Robocopy is a top tool of system administrators around the world. Easily able to handle complex file transfer tasks, RoboCopy is a tried and true swiss army tool for any number of file transfer scenarios. Synchronizing files is a challenging problem for a myriad of reasons. The Robocopy /MIR switch aims to make the process of keeping two directories synchronized that much easier. Although this switch is not a two-way synchronization, there are many handy uses!
If you want to learn more about robocopy, be sure to check out the Ultimate Guide to Robocopy!
What is so special about Robocopy /mir?
Let’s suppose that you have a temporary backup folder and you need to verify that all of the files in the source directory make it to a backup directory. Since backup files can get quite large, perhaps we want to make sure that the destination folder does not grow too quickly with stale backup files. Often manual backups or temporary copies are put into backup folders, and it is all too easy to run out of disk space.
To make sure we don’t run out of storage space, the ideal transfer operation is a copy and purge. This operation makes sure that all of the files in the source directory make it to the destination directory and remove all destination files that are not present in the source directory. This type of scenario is exactly what the Robocopy /mir switch is made for!
Functionally, Robocopy /mir is equivalent to the /e /purge options in Robocopy with a small difference in behavior. With the /e /purge options, a destination directories security settings are not overwritten. When using the /mir option, the security settings for the destination directory are overwritten.
/miralong with a handful of other commands are destructive to data if used incorrectly. This can potentially delete files in the destination directory so use with caution!
File and Folder Security with the Mirror Command
As mentioned above, there is a unique behavior related to security permissions and destination directories. When using the mirror switch, you might find that the file permissions themselves are not changed, only destination folder permissions. This is by design as for performance, and for practical reasons, individual file permissions were not intended to be copied using the mirror command.
What does this look like in practice? Let’s take the example source directory folder structure like so:
- Folder1
- File1 – Unique permissions
- File2
- Folder2 – Unique permissions
- File1
- File2 – Unique permissions
The result of a mirror command will result in the following file and folder permission structure. As you can see, the only permissions that are carried over are the unique folder permissions. The unique file permissions will not be carried over.
- Folder1
- File1
- File2
- Folder2 – Unique permissions
- File1
- File1
- File2
Of course, there are plenty of scenarios where you would like the permissions to be copied and kept in sync; those scenarios will be explored in further detail later on in the article.
Using Robocopy /mir in Practice
There are many different ways to utilize the Robocopy /mir command, and certain behaviors have changed over time. These changes are primarily around copying file security permissions which are made easier in the Vista version of Robocopy.
Mirror a Simple Directory to a Destination
One of the simplest ways to take advantage of the mirror command is to simply mirror two directories on a single server. We will use two parameters, the Robocopy /mir command and the /v command for verbose logging and output. The verbose command is useful to see what Robocopy is doing and make sure the files that we want to copy are doing so.
robocopy D:\Articles\SourceDirectory\ D:\Articles\DestinationDirectory /mir /v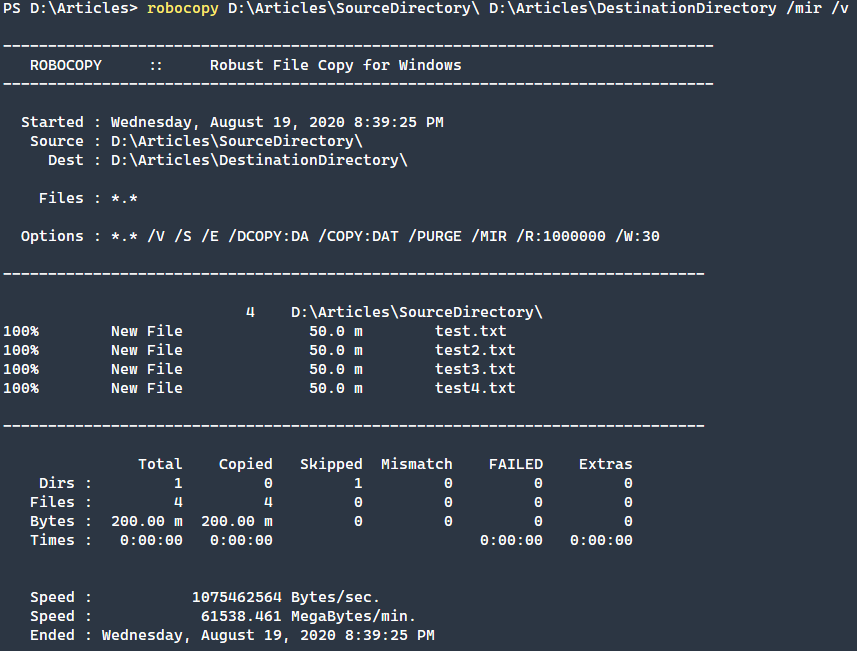
Depending on your needs, this might work just fine. File attributes are copied with the files, but the file security settings are not copied. The next example you may want to see is how to properly copy over the files with the security intact?
