You’ve decided that you need to start using GitLab for your project management, but not sure how to install GitLab securely? Not only is installing GitLab a complex process, but if not done correctly, your data could be at risk. But don’t fret, you’ve come to the right place!
Not a reader? Watch this related video tutorial!In this tutorial, you’ll learn the entire process of installing GitLab securely, so you get to set up SSL encryption and configure GitLab for optimal performance.
Sounds interesting? Jump right in!
Prerequisites
This tutorial will be a hands-on demonstration. If you’d like to follow along, be sure you have the following:
- A Linux server with root access – This demo uses Ubuntu 20.04 LTS, but any Linux distribution will work.
- A fully qualified domain name (FQDN) pointing to your server.
- Let’s Encrypt installed on the server.
- Minimum requirements – 8 GB of RAM, 50-100 Mb/s bandwidth, 2 GHz processor, and 20 GB of disk space.
Installing GitLab Community Edition
Now that you have an FQDN and your server prepped, it’s time to install GitLab. There are several ways to install GitLab, such as using the Omnibus package or compiling from the source. But this tutorial focuses on installing GitLab using the GitLab repository from its developer.
GitLab comes in two distributions:
- GitLab Community Edition (CE) – for users who prefer an open-source, community-supported version of GitLab.
- GitLab Enterprise Edition (EE) – for users who need the extra features that GitLab Enterprise Edition provides.
But this demo uses the Community Edition to test the application in your developer environment.
1. Open your terminal and run the apt update command below to ensure your system has access to all the latest software updates.
The apt update command updates the package index files used by the apt utility to retrieve information on available packages.
sudo apt update -y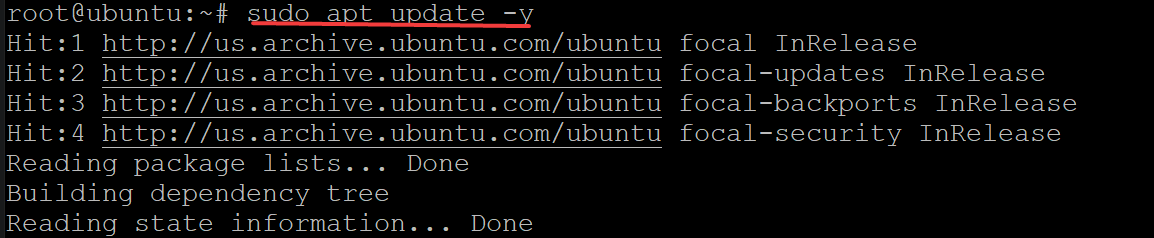
2. Next, run the apt install command below to download (curl) and install the following required dependencies for your GitLab installation:
openssh-serverpackage – Contains the OpenSSH server daemon and related tools, such as the host-key management tool and server, to provide remote login access to users.ca-certificatespackage – Contains a list of CA certificates. This package provides the necessary files to enable HTTPS support on your server.
sudo apt install curl openssh-server ca-certificates -y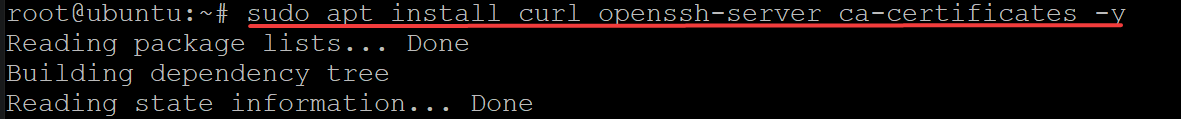
3. Run the curl command below to download (curl) the installation script from GitLab ( https://packages.gitlab.com/install/repositories/gitlab/gitlab-ce). The command then saves the installation script as a shell script (script.deb.sh) and runs it as a superuser (sudo bash).
sudo curl https://packages.gitlab.com/install/repositories/gitlab/gitlab-ce/script.deb.sh | sudo bashOnce the curl command completes, you will get the following output.
