If you have hundreds or thousands of user accounts in your Active Directory (AD), how do you find out which users have weak passwords or, worse, breached passwords? After scouring the internet for tools and scripts, you soon discover that they’re not the password audit tool you needed.
Before you get to the point of desperation and start creating your own tool, why not give Specops Password Auditor a try? This tool scans your AD for password-related vulnerabilities and produces reports that will help you drill down on identified risks.
This product review will cover the main functions of Password Auditor, from scanning the AD to exporting reports. By the end of this review, I will answer what you’re probably itching to know – is Specops Password Auditor any good? Let’s find out!
Scripting Is Great, But Not All The Time
For Windows admins, firing up PowerShell and writing scripts is second nature when they need to solve admin problems, much like muscle reflex. But, sadly, considering the type of password reports to generate, creating a script would be inefficient, and the outcome would be limited at best.
Surely you can pull information like password expiration and last password change time from the AD. But unless you have a free database of breached passwords lying around, how would your script audit the breached passwords? Or compare password compliance to industry standards?
Let’s admit it. Scripting is great most of the time, but not all of the time, and certainly not for everything.
Getting Started
The first time you start Specops Password Auditor, you’ll notice the minimalist interface. You’ll see three input boxes that clearly define what the tool expects you to provide.
- Domain – Specify the Active Directory domain to scan.
- Scan Root – Where you select the scope of the scan. You can select the domain root or a specific organizational unit (OU) only. The ability to limit the scope to specific OUs may come in handy if you only want to audit specific groups of users.
- Domain Controller – Specify which domain controller (DC) the tool will scan. Preferably, you’d choose a DC that’s local or within the same network.
And there’s the big Start button. This interface is not allowing you to confuse yourself. It’s intuitive and clear.
You’ll also appreciate the Overview section to the left, which gives you the low-down of what the tool will do (and what it won’t do). Not everyone reads the manual, right?
Having these types of information on display helps avoid questions like—is there a risk of exposing passwords while scanning? Is my access enough?

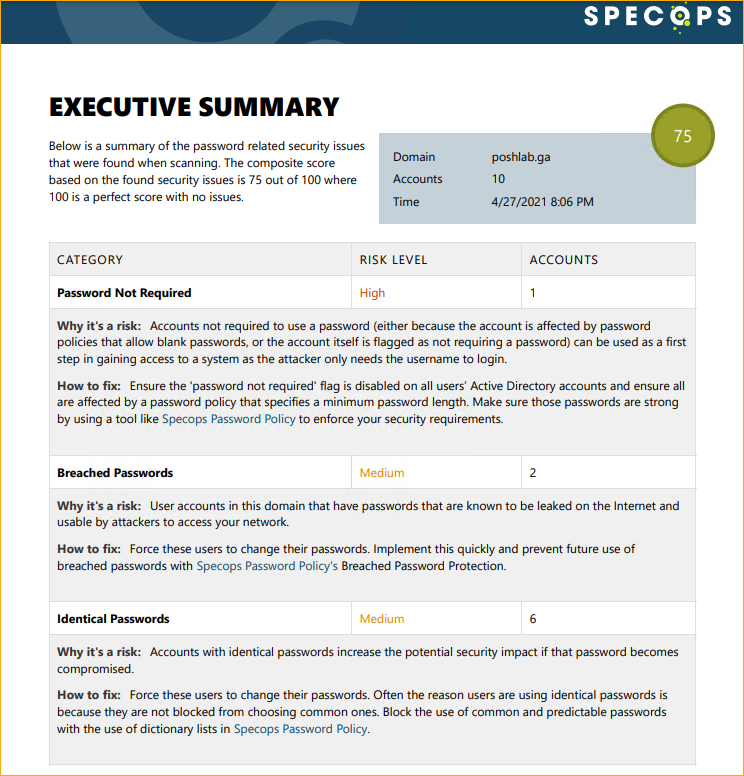
And when it’s time to present reports, Specops Password Auditor also produces professional-looking PDF reports. The PDF report provides an executive summary of its findings, the assessment for each, and possible fixes.
Specops Password Auditor has two main functions; scanning the AD to identify password vulnerabilities and generating reports of its findings. Stick around to know more about them.
Scanning for Password Vulnerabilities
Specops Password Auditor’s primary feature is scanning the AD to identify password-related security risks. Specops Password Auditor also reads password policies and compares them to multiple industry standards.
I ran Specops Password Auditor on my environment to test it out, and here’s the rundown.