Mirroring a Directory with Permissions
To do a similar mirror operation but properly copy the file and folder permissions, we need to use the /sec and /secfix commands. The /sec command will copy the file security over for changed files, while the /secfix command will update the security for unchanged files. By combining these commands with /mir you will effectively mirror all of the files, folders, and permissions from a source directory to a destination.
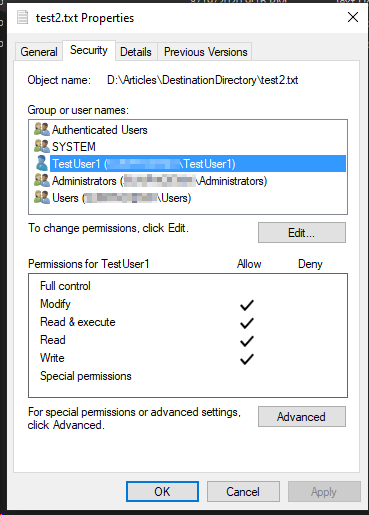
In this example, we have a directory with four files just like the first example. In addition, we have modified the permissions on test2.txt to add an additional user with modify permissions.
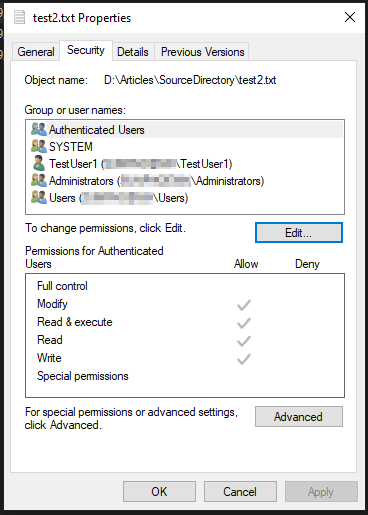
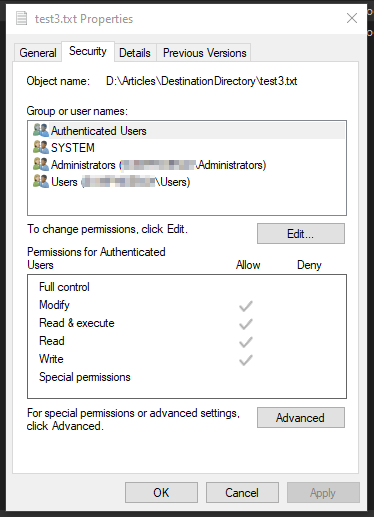
Here we are also going to modify test3.txt in the destination folder with differing permissions to demonstrate how permissions will properly copy over utilizing the /sec and /secfix switches.
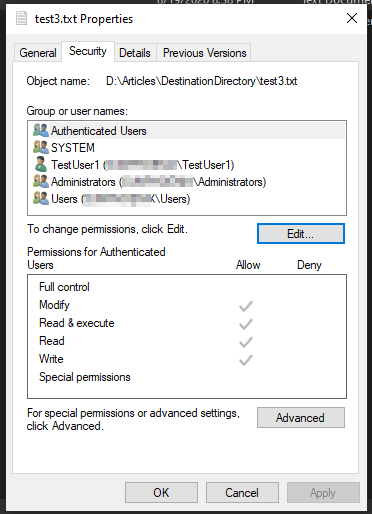
After running the following command, we will see that the permissions related to the user are copied over. Since the files were the same but with different permissions, the correct permissions have been copied while the file data itself remains synced.
