Redis is beneficial for many things, one of which is caching. You can also use Redis as a primary data store or even as a replacement for a database. But how do you execute a secure Redis install? Installing Redis can be a pain, and if you’re not careful, you could end up with many errors. Lucky for you, this tutorial has got you covered.
In this tutorial, you’ll learn how to securely install Redis on your Linux system, along with some tips to avoid common mistakes.
Read on and save yourself the headaches from troubleshooting Redis installation errors!
Prerequisites
This tutorial will be a hands-on demonstration. If you’d like to follow along, be sure you have the following:
- An Ubuntu 20.04 LTS machine – This tutorial uses Ubuntu 20.04 LTS, but the instructions are similar for most Linux distributions.
Redis Install with the APT Package Manager
There are a few ways to install Redis on Ubuntu, but for this tutorial, you’ll go with the APT package manager to install Redis.
Redis is written in C, so you’d need to compile Redis from its source code manually. Several dependencies would need to be installed, and the build process isn’t exactly foolproof.
Compiling Redis from source isn’t recommended, but the upside is that you can customize your installation if you like. You download the source code, then manually configure it.
Open your terminal and run the apt update command below to ensure you have the latest package lists.
sudo apt update -y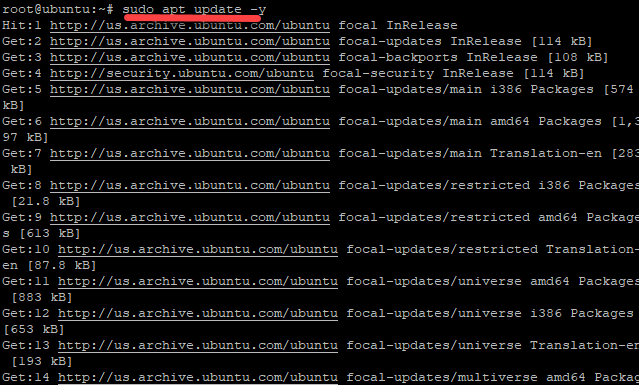
Now, run the apt install command below to install Redis on your machine.
The below command uses the apt package manager to download and install the redis-server package from the Ubuntu repositories onto your machine. The -y flag tells apt to accept prompts during the installation process automatically.
sudo apt install redis-server -y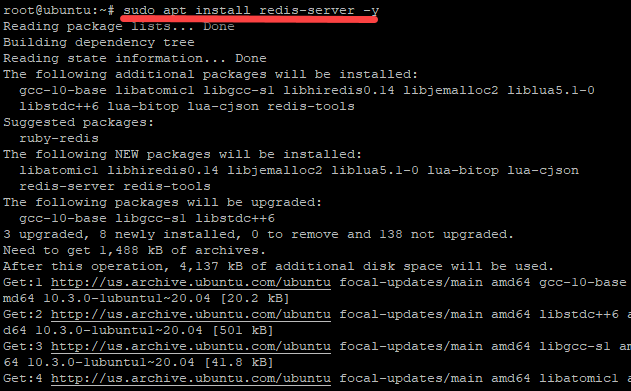
Configuring the Redis.conf File to Run Redis as a Service
You’ve just installed Redis, but it’s not ready for use yet. Before you can start using Redis, you’ll first configure the redis.conf file.
The redis.conf configuration file is included with the Redis package you installed and is stored in the /etc/redis/ directory by default. This file contains all of the configuration options for Redis.
The .conf file extension is logical, as it follows a conventional pattern. Many other programs use this same style. The Apache web server, for example, uses the .conf file extension for its main configuration file.
1. Run the following systemctl command to stop the redis-server service. Stopping the Redis service from running is a recommended practice when you’re first getting started with Redis.
sudo systemctl stop redis.service2. Next, open the /etc/redis/redis.conf file in your preferred text editor.
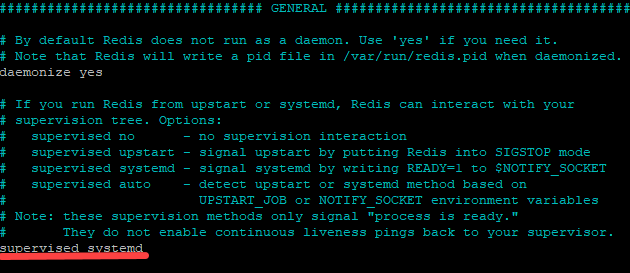
Find the supervised directive, then set it to systemd, as shown below, and save the changes. Doing so tells the operating system to run Redis as a service.
3. Now, run the systemctl restart command below to restart the Redis service (redis.service) since the Redis service doesn’t know about the changes yet.
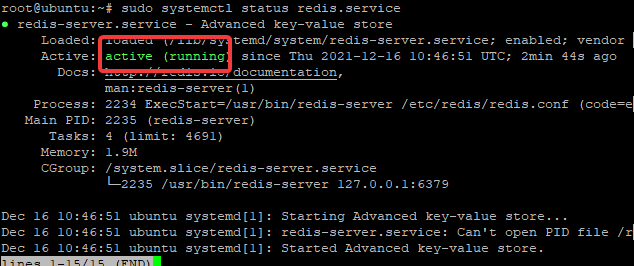
sudo systemctl restart redis.service4. Finally, run the systemctl status command below to see if Redis is running.
sudo systemctl status redis.serviceAs you can see below, the output shows that the Redis service is running.
Testing if the Redis Server Functions Properly
You’ve configured and verified that the Redis service is actively running, but that doesn’t mean the Redis server is working. How to test if the Redis server functions properly? Connect to the Redis server and send commands to see if the server responds.
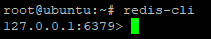
1. Run the redis-cli command below to connect to the Redis server. redis-cli is the command-line interface for Redis, which allows you to send commands to the server and inspect its state.
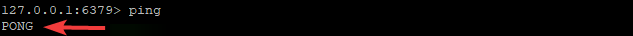
redis-cliBelow, you can tell that you’re in the Redis server prompt (127.0.0.1:6379>). The redis-cli command tries to connect to a Redis server at 127.0.0.1:6379 by default.
2. Next, run the ping command below to check if the Redis server is reachable.
pingAs you can see, the server returned PONG, which indicates the Redis server is reachable and can now successfully communicate with the service.
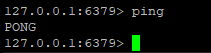
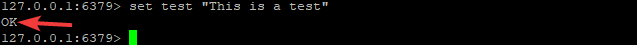
Perhaps you’re still skeptical; run the set command below. The set command is a Redis command that sets a key-value pair in a database.
set test "This is a test"As you can see, the set command returns “OK,” which indicates that the Redis service is working correctly.
3. Run the exit command below to exit the redis-cli. Doing so closes the connection to the Redis server.
exitBinding the Redis Server to Localhost
You’ve just tested that the Redis server works properly, but it might be accessible from other devices on your network too. This behavior is undesirable, and you’d typically want to protect your Redis server from strangers.
Binding the Redis server to localhost sets a behavior that only the machine on which you installed Redis can access the Redis server.
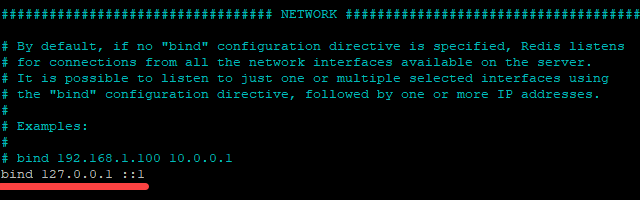
1. Open the /etc/redis/redis.conf file in your text editor.
2. Locate the line that says bind 127.0.0.1 ::1 and uncomment the line by deleting the number sign (#) at the beginning of the line.
