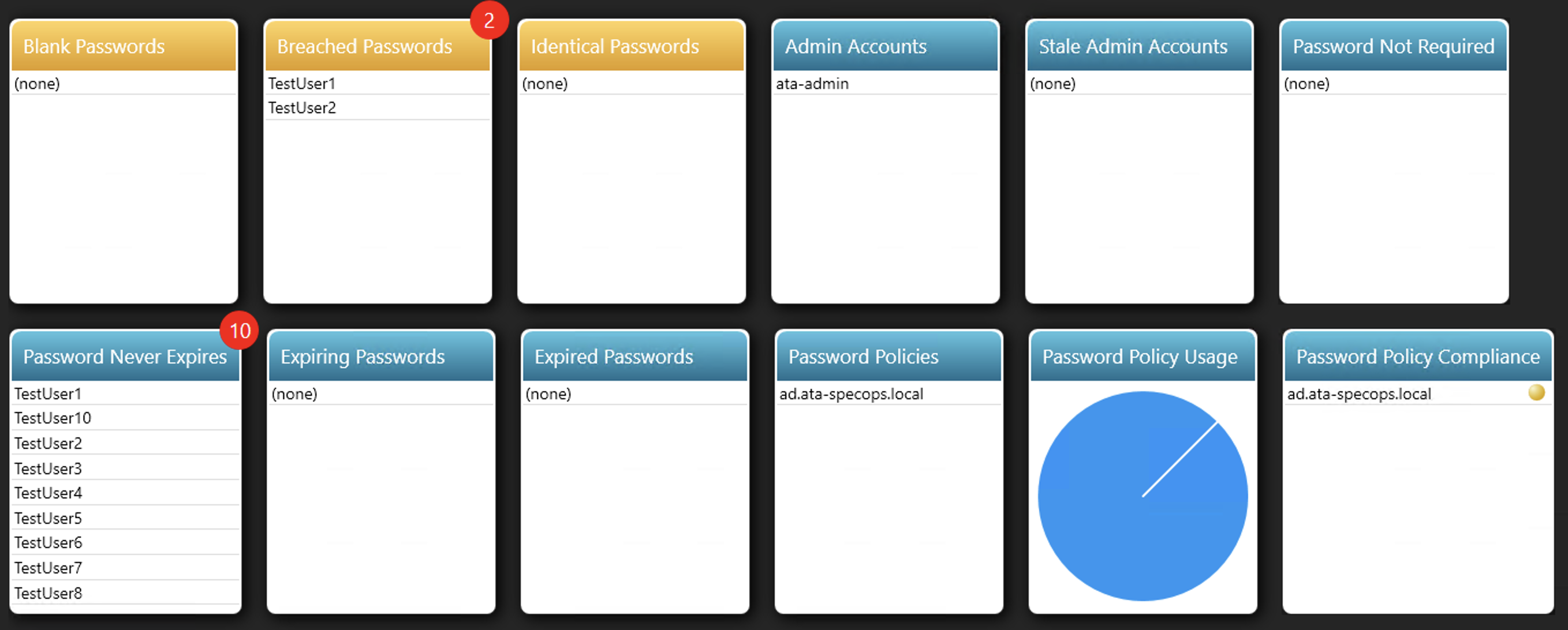
When scanning is complete, you’ll see a screen grouped by the various tests Password Auditor performed. You’ll see in the screenshot below that two of my user accounts are currently using passwords found to be on a breached password list. I also see that 10 of my accounts have accounts that do not expire.
From what I’ve seen so far, I like that Specops tools aren’t bloated with a complex interface. Each tool serves one purpose and doesn’t include features that no one uses.