Before the scan starts, the tool asks you whether you want to skip the Breached Password scan or download the latest breached password database to your computer.
Should you choose to download, know that the database size is approximately 5GB. Make sure your download location has enough space. You only need to download the database once, and the succeeding scans can re-use it.
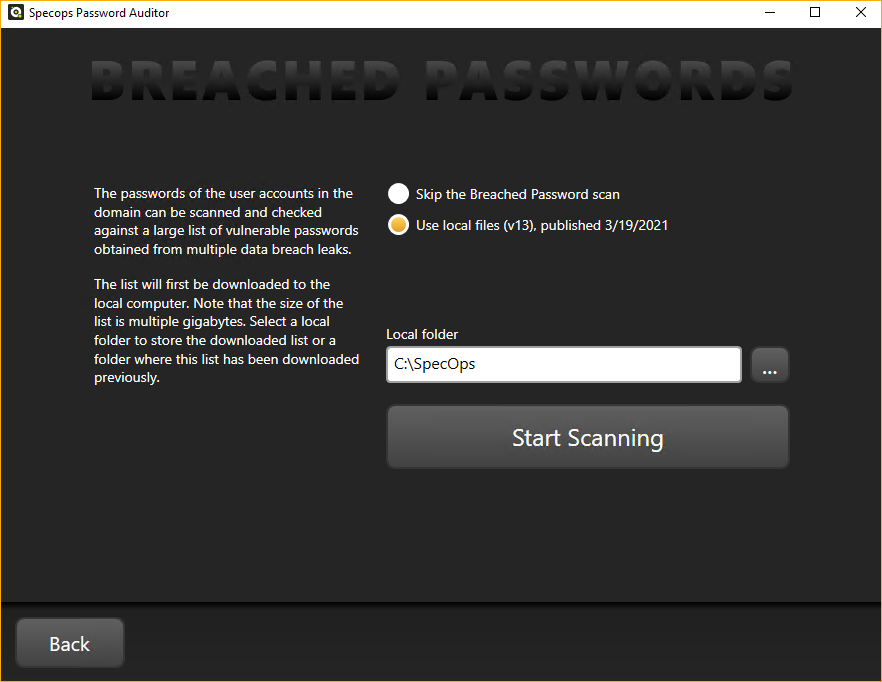
I noticed that there’s no option to check for an updated database. Perhaps the update functionality is already baked into the tool, but I couldn’t find any documentation about it. Having a database update check option would be nice.
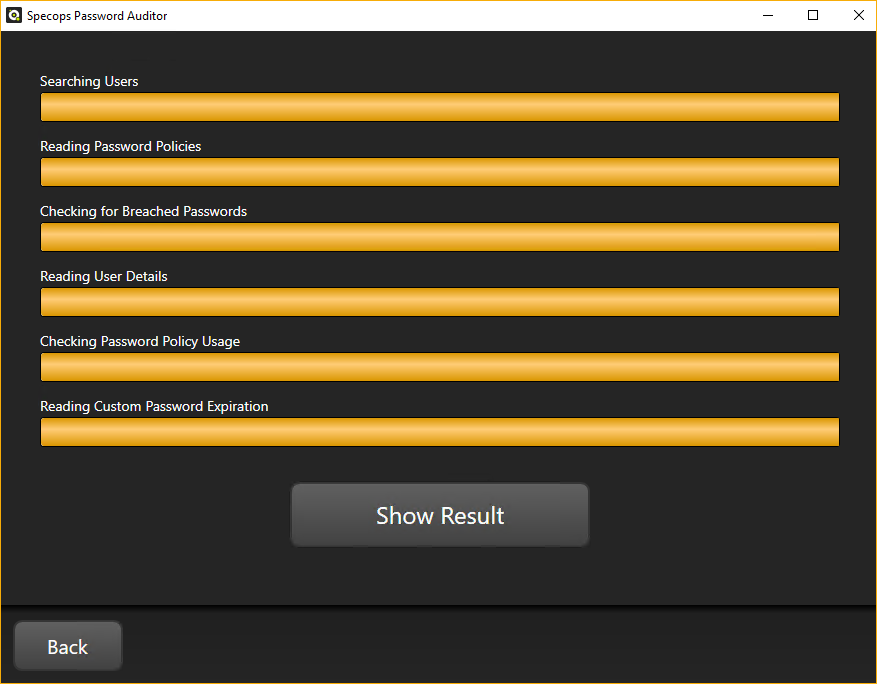
During the scan, all you see are the different progress bars that represent each action. You’ll notice no countdown timer or percentage display, but it’s no big deal. In my experience with other tools, timers and percentage counters are rarely accurate anyway.
