Active Directory (AD) sits at the center of most on-premises Windows environments. When AD is set up well, administrators can more easily manage authentication, authorization, and policy enforcement across their organization. When it isn’t, small issues build into long-term security and operational risks.
If you’re building or rebuilding an AD environment, the goal is to make sure it works securely and predictably from day one. Understanding the AD best practices is crucial to ensure your setup goes smoothly and stays that way. Here are 7 best practices organizations should implement to ensure their AD environment is efficient, secure, and resilient.
Plan Your Structure
While AD is designed to be flexible, some elements aren’t easy to change once in place. For instance, reworking Group Policy design after deployment can be time-consuming and disruptive, especially in live environments. As such, you should define the following before going live:
Domain and forest structure: Clear forest and domain structures are the foundations of an efficient, secure AD environment. In most cases, a forest containing a single domain is easier to manage, but larger or more complex organizations may need multiple domains for separation or compliance reasons.
Naming conventions: Consistent naming for domains, Organizational Units (OUs), groups, and accounts makes your environment much easier to navigate and maintain, as well as helping with auditing when necessary.
OU hierarchy: Your OU structure determines how you group users, devices, and resources, and how Group Policy Objects (GPOs) are applied. A well-designed hierarchy should reflect how you manage the environment (e.g., by department or function), not just how the business is structured on paper.
Administrative boundaries: This defines who has control over what within your environment. By delegating permissions at the OU or role level, you can distribute administrative tasks without giving away unnecessary privileges, which improves both security and scalability.
Build with Least-Privilege in Mind
Excessive access is a common issue in AD environments and opens the door for damaging credential-based attacks. Keeping privileges tightly controlled limits the impact if credentials are compromised, so it’s worth putting a few guardrails in place from the start:
- Separate standard user accounts and admin accounts
- Avoid using domain admin credentials for routine tasks
- Delegate permissions where possible instead of centralizing everything
- Create OUs that reflect security requirements, not just organizational structure
Remember that Enterprise Admins, Domain Admins and Administrators by default have the highest AD privileges. Ensure that those accounts are protected by security measures like multi-factor authentication.
AD includes built-in security features, but they often only provide a basic level of protection. For instance, the native tool can’t block commonly used passwords, dictionary terms, or credentials exposed in data breaches.
Specialized tools like Specops Password Policy fill those gaps in two key ways. First, it extends native Active Directory capabilities with ready-made templates and auditor-ready reporting to support compliance, while guiding users to create stronger passwords at reset.
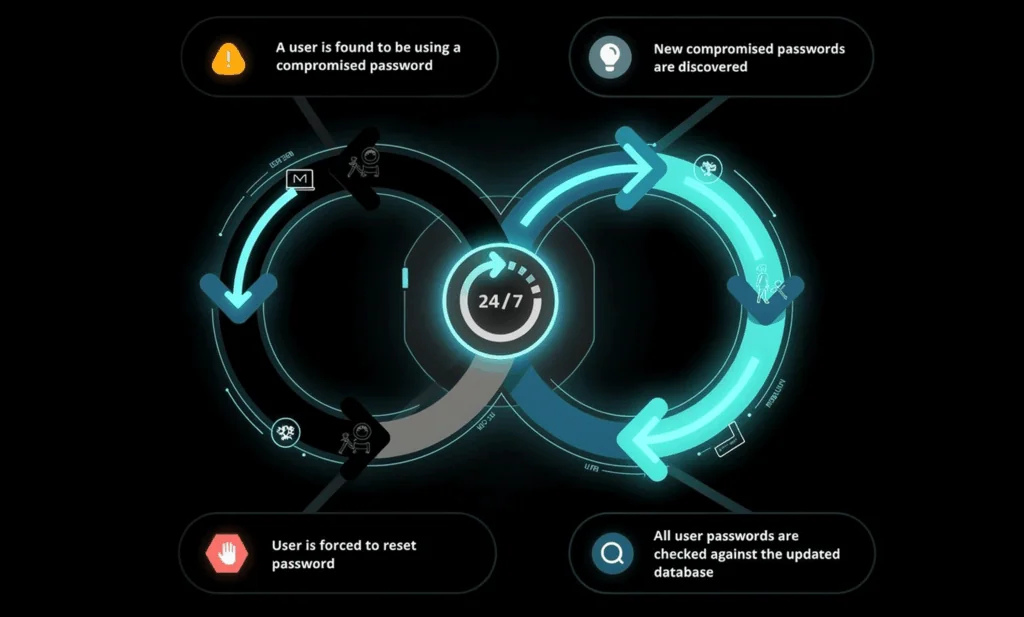
Second, it includes Breached Password Protection, which continuously scans AD against a database of over 5.8 billion unique compromised passwords, with alerts when exposed credentials are detected.
Design Group Policy Carefully
Group Policy is one of the most effective ways to secure and standardize your AD environment. Using the Group Policy Management Console, you apply GPOs at the OU level, so how you structure those units has a direct impact on how easily and consistently policies can be enforced.
As security settings like account permissions are enforced through GPOs, you must ensure that policies are carefully designed. Start with a baseline security GPO that applies consistent settings across all systems.
From there, layer in additional GPOs for more specific use cases, rather than trying to handle everything in a single policy. For instance, you can use GPOs to disable unnecessary services, configure Windows Firewall rules, enable audit logging, and enforce secure authentication protocols.
Use Groups to Manage Permissions
Managing permissions at the user level doesn’t scale well and quickly becomes difficult to maintain. A more reliable approach is to assign permissions to security groups, then add users based on their role or responsibilities. AD user attributes help with grouping and categorization.
This keeps administration straightforward and makes auditing far easier. When someone changes roles or leaves, you can update their group membership instead of chasing individual permissions across multiple systems.
Secure Your Domain Controllers
Domain controllers handle authentication and store sensitive data like password hashes, so they’re an obvious target for attackers. Limit who can log on to domain controllers and monitor them for unusual or suspicious authentication activity.
Domain controllers shouldn’t sit directly on the wider production network. Isolating them using network segmentation reduces risk, with tightly controlled firewall rules governing how other systems communicate with them.
Plan for Resilience
Planning for resilience early means you avoid single points of failure and keep authentication and access running even if something goes wrong. In practice, this comes down to a few key design decisions:
- Deploy at least two domain controllers per domain
- Place DCs appropriately across sites (if you have multiple locations)
- Configure proper Domain Name System (DNS) integration
- Test replication between controllers
AD is highly dependent on DNS, so misconfigurations here can cause authentication failures, login delays, or policy issues.
Implement Secure by Design Architecture
The fundamental challenge with AD is that many of its features prioritize backwards compatibility and ease of administration over security. A secure by design approach to AD ensures that security is treated as a core requirement rather than an add-on, and includes:
- Disabling or limiting NTLM authentication where possible
- Using modern authentication methods and enforcing strong encryption
- Separating administrative tiers to prevent privilege escalation
- Reducing the attack surface by limiting unnecessary services and access paths
Baking security considerations into your AD setup from day one will mitigate risks even as your environment grows and evolves. Done properly, this reduces reliance on reactive controls and limits how far an attacker can move, even if they gain an initial foothold.
If you’re interested in seeing how Specops can strengthen these controls in your AD environment, book a demo to see Specops solutions in action.