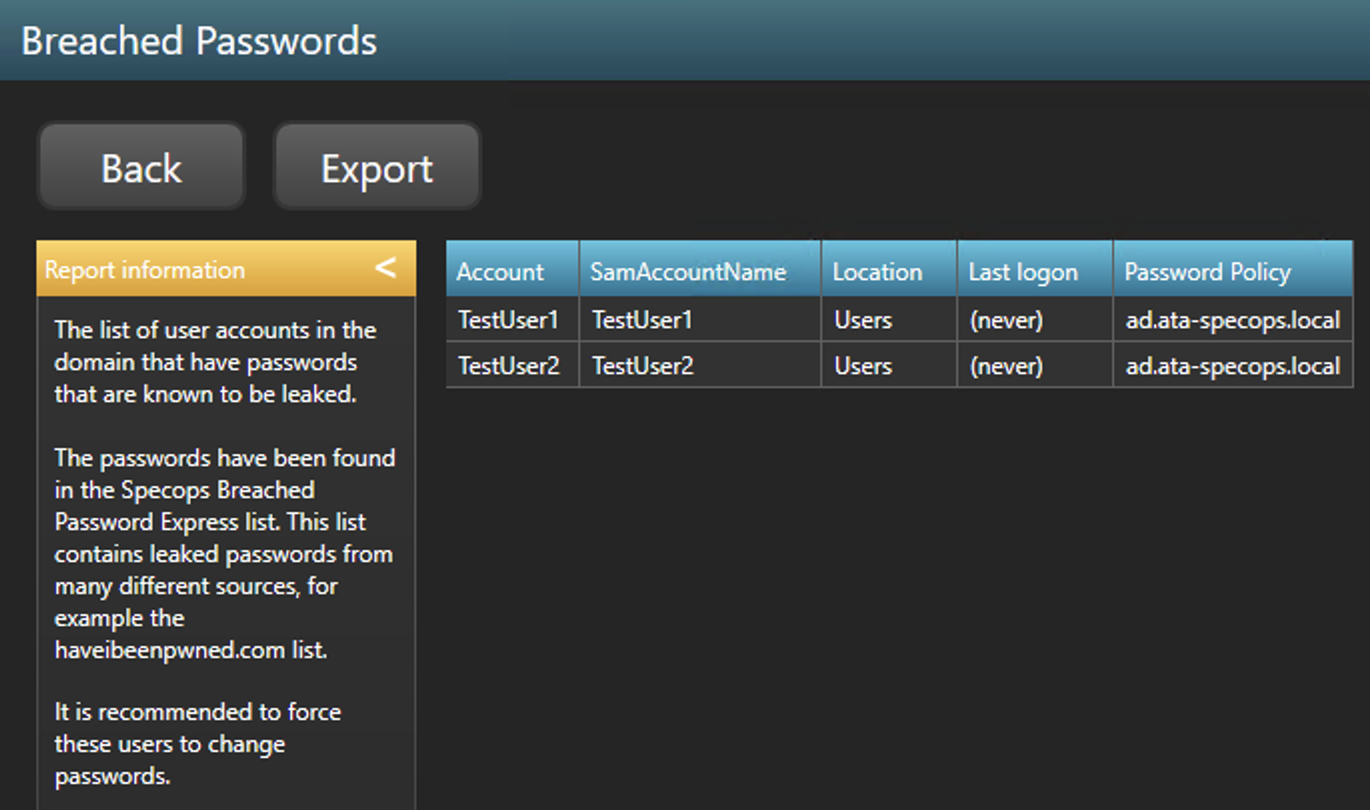
Breached Passwords
I can then click into each of the groups to drill down for more information. For example, you’ll see that the users using the breached passwords are in my Users AD container, they’ve never logged in, and the default domain policy currently applies to them.
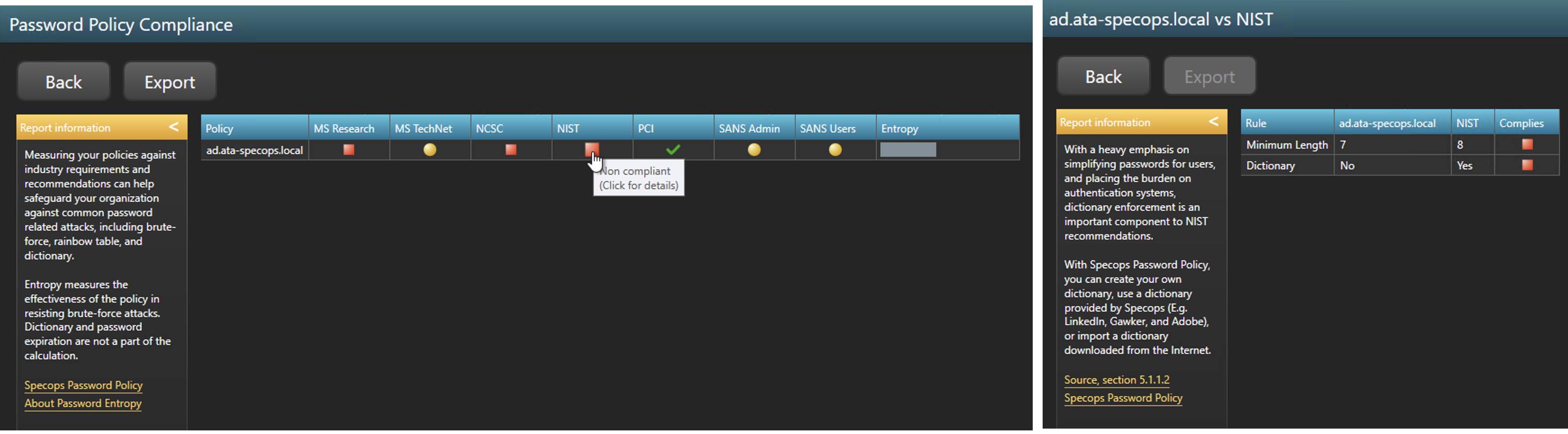
Password Policy Compliance
The Password Policy Compliance report was another interesting report I found. You’ll see below that for every password policy in AD, Password Auditor compares it with industry-standard security practices. By clicking on an organization, you can then see exactly where you’re out of compliance.