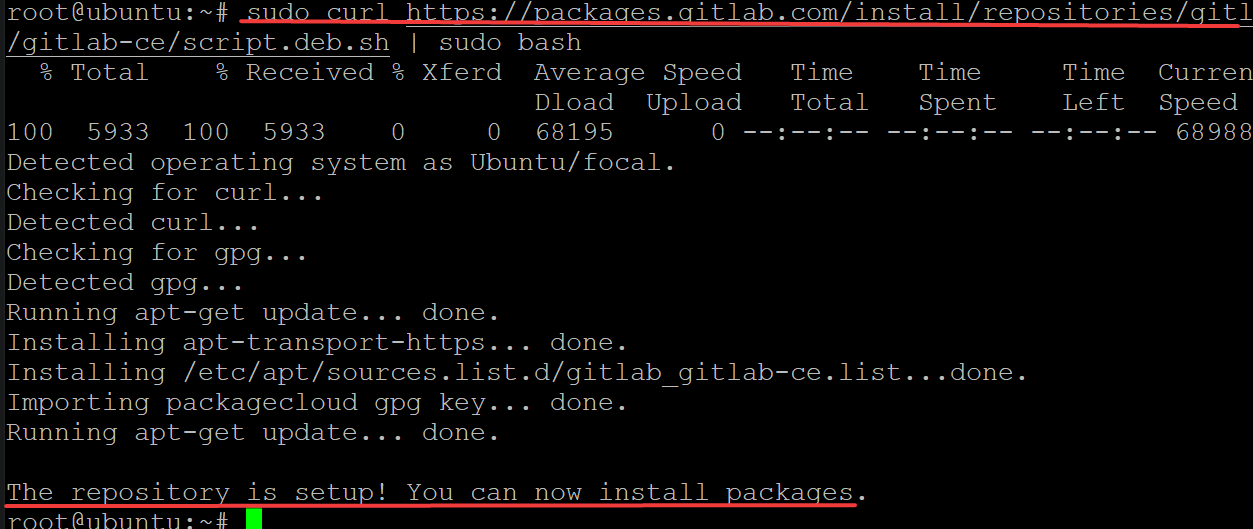
4. Run the apt-cache command below to verify that you’ve added the GitLab repository successfully.
apt-cache policy docker-ce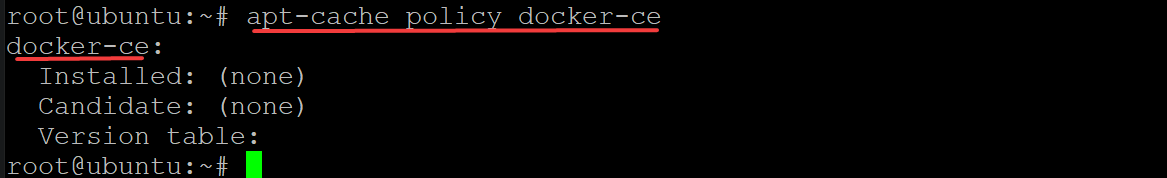
5. Now, rerun the apt update command to update the list of available packages. This command ensures that your system will use the newly added GitLab repository when you install GitLab.
sudo apt update -y6. Finally, run the apt install command below to install GitLab (gitlab-ce) on your system.
sudo apt install gitlab-ce -y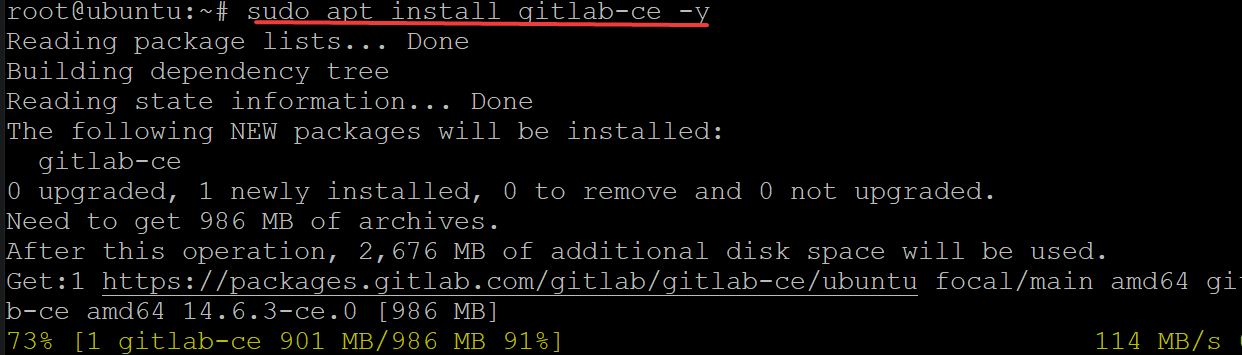
The installation will take a while, but you will see the following output when the installation is complete. This output confirms that you now have successfully installed GitLab on your system.
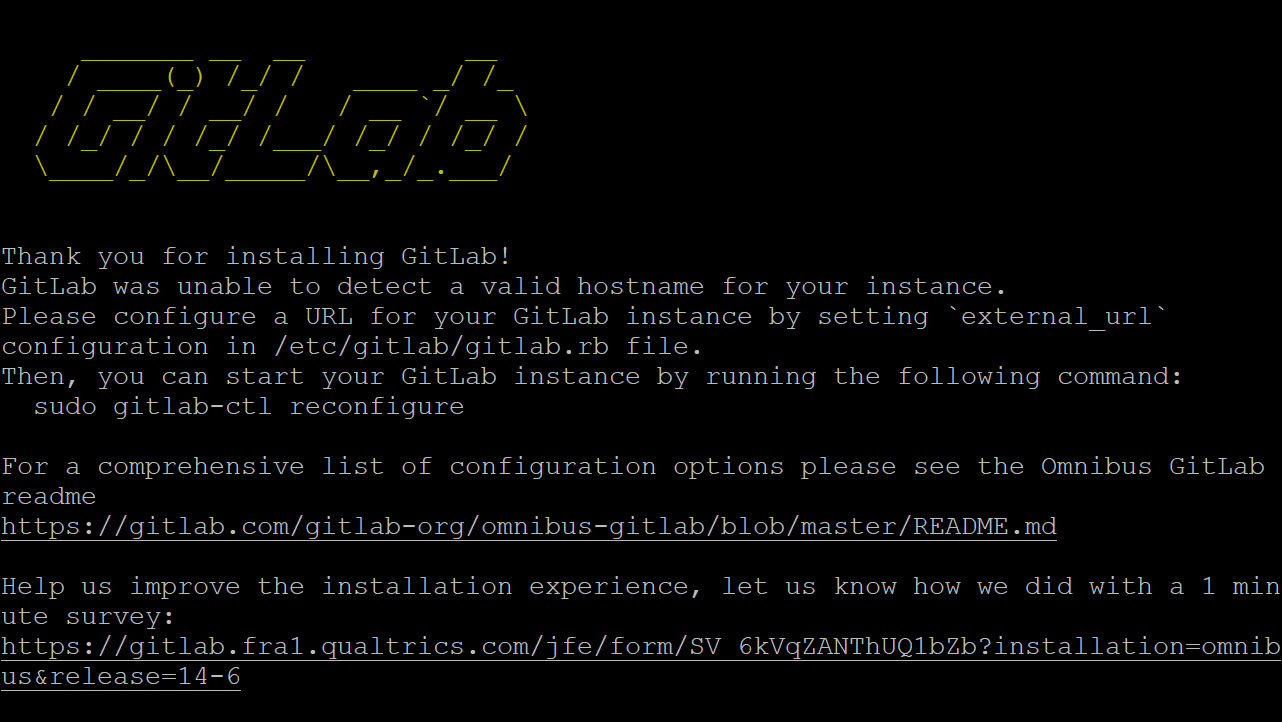
Configuring your GitLab Installation
You now have GitLab installed on your system, but you will need to make a few configuration changes before using GitLab. GitLab’s configuration file (/etc/gitlab/gitlab.rb) contains the global settings for GitLab that are not specific to the environment of your GitLab server.