After Specops Password Auditor finished scanning your AD, you can now see the reports represented by cards. As you can see below, there are two different header colors for the cards. What’s the difference?
If a domain administrator runs the scan, the gold and blue reports will be available, as you can see below. In contrast, non-administrators can only get the blue reports. I think this type of visual distinction is good as it makes the difference between result types easier to spot.
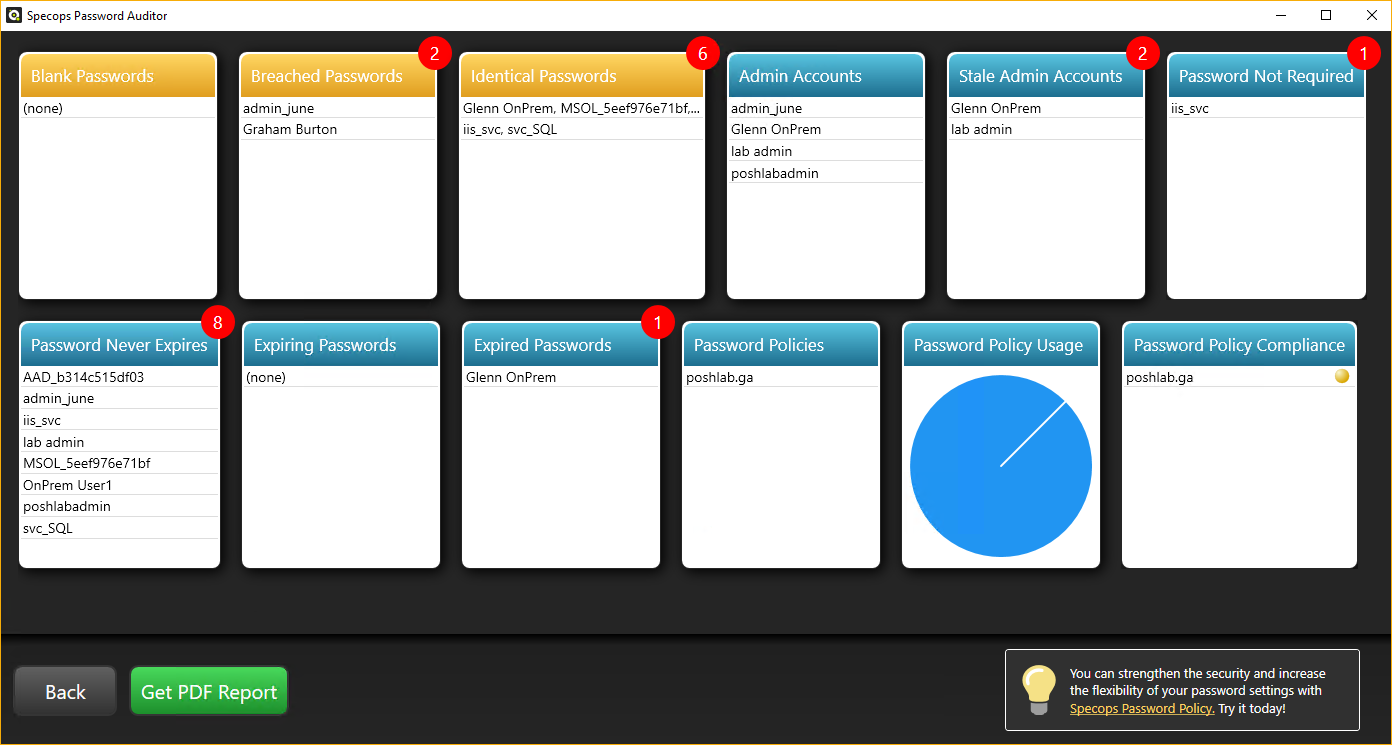
Let’s briefly cover each report card by order of appearance.
- Blank Passwords – shows all user accounts that have blank passwords.
- Breached Passwords – lists the users whose password hashes match the entries in the breached passwords database.
- Identical Passwords – list user accounts with identical passwords in the same line. Identical passwords typically happen on service accounts or generic accounts.
- Admin Accounts – lists all accounts with administrator privileges.
- Stale Admin Accounts – shows all administrator accounts that have not logged on to the domain within 90 days. But, this threshold is adjustable and can go from 30 to 360 days.