Unlike what I originally thought, Password Auditor doesn’t just scan AD for weak passwords. It reaches out to many different places and offers suggestions for improvement. This tool is great for taking snapshots for management, auditors, or simply measuring efficacy of password security initiatives.
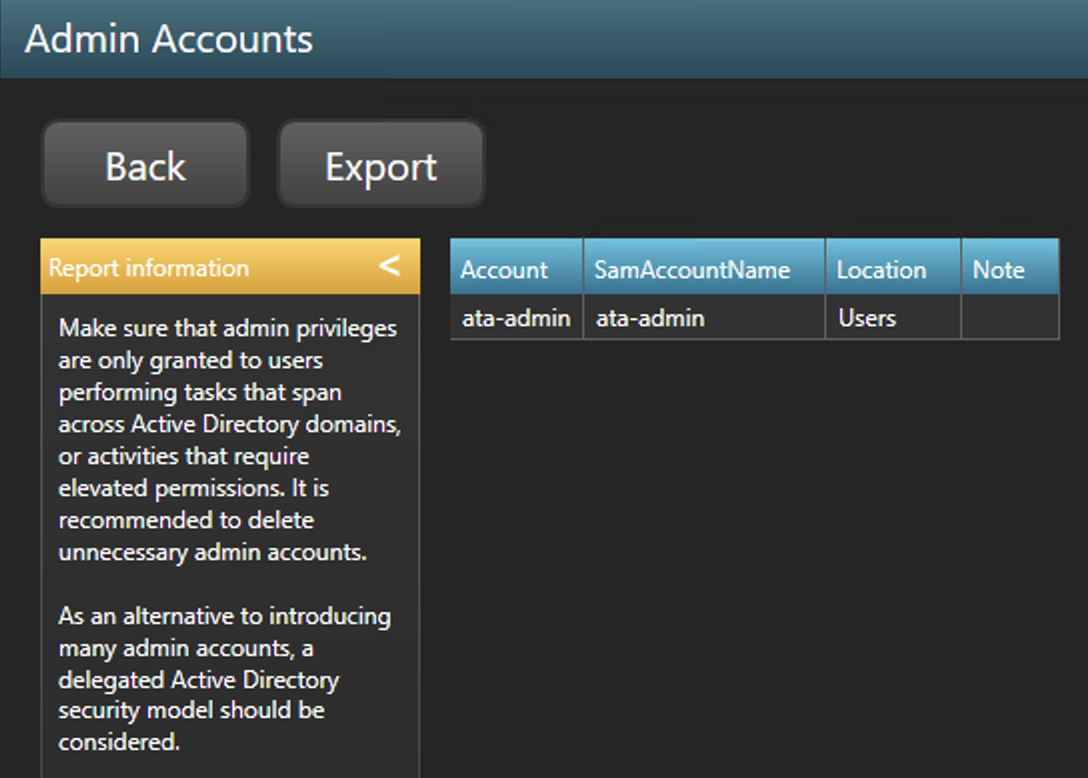
Admin Accounts
Coming from an organization with too many admin accounts, the Admin Accounts report sure would have come in handy. You must ensure that a limited number of admin accounts exist in AD. You should never provide more permissions than what a user requires (least privilege).
You can see below by drilling into the Admin Accounts report, Password Auditor provides a list of each user account with a high privilege.