You’ll modify GitLab’s configuration file to set your FQDN domain name and secure connection to your domain.
1. Open the /etc/gitlab/gitlab.rb configuration file in your favorite text editor.
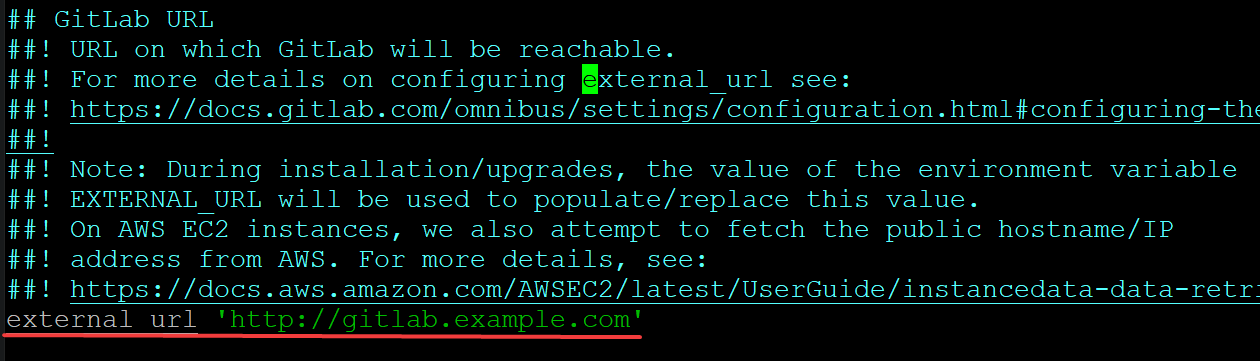
One of the most important entries in the GitLab configuration file is the external url directive, as shown below. This directive lets users access GitLab through a web browser.
Change the external url directive’s value from http://gitlab.example.com to https://gitlab.yourdomain.com, where yourdomain.com is your FQDN domain name.
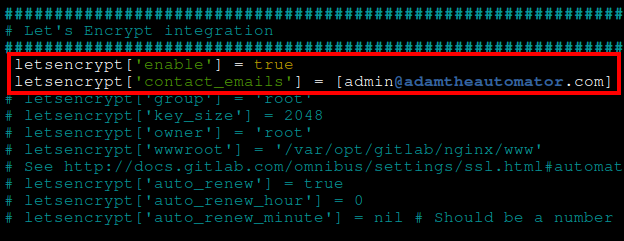
2. Next, navigate to the Let’s Encrypt integration section located at the bottom, and configure the directives with the following:
- Uncomment the
letsencrypt['enable']directive by removing the preceding#and change the value fromniltotrue. This directive tells GitLab to configure HTTPS on your server automatically. - Uncomment the
letsencrypt['contact_emails']directive by removing the preceding#, and put your email address as the value. Let’s Encrypt will use this email address to contact you when you need to renew your SSL certificate (every 90 days). - Save the changes and exit from the editor.
3. Lastly, run the below command to reconfigure and apply the changes in the /etc/gitlab/gitlab.rb configuration file to GitLab.
sudo gitlab-ctl reconfigure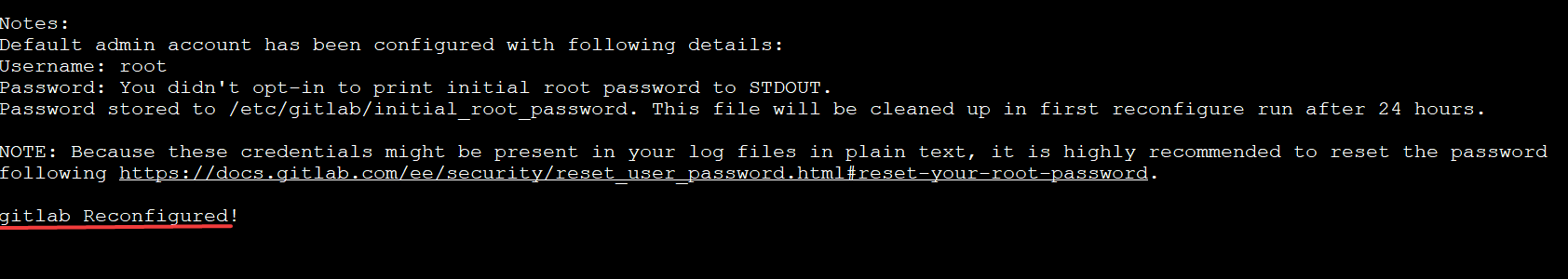
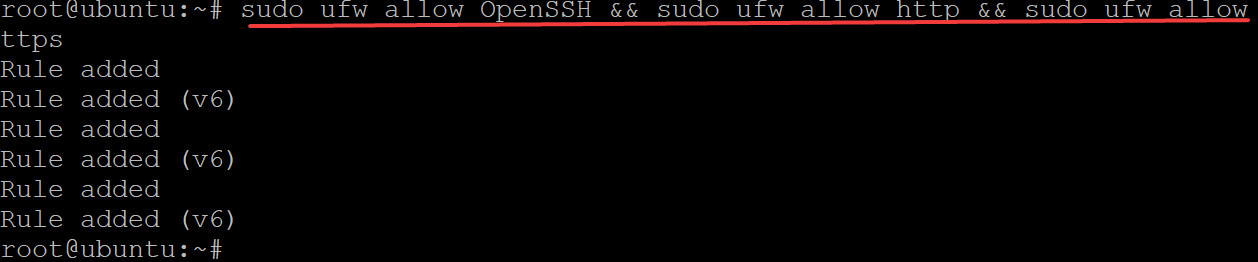
Configuring your Firewall for SSL Connections
Now that you’ve configured GitLab, you will need to configure your firewall rules to allow SSL and secure connections to your server. Uncomplicated Firewall (UFW) is the default program to manage firewall rules in Ubuntu.
If you put your server behind a firewall, you will need to open HTTP port 80 and HTTPS port 443 for SSL connections.
Run the following command to open OpenSSH, HTTP, and HTTPS ports for your GitLab server.
sudo ufw allow OpenSSH && sudo ufw allow http && sudo ufw allow http
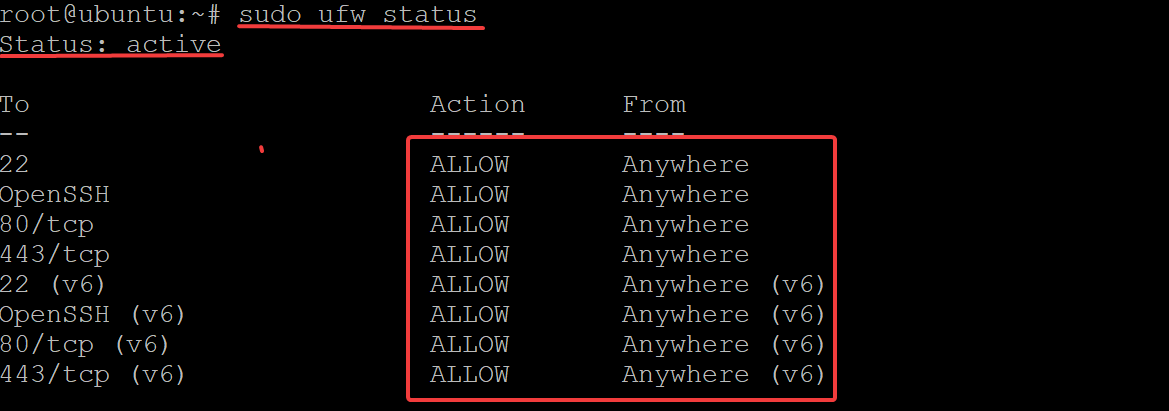
Now, run the following command to check the status of your firewall.
sudo ufw status
Securing GitLab via the Web Interface
Your firewall is up, but does it mean your GitLab is secure? Adding layers of security is never too much. So you’ll further secure your GitLab installation via the web interface.
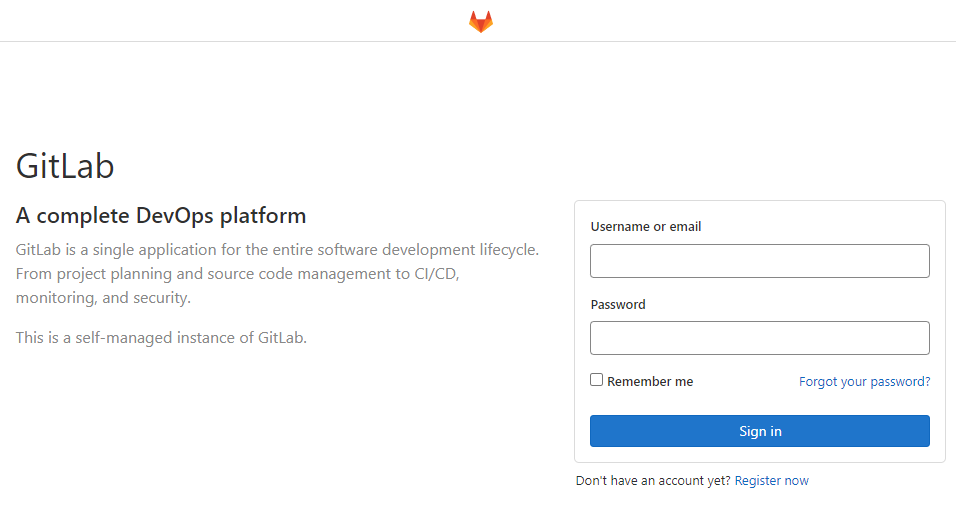
1. Open your favorite web browser and navigate to your GitLab server. For example, http://gitlab.example.com, where example.com is your FQDN domain name.
Choose either Chrome or Firefox when accessing your GitLab server for better security. These web browsers use their own HTTP/HTTPS protocols, which help enforce security policies.
Below, you can see the GitLab login page.
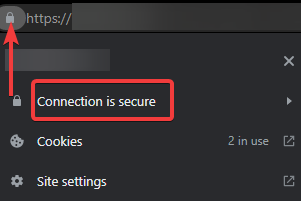
2. Next, click on the padlock icon (top-left) beside the address bar, and you’ll see your connection status. This demo shows the Connection is secure, which indicates your connection to the server is via HTTPS.
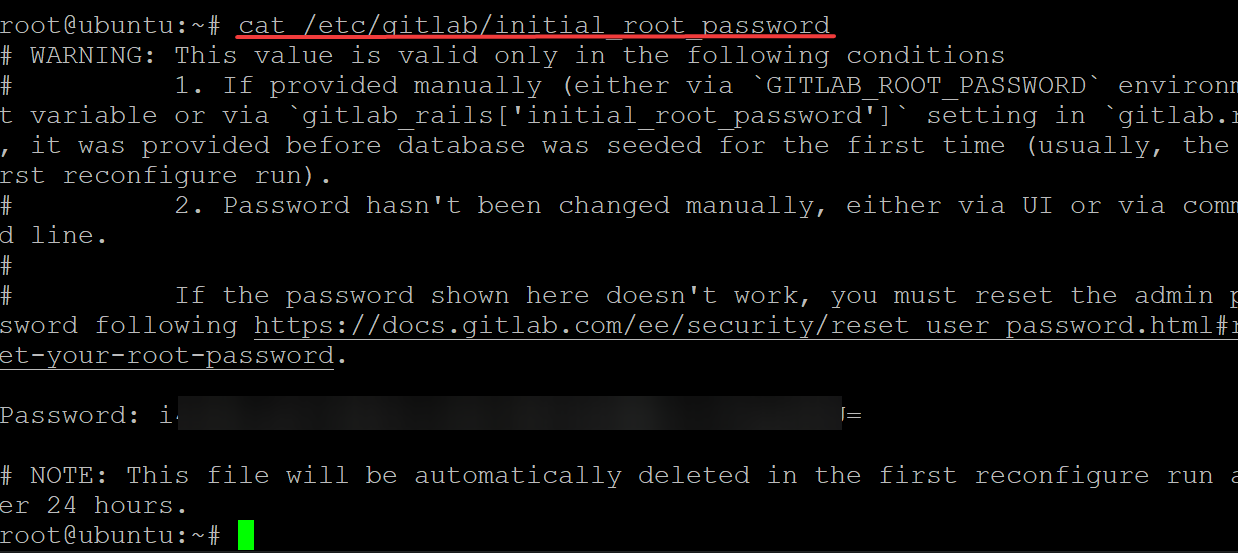
Return to your terminal, and run the cat command below to get your initial_root_password.
