How to Add Timeouts to Pester Tests with PowerShell Runspaces
Prevent Pester tests from hanging indefinitely using PowerShell runspaces. Learn to handle variable scoping, module loading, TestDrive access, and stream capture challenges with timeout protection.
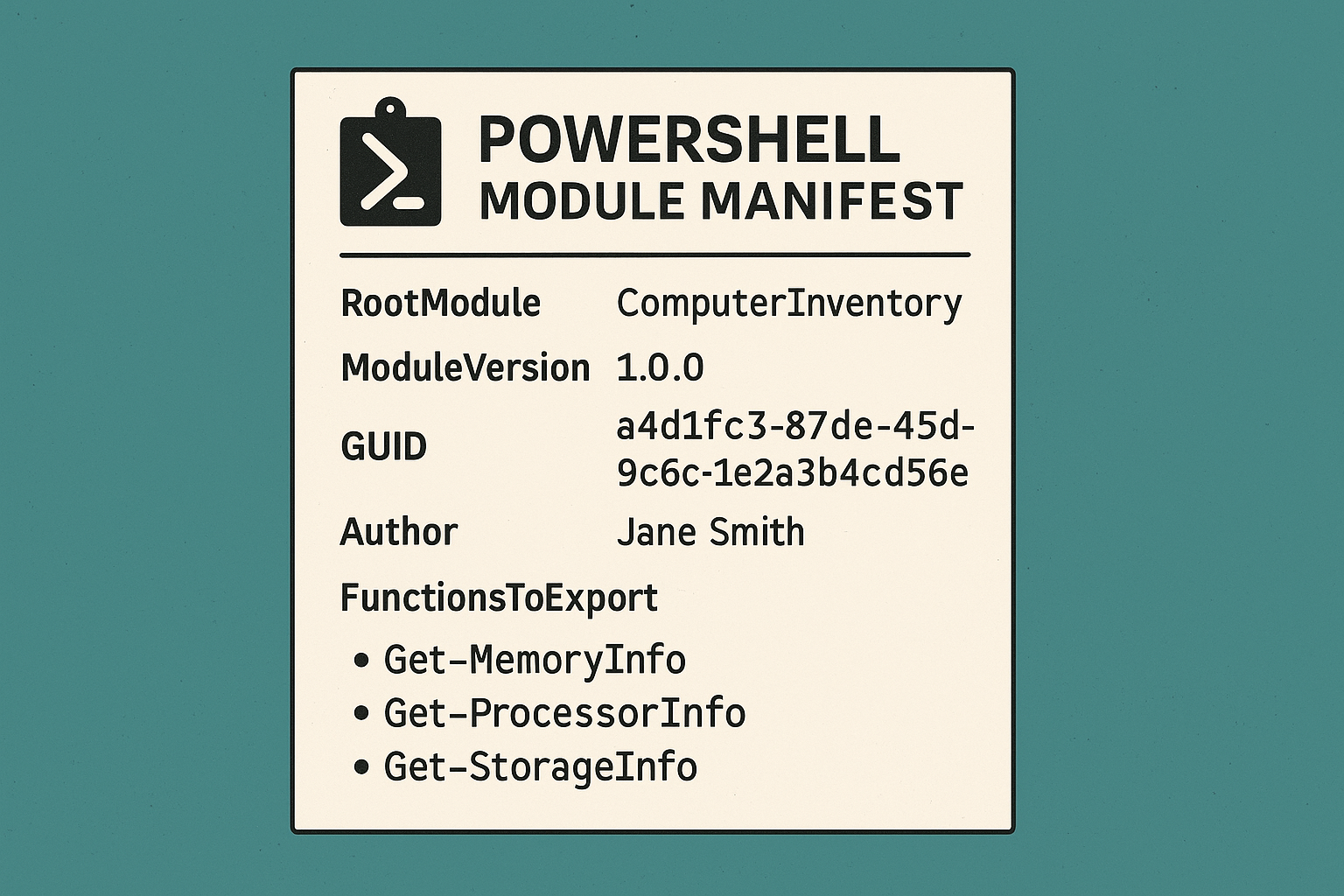
PowerShell 101: Creating a Module Manifest
Maybe you've put together some great functions but struggle to make them cohesive, intuitive, or shareable. Without a way to define your module's identity and functionality, managing or scaling as your scripts evolve into robust tools can be a headache. Not unless you have a module manifest in place.
Refactoring with AI: Why “Fix Everything” Is a Terrible Prompt
Transform your AI coding workflow: Learn why asking AI to 'fix everything' fails spectacularly and discover my battle-tested, step-by-step framework for effective AI refactoring that turns chaotic code into clean architecture—without breaking your app.
When a Script is Worth a Thousand AI Prompts
When traditional scripts outshine AI: a developer's journey back to automation basics.
Vibe Coding: How I Built a 120K Line App Without “Learning to Code”
Building real applications with AI isn't just for developers anymore. Here's how I went from PowerShell scripts to a full-stack React/Express app by embracing "vibe coding" with AI.
Creating a Real-World Module: Creating Functions
Learn how to create PowerShell functions that gather memory, storage, and processor information from remote systems, transforming raw output into readable formats.
Creating a Real-World PowerShell Module: Scaffolding Functions
Learn how to create a custom PowerShell module for computer inventory management. This hands-on guide covers module structure, functions, and remote capabilities.
Build a Scalable PowerShell Pester Testing Framework
Learn how to create a maintainable and organized Pester testing framework for PowerShell that scales with your needs. Perfect for large test suites.
PowerShell 101: Creating a Real-World Module: Scaffolding Functions
Learn how to create powerful PowerShell modules from scratch by building a computer inventory tool. Perfect for sysadmins who need custom automation solutions.
PowerShell 101: Finding and Installing New Modules
Learn how to find, install, verify and remove PowerShell modules efficiently. Master module management to enhance your PowerShell automation capabilities.
PowerShell 101: Importing Modules
Learn how to manage PowerShell modules like a pro! From importing and removing modules to troubleshooting common issues, master PowerShell modules in this complete guide.
PowerShell Modules: A Beginner’s Guide to Extending Functionality
Learn how PowerShell modules work, where to find them, and how to use them effectively. Master the building blocks that unlock PowerShell's automation potential.
PowerShell Pester 101: A Practical Guide for Beginners
Learn how to validate your PowerShell scripts with Pester testing. This hands-on guide shows you how to write tests that ensure your code works as intended.
How to Fix PowerShell’s Double-Hop Problem: A Complete Guide
Learn how to overcome PowerShell's double-hop authentication limitation with session configurations. This guide shows you practical solutions for remote access problems.
Master PowerShell Remote Sessions: Interactive & Persistent Access
Learn to manage Windows systems remotely using PowerShell interactive sessions from basic interactive connections to persistent sessions.
Creating Custom GitHub Actions: A Complete Guide for DevOps Teams
Learn how to build custom JavaScript GitHub Actions to share standardized, reusable code across your organization's workflows. This hands-on tutorial walks through creating authentication and secret management actions.
PowerShell Reusable Sessions: A Guide to Persistent Remote Connections
Learn how to leverage PowerShell reusable sessions to maintain persistent connections with remote systems. This tutorial shows you how to create, manage and effectively use PowerShell sessions for remote administration.