- Password Not Required – shows the list of users whose accounts that do not require passwords.
- Password Never Expires – shows the list of users whose passwords do not expire.
- Expiring Passwords – shows the list of users whose passwords will expire in 10 days. This threshold is adjustable from 1 to 365 days.
- Expired Passwords – shows the list of users whose passwords have already expired.
- Password Policies – lists all the password policies in your domain.
- Password Policy Usage – shows the distribution of users per password policy.
- Password Policy Compliance – shows the comparison of each password policy in your domain with several industry standards. Here you’ll see if your password policies are non-compliant, partially compliant, or compliant to industry standard recommendations.
While the cards give you an overview of the reports, you can drill down each result by clicking each card. For example, if you click the Breached Passwords card, you’ll see the details of that card in a list. You can also sort the results by column, which could help when viewing large results.
Additionally, Specops did a great job of putting the explanation right next to the results. This way, you wouldn’t have to guess what or why the tool considered these results as security risks.

Exporting Reports
What good are reports if you cannot share them? The on-screen reports are functional and interactive, but they are not for sharing. Specops Password Auditor allows you to export the reports in two formats, CSV and PDF, and I tried both of them to see if they’d be helpful reports.
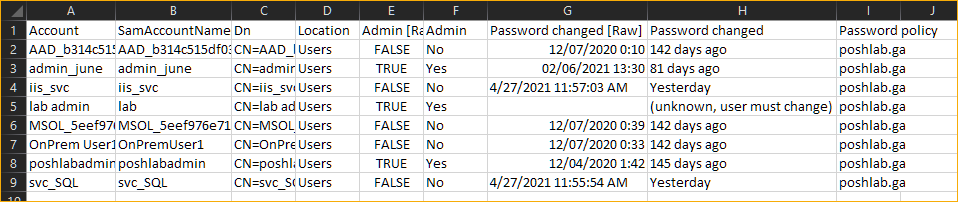
CSV Reports
As you can see below, you can export the results of a card by clicking on the Export button. In this example, I’m exporting the Password Never Expires report to a CSV file.
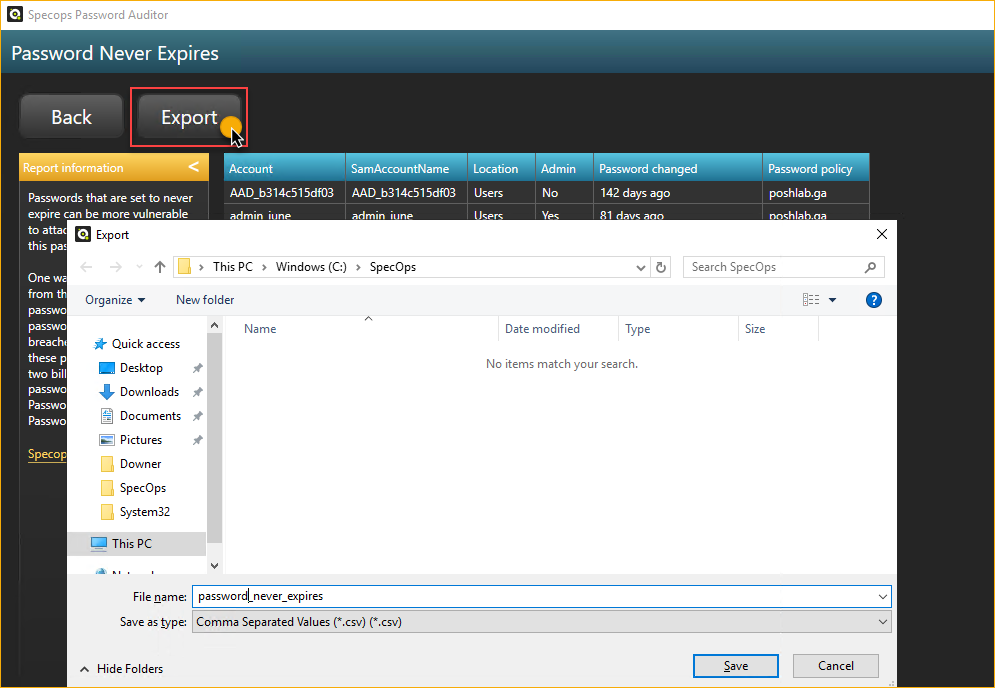
After the export, I now have a CSV file that I can use as input for remediation scripts or something similar. This report is indeed useful.