By default, GitLab installation comes with an automatically generated initial root password.
cat /etc/gitlab/initial_root_passwordCopy and save your initial root password in a secure place. You will use this password to log in to GitLab (step four).
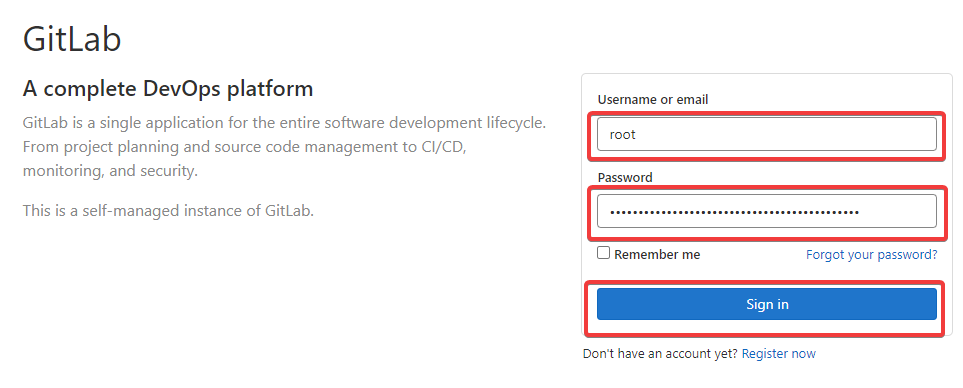
4. Return to your web browser, type in root as the username, and enter your initial root password as the password. Click on Sign In to log in to your GitLab server.
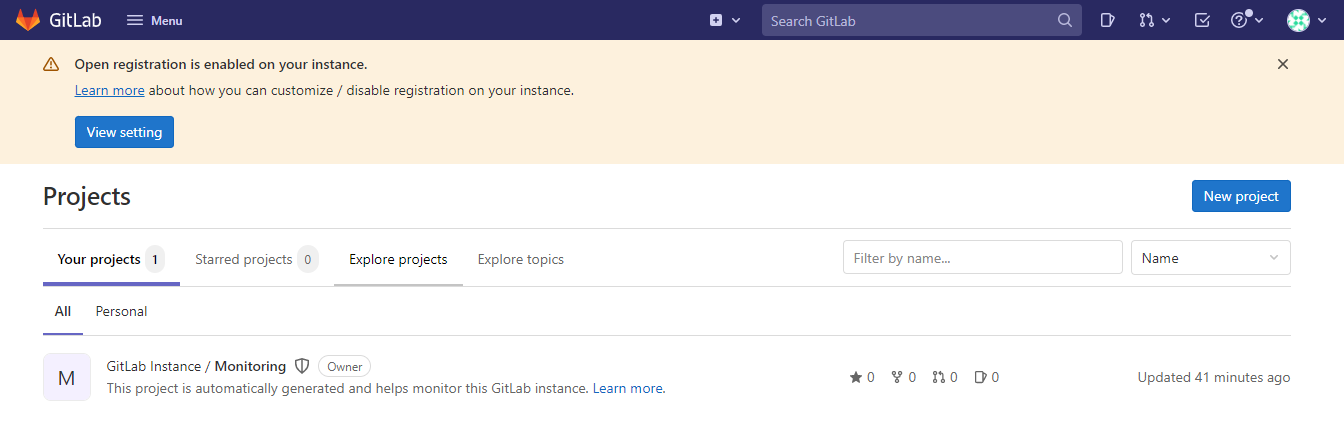
After logging in to your GitLab server, your browser redirects to the GitLab dashboard, as shown below.
Adding an SSH Key to your GitLab Account
Apart from the web interface, you can also access GitLab via a command-line environment in a secure fashion. How? You’ll first need to add an SSH key to your account, so you can access GitLab by running a command on your terminal without having to enter a password.
1. Run the ssh-keygen command to generate an SSH key pair suitable for use in SSH connections. When prompted, press the Enter key to keep the default save location for the SSH key (/root/.ssh/id_rsa) and don’t add a passphrase.