3. Now, run the command below to restart the redis-server service.
sudo systemctl restart redis-server4. Finally, run the following command to check if your Redis server is bound to localhost. The netstat -lnp command lists all active network connections, and the grep redis part filters the output to lines that contain “redis.”
-lnp stands for Local Name Protocol, a networking protocol used by UNIX-like systems to resolve hostnames to IP addresses.
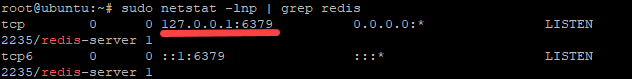
sudo netstat -lnp | grep redisYou can see below that the Redis server is now listening on the localhost interface only (127.0.0.1:6379). Reflecting the change in the configuration file, you can see that only the localhost interface is listed under your active internet connections (tcp).
Now, no other devices on your network can connect to your Redis server.
Securing Redis Server Connection with a Password
At this point, Redis isn’t set to require users to authenticate with a password. Anyone who knows your Redis server’s IP address or hostname could connect to it and change its data.
How do you protect your Redis server? Set a password to require users for authentication when connecting to your Redis server.
1. Re-open the redis.conf configuration file in your text/code editor.
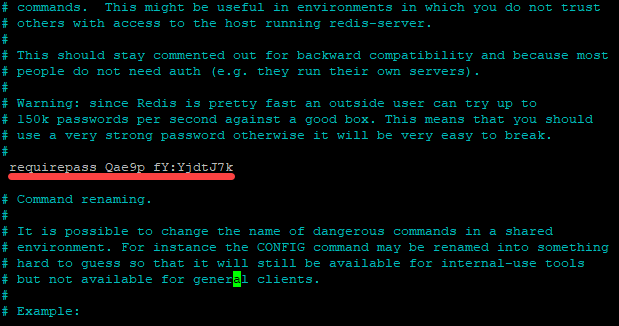
2. Next, set a strong password with the following:
- Look for
requirepass foobaredunder theSECURITYsection - Delete the number sign (
#) at the beginning of the line - Replace
foobaredwith a strong password of your choice and save the changes
3. Run the following commands to restart and connect to your Redis server.
sudo systemctl restart redis-server
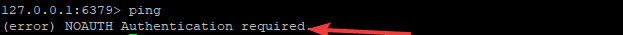
redis-cli4. Now, run the ping command to see if you’ll get a response from the server.
pingBelow, you can see an error message that says NOAUTH Authentication required. This message indicates that you need an authentication password to access your Redis server remotely.
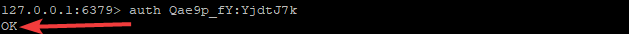
5. Run the below auth command followed by your password to authenticate your connection to your Redis server.
auth Qae9p_fY:YjdtJ7kYou will get an OK response when authentication is successful, like the one below.
6. Finally, rerun the ping command to test if you’ve authenticated your connection to your Redis server.
pingYou’ll now get the PONG response, as shown below, after authenticating your connection. At this point, you have now successfully protected your Redis server with a password.
Disabling Dangerous Commands to Protect your Redis Server
Setting a password to authenticate the connection to your Redis server doesn’t mean it gets 100% protection. By default, Redis includes several dangerous commands that allow users to change the data in your database.
When run by unauthorized users, these commands allow intruders to read, modify, destroy, and even wipe out the data of your Redis database.
Below is not a comprehensive list as your Redis server may have additional dangerous commands, but in most cases, these are the dangerous commands:
FLUSHDB, FLUSHALL, KEYS, PEXPIRE, DEL, CONFIG, SHUTDOWN, BGREWRITEAOF
BGSAVE, SAVE, SPOP, SREM, RENAME, DEBUG, EVALTo further secure your Redis server, rename these dangerous commands in the redis.conf file:
1. Open the redis.conf file in your text editor and look for the Command renaming section.
Rename commands to an empty string to disable them following the below syntax. Replace the-command with the actual command to disable.
rename-command the-command ""For example, disable the CONFIG command by renaming CONFIG to an empty string, as shown below, then save the changes. The double quotes (“”) indicate an empty string that signifies disabling a command.
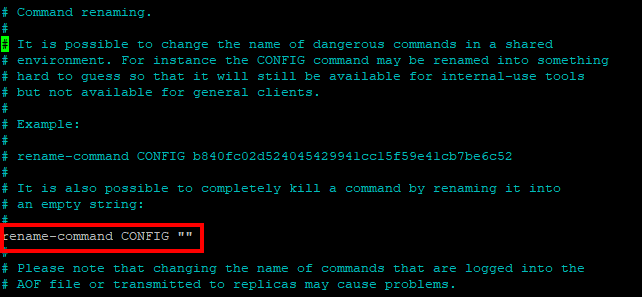
CONFIG command 2. Exit from the text editor and run the command below to restart the Redis server.
sudo systemctl restart redis-server3. Now run the following commands to connect to your Redis server.
redis-cli
auth Qae9p_fY:YjdtJ7k4. Finally, run the config get command to test that the CONFIG command is disabled.
config get requirepassYou will get an ERR unknown command config response, as shown below, which indicates that the CONFIG command is disabled.
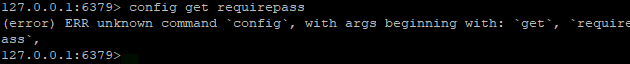
CONFIG command If the config get requirepass command pushes through, it requests your Redis server for the password to authenticate the connection to your Redis server.
You have now successfully renamed a dangerous Redis command to protect your Redis server. Now keep disabling other dangerous commands in the redis.conf file.
Blocking Connection Request to Redis Server with a Firewall
Another way to secure your Redis server is to set up a firewall. Setting up a firewall requires you to allow only the required port for each of the services running on your server.
For example, if you are running Redis on your server at port 6379, then that port is what you only need to open. If you need to allow access from a specific IP address or range of addresses, you can add those addresses to the firewall rules.
To set up a firewall, you’ll first install a firewall configuration tool. This example uses UFW, a commonly used firewall configuration tool on Linux. But you can also use another tool, such as iptables, to set up a firewall.
1. Run the following command to install UFW on your machine.
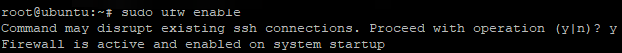
sudo apt install ufw -y2. Next, run the below command to enable UFW.
sudo ufw enableEnter ‘Y’ when you get the prompt shown below to continue running the command.
3. Run the ufw command below to add a rule, which allows (allow) traffic on port 6379 for your Redis server. Replace the 11.22.33.44 IP address with the IP addresses of your intended users.
sudo ufw allow from 11.22.33.44 to any port 6379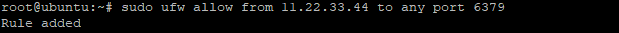
6379 4. Lastly, run the command below to verify that you’ve added the firewall rule successfully. The command checks the status of your firewall.
sudo ufw statusYou can see in the output below that the firewall is active and has the rule to allow traffic on port 6379 for Redis from the IP address 11.22.33.44.
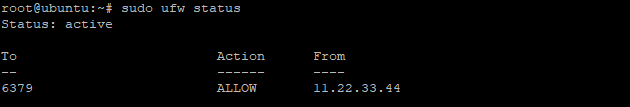
Now, any users with the IP address of 11.22.33.44 can connect to Redis via port 6379 and will need to authenticate with a password. You can add additional ports for other services in a similar fashion.
Conclusion
Throughout this tutorial, you’ve learned how to install and secure your Redis server by renaming dangerous commands to empty strings and setting up a firewall.
With this newfound knowledge, you can enjoy the full benefits of Redis without worrying about exposing your server to unnecessary risks.
Wish to learn more? Why not start with securing a Redis server in Kubernetes?