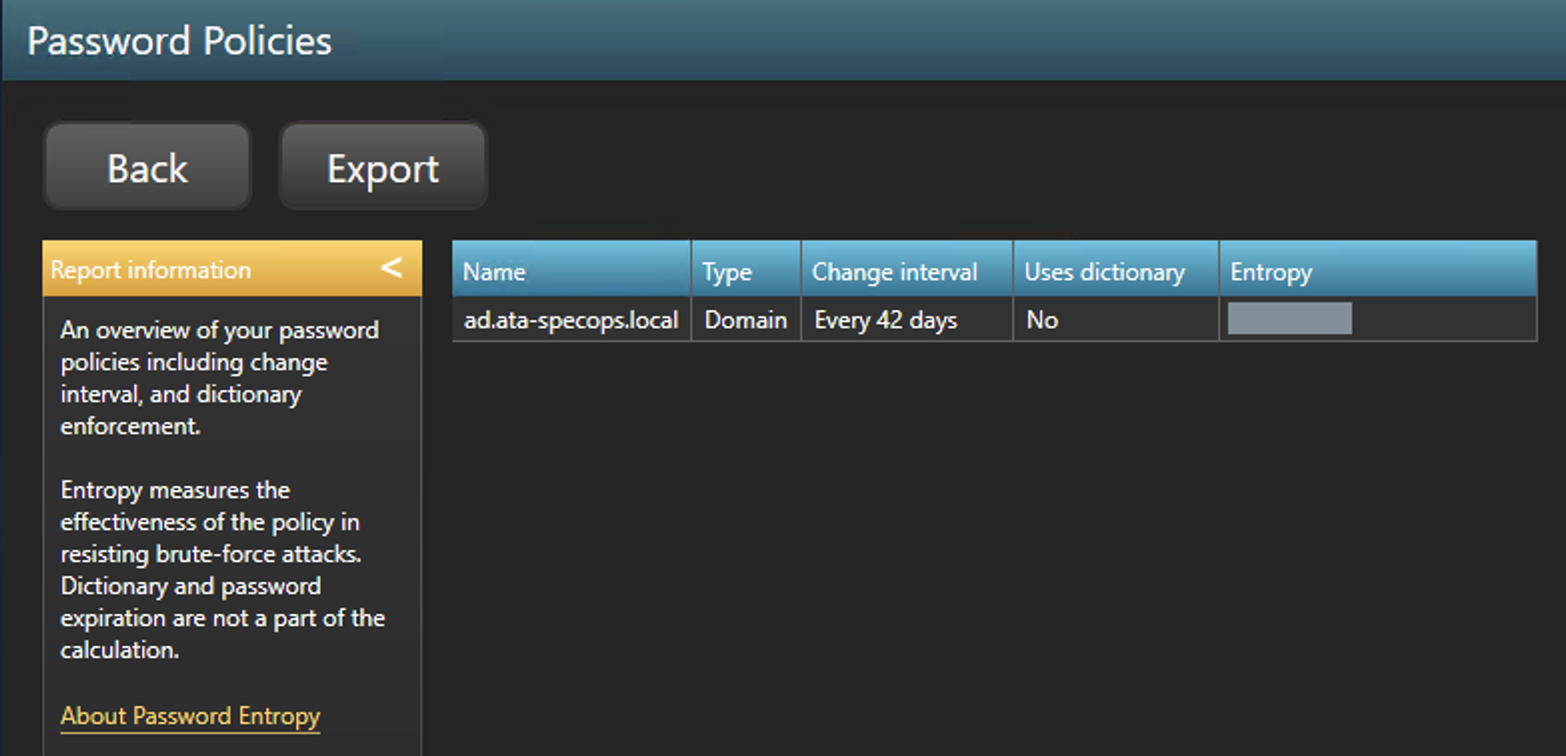
Password Policies
Another interesting report you’ll find in Password Auditor is on password policies. Password Auditor reads all domain policies (even fine-grained password policies) and inspects them when performing a scan. You can see below that it tells you:
- How often does the policy forces password changes
- If it prevents certain passwords via a dictionary
- How easy it is for an attacker to guess a password managed by the policy via password entropy.
Password entropy is a neat concept this tool is using. This metric displayed with a “strength bar” measures how long it would take for an attacker to guess the password.
Exporting Scan Results to a Report
One of Password Auditor’s hidden gems, though, is the PDF report. Click on Get PDF Report, and you’re presented with a professional-looking report of every password security issue found in the scan. You can find the report that I ran here.