PDF Reports
Unlike the CSV report, which is raw by design, Specops Password Auditor generates beautiful and professional-looking PDF reports. To generate the PDF report, you have to click on the Get PDF Report button on the main window.
You’ll get the option to generate a summary or a full report. Both report types include a summary, but the full report contains the results, such as users and policies.
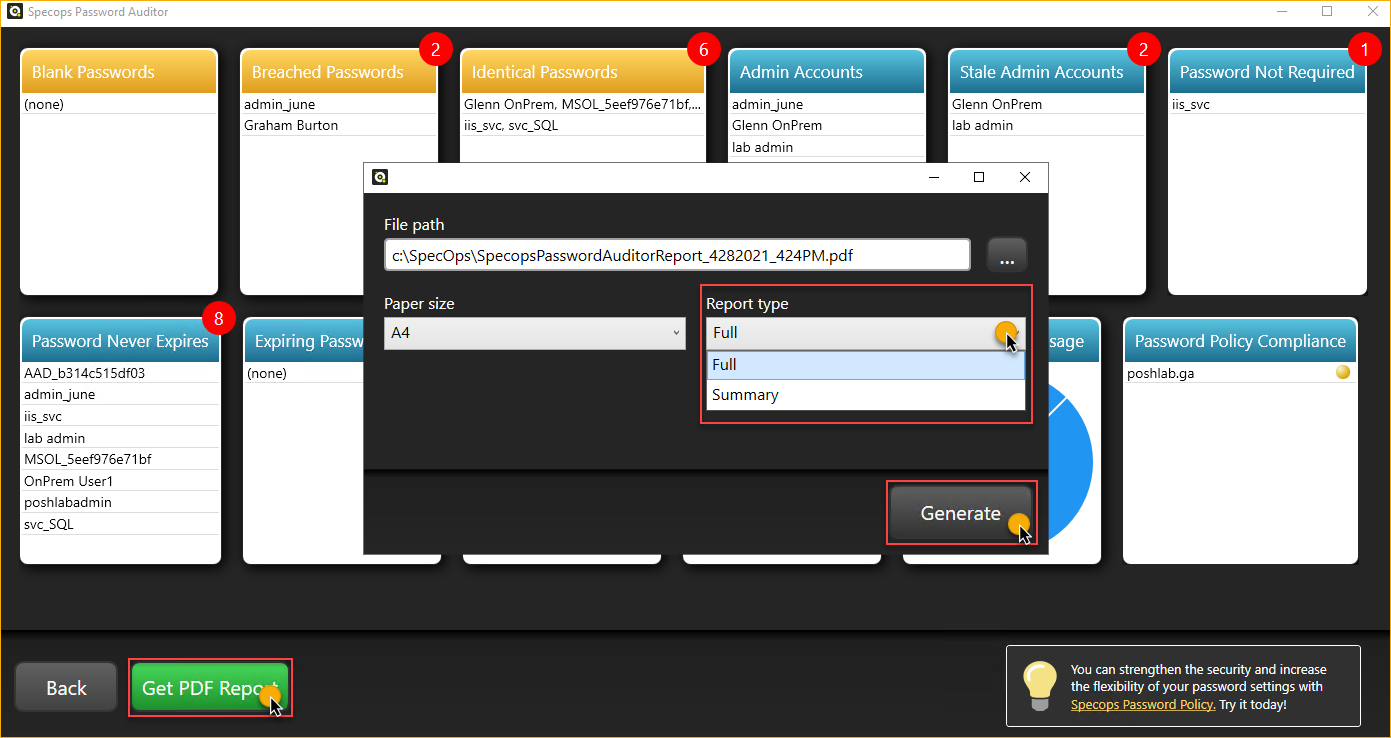
The image below is a snip from a full PDF report.