ssh-keygen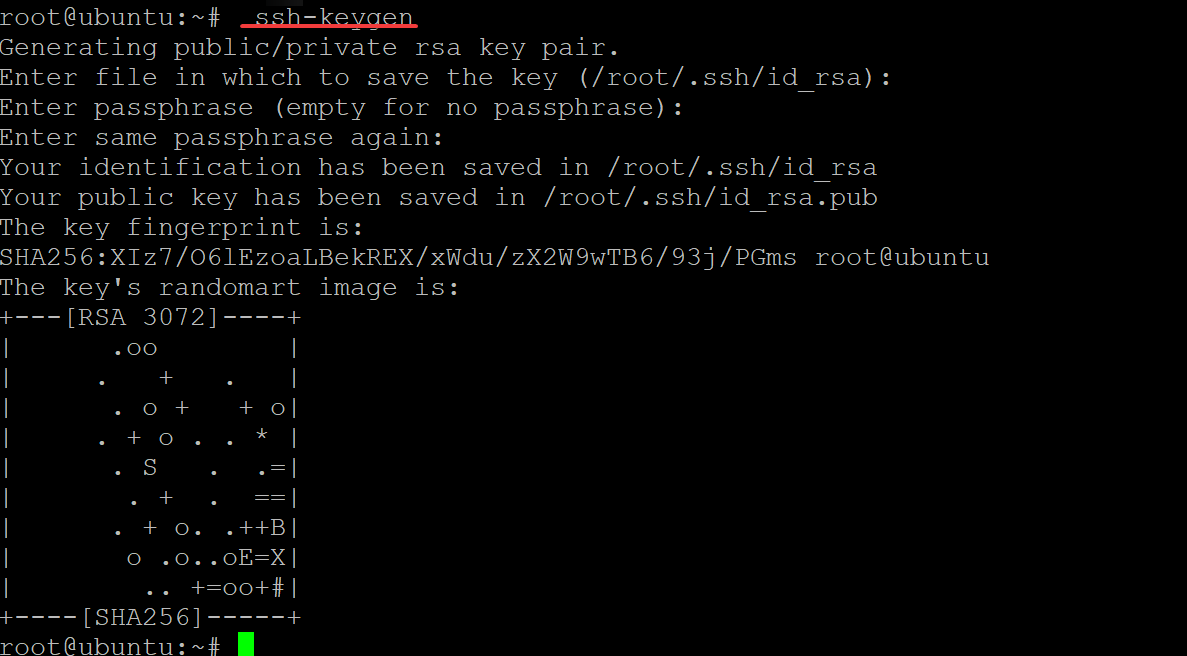
2. Run the cat command below to print your public key on-screen, as shown below. Copy the entire ssh-rsa public key string and save it somewhere safe. You’ll add this public key to your GitLab later (step three).
cat ~/.ssh/id_rsa.pub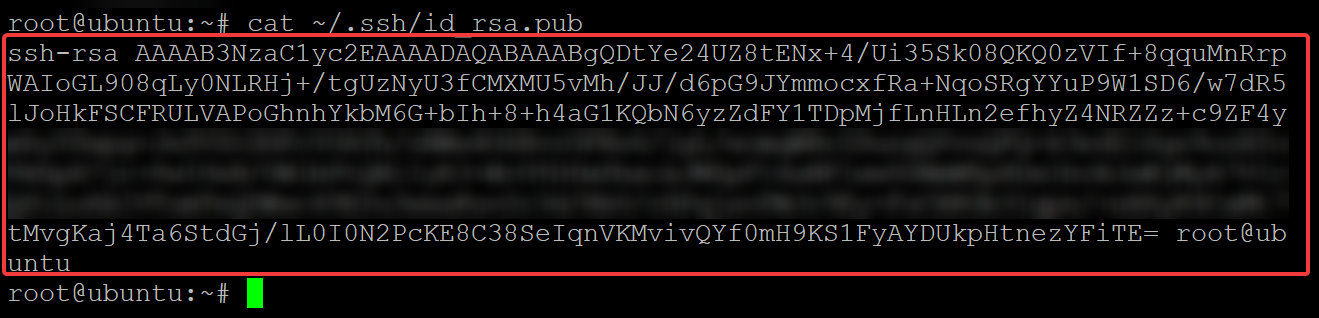
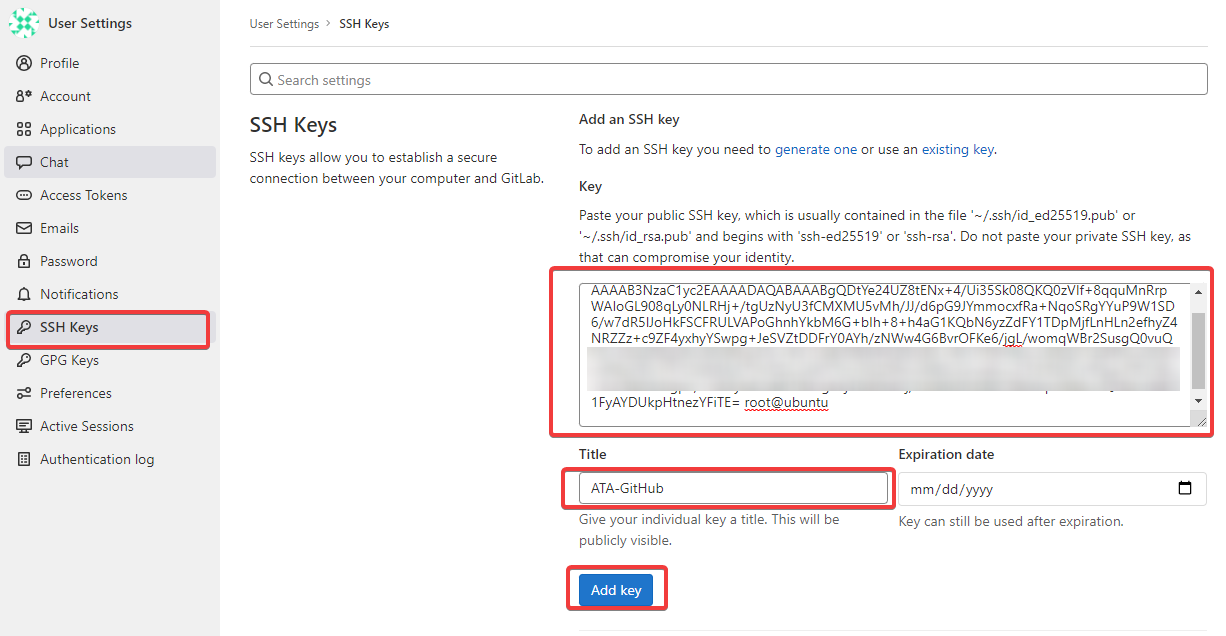
3. Return to the GitLab dashboard on your browser to add your public key with the following:
- Click on the SSH Keys menu at the left panel of the User Settings page to access the SSH Keys page.
- Paste the public key that you copied (step two) to the Key field, as shown below
- Provide your preferred name for the key in the Title field. But for this demo, the name is set as ATA–GitHub.
- Click Add Key to finalize adding the public key to your account.
Disabling Public Sign-ups
For additional security, you can disable public sign-ups on GitLab. Why? The public sign-ups feature in GitLab allows anyone to create an account on the GitLab server. Disabling this feature lets you avoid brute-force attacks on your server.