SpecopsPasswordAuditorReport_8212021_447PM.pdf
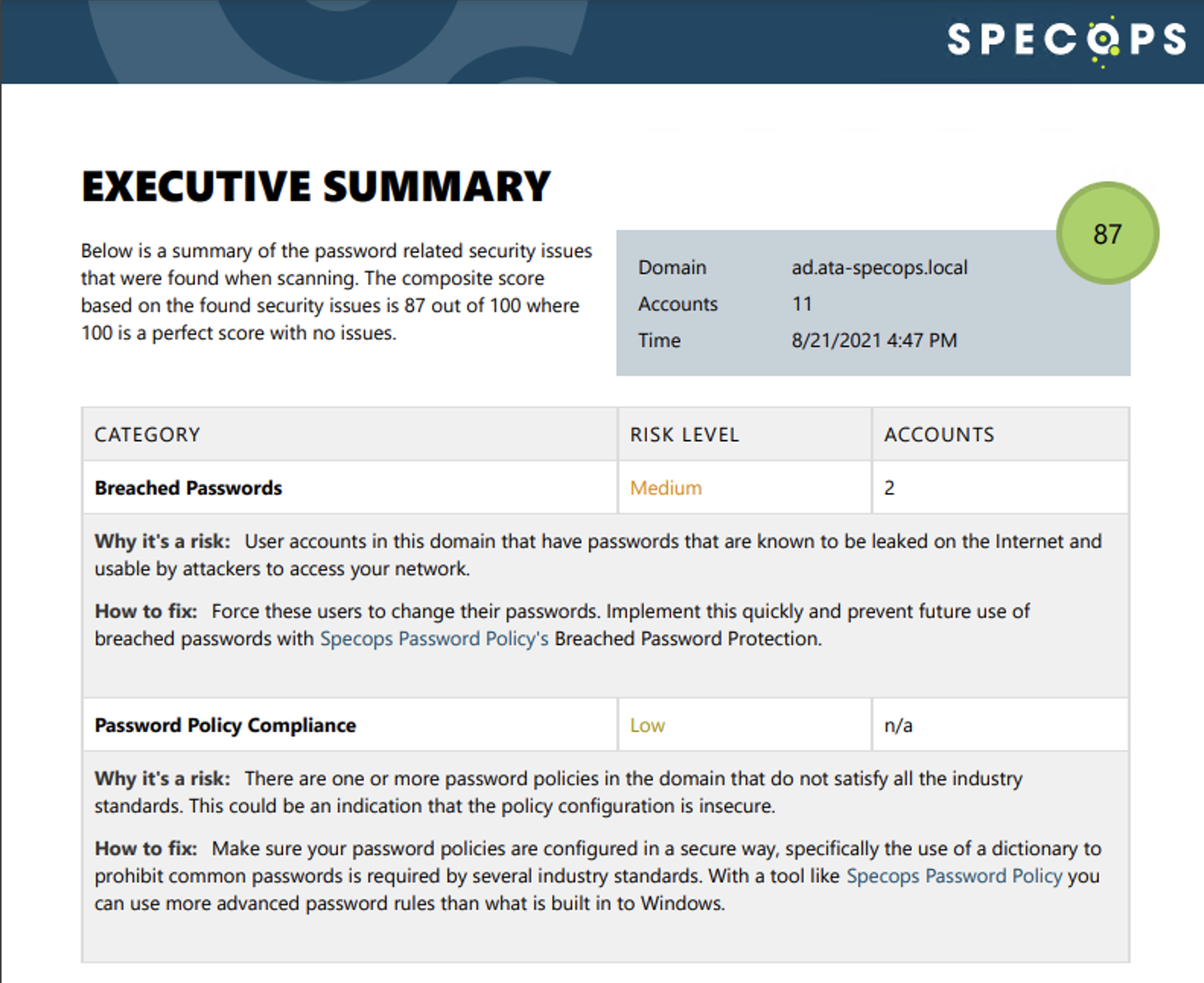
To be honest, I wasn’t expecting such a professional-looking, complete report. The kind of data that Password Auditor pulls and the report that it generates from that data could rival much more expensive software.
Conclusion
Specops’ Password Auditor is a simple yet effective tool in collecting data about your AD passwords. The tool’s interface is simple and, at first, leads you to believe there’s not much value here. But as soon as I saw the PDF export, the value clicked for me.
Password Auditor isn’t just a simple, little password scanner. This tool provides useful information not only from AD but by pulling from other industry-standard sources and comparing that information with AD. Better yet, it provides the details and actions necessary actually to fix the issues it finds.