Make sure to use Run as Administrator if you get access denied on copying over files. The setting of the permissions may require administrator rights to perform depending on your system security configuration.
robocopy D:\Articles\SourceDirectory\ D:\Articles\DestinationDirectory /mir /sec /secfix /v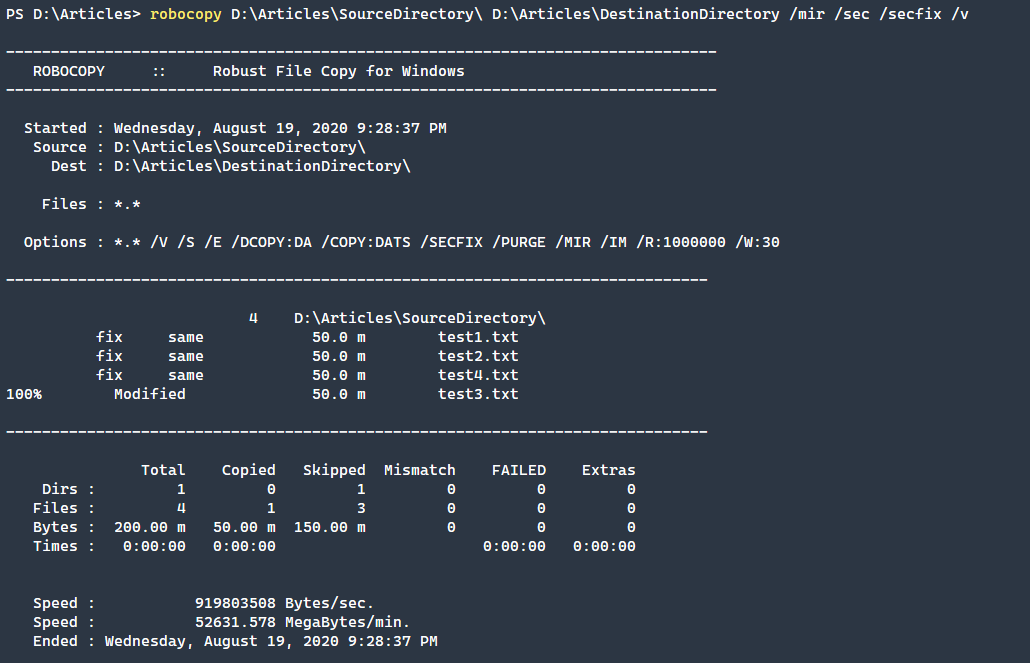
Looking at the test2.txt file that had the source permissions changed, we will see that it copied over to the destination folder with the correct permissions.
If we check on test3.txt that had its destination directory permissions changed we will find that the file now has reverted to what the source directory permissions were.
Using the Mirror Command over the Network
This command works equally well over the network but to work to optimize the speed and performance, there are a few extra commands that can be very useful to use in conjunction with the /mir command.
/zb– Use restartable mode, and upon access denial, attempt to use the backup mode (shadow mode)/MT:nn– Copy files using multiple threads, which you would define by replacing thennplaceholder with the number of threads.8is the default, and16is a reasonable number to test first. Keep in mind that more threads will need more CPU and memory to keep going./tbd– If you are transferring across network shares, then you may encounter Error 67 which is “network name cannot be found” and this option will attempt a retry on that error./r:1 /w:3– These two commands combined tell Robocopy to only retry once and wait 3 seconds in between. This value should be adjusted as necessary, perhaps 5-10 retries and 5 seconds in between, otherwise it will retry near indefinitely and 30 seconds in between./fft– Finally the FFT switch uses FAT file timing instead of NTFS which may introduce around a 2-second drift and less accuracy but more resiliency in transferring files. This is also important when transferring between file systems such as NTFS and EFS./np– This removes the progress bar indicator as this can become inaccurate with