1. From the GitLab dashboard, click on Menu —> Admin to access the admin panel, then click on Settings to access the admin panel’s General settings page (step two).
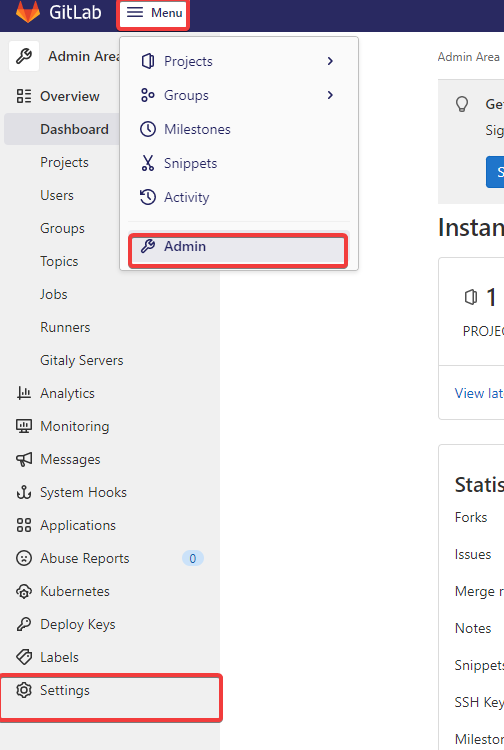
2. Disable the Sign-up enabled option under the Sign-up restrictions section. Doing so disables GitLab’s public sign-ups feature.
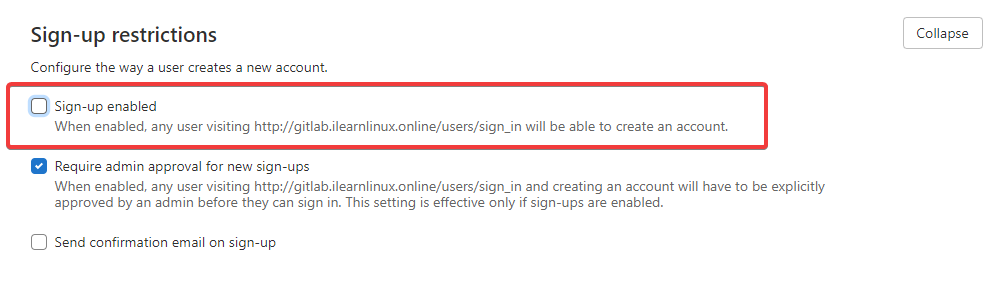
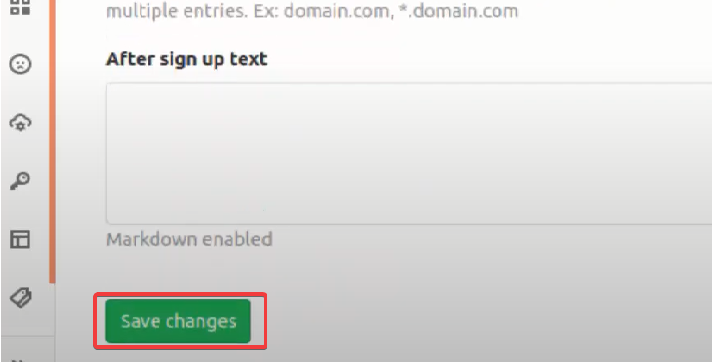
3. Scroll down and click Save changes (bottom) to save the changes you made to the sign-up restrictions settings.
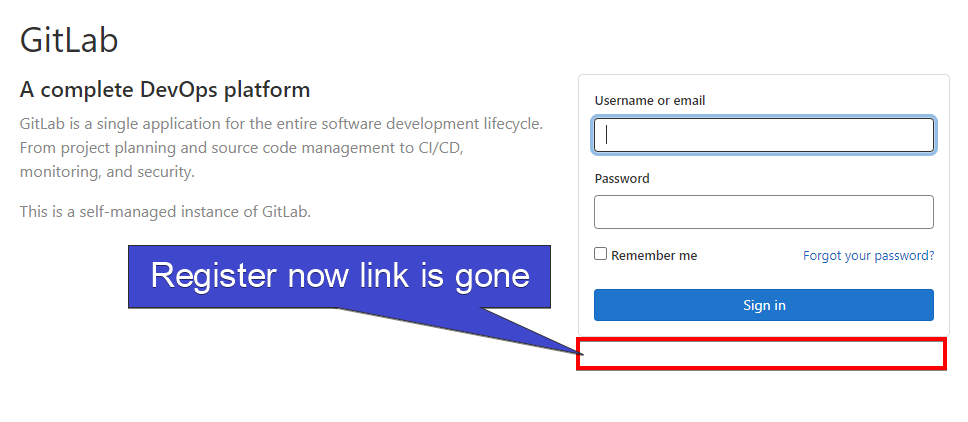
4. Finally, log out from your account and navigate your GitLab log-in screen.
As you see below, the Register now link is gone.
Testing your GitLab Server
At this point, you’ve already configured and secured your GitLab server, and that’s great! But how do you know your GitLab server is actually working? You’ll test your server by creating a GitLab project via the GitLab dashboard and cloning the project to your server.
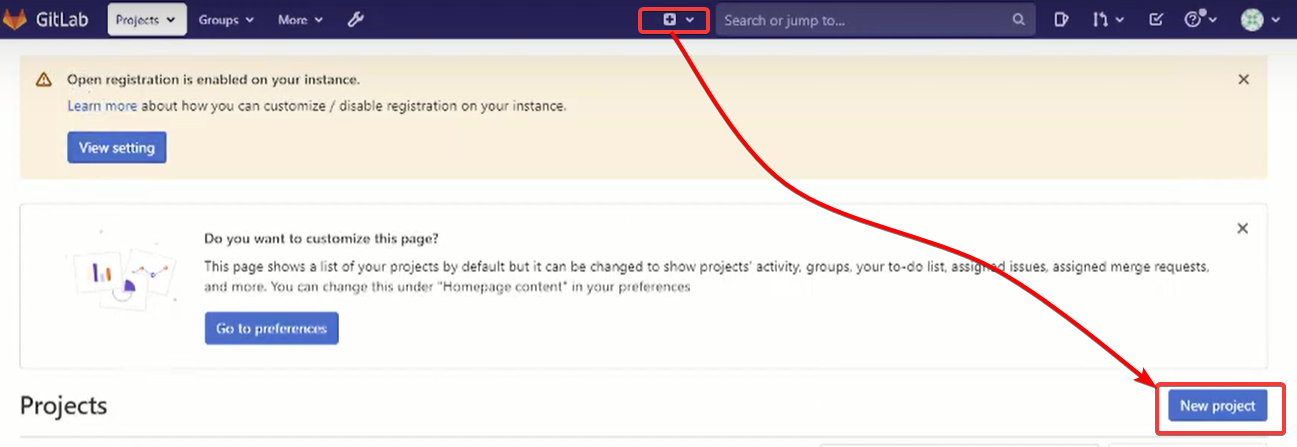
1. On the GitLab dashboard, click on the plus (+) icon beside the search box, then click on New project, as shown below, to create a new GitLab project.
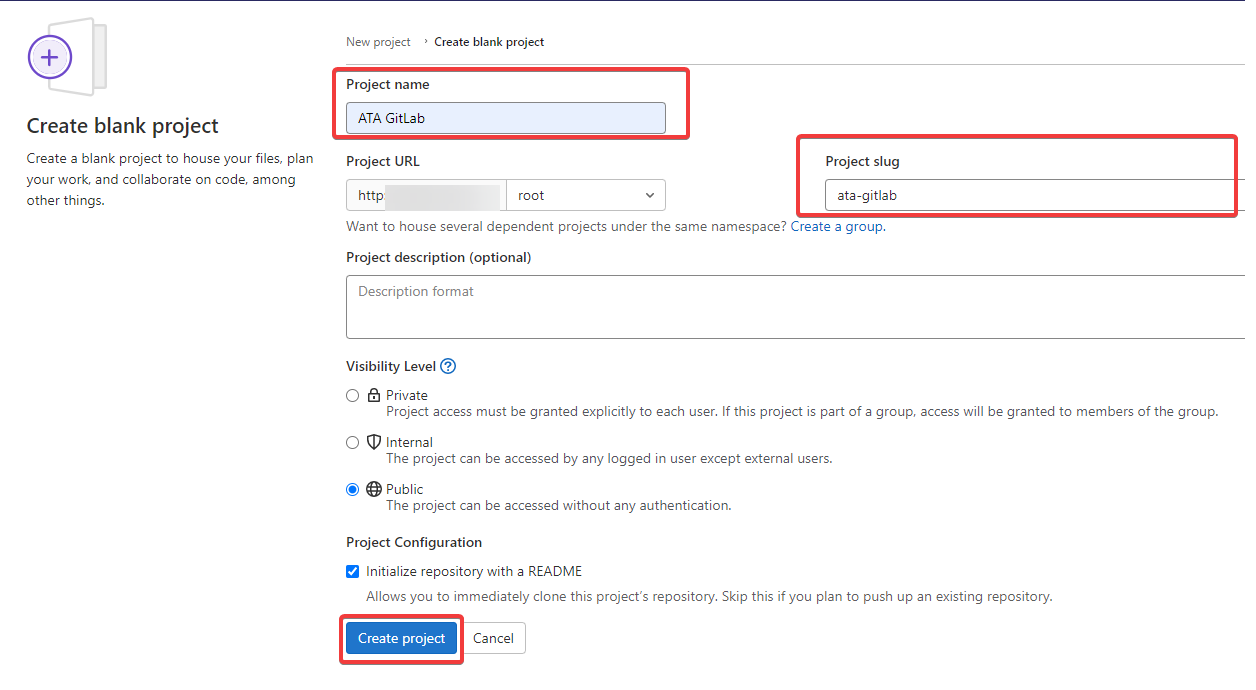
2. Next, provide your preferred Project name, but for this demo, the project name is set as ATA GitLab, and the Project slug is set to (ata–gitlab).
Click on Create project to create your new project.
3. Return to your terminal and run the following commands to set up your global username (--global user.name) and email (--global user.email) for Git. Each username and email are globally unique across all accounts on the GitLab server.
git config --global user.name "ATA"
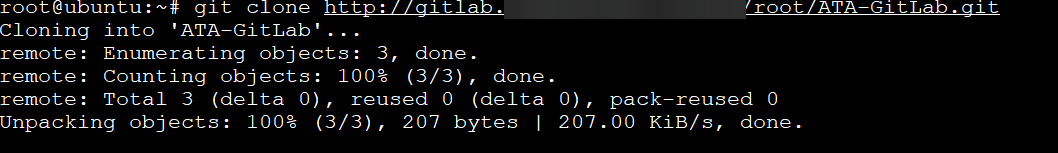
git config --global user.email "[email protected]"4. Now, run the git clone command below to clone the ATA GitLab project you created (step two) to your current directory. Replace yourdomain.com with your FQDN.
git clone http://gitlab.yourdomain.com/root/ATA-GitLab.gitIf all goes well, you’ll see an output similar to the one below. When the cloning completes, you’ll have a new directory called ATA-GitLab.
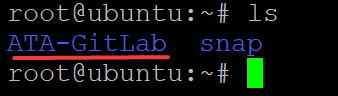
5. Finally, run the ls command to verify the ATA-GitLab directory exists.
lsSince you can clone the new ATA GitLab project and that the ATA GitLab directory exists, the output below confirms that your GitLab server is working properly.
Conclusion
In this tutorial, you learned how to perform a secure GitLab install on your Ubuntu Linux system. You’ve made sure to secure your GitLab server via the web interface, add SSH keys to your GitLab account, and test if your GitLab server works.
With this newfound knowledge, perhaps you’d like to learn how to set up automated Continuous Integration (CI) systems with GitLab?