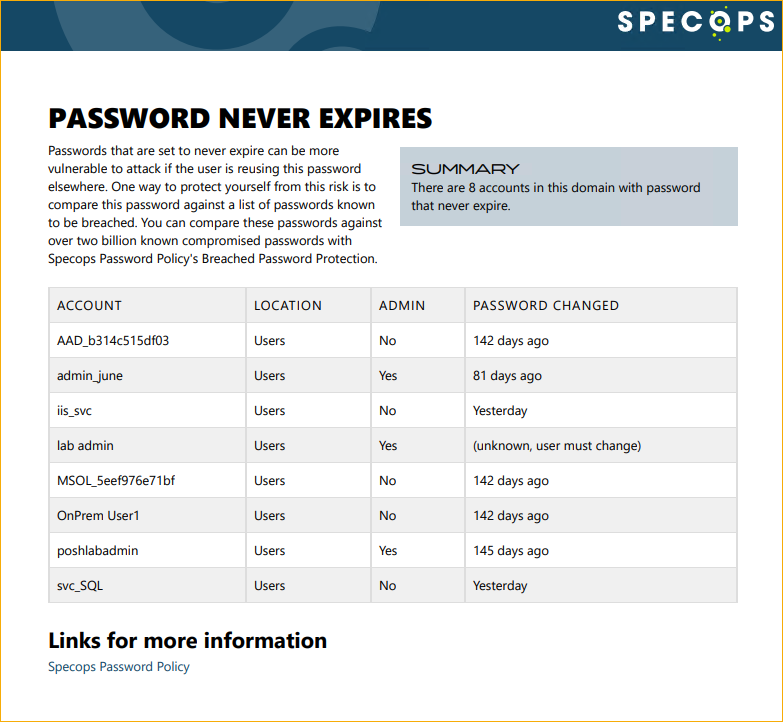
The CSV and PDF reporting is a significant feature of the Specops Password Auditor to help admins address password security findings. The PDF report includes a summary, but it also has information for possible fixes to the risks that the tool identified.
Will Specops Password Auditor Work in My Environment?
Primarily, Specops Password Auditor is a Windows product, and you most likely already have the requirements to run it. There are only a few and these are:
- A computer with Windows Server 2012, Windows 8, or later.
- The computer must be domain-joined.
- And has .NET Framework 4.7
If you are downloading the Breached Password Database, you need:
- 5GB of storage space for the database.
- Your firewall or proxy must allow access to:
- https://breach-protection.specopssoft.com/
- https://download.specopssoft.com/
Specops Password Auditor Support Options
I never needed support when I was testing out Specops Password Auditor. But checking on the Specops website, there no explicit mention if they provide support for Specops Password Auditor, either by phone, chat, or email.
If you navigate to the Specops Password Auditor support page, you can find a general guide and a troubleshooting guide. But the troubleshooting guide only has one entry, and it’s about how to enable the debug logging, and yet no mention of what you’re supposed to do with those logs afterward.
There’s also a knowledge base (KB), which, as of this writing, only has four entries. Perhaps the few available KB articles indicate that there aren’t many issues with Specops Password Auditor that they needed to write about?
Finally, Specops provides a contact form for when you need to get in touch with their support.
How Do I Get Specops Password Auditor
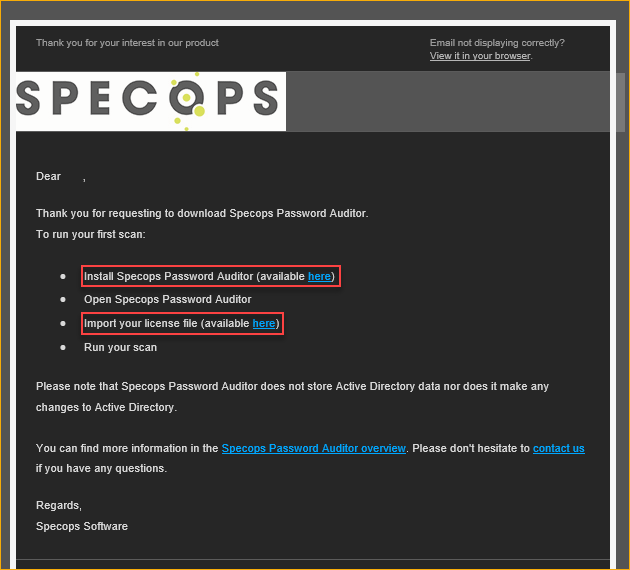
You can get Specops Password Auditor from the product’s download page. Going into the download process, you will need to provide your personal information such as your name, work email, phone, and company name.
Specops will email you the download links for the installer and the license file.
How Much Does Specops Password Auditor Cost?
As you’ve seen, Specops Password Auditor has great features that could help admins deal with possible password-related risks in their environments. But the question is, how much?
Specops Password Auditor costs nothing! It’s FREE!
The Verdict
Should you be using Specops Password Auditor? At this point, the better question is, why not? As you’ve seen in this post, Specops Password Auditor saves you time generating password audit reports.
With only a few clicks, this tool can scan your Active Directory and identify weaknesses and improvement opportunities to your password policies or your organization’s password management in general.
And above all, Specops Password Auditor is free. If that still doesn’t convince you, I don’t know what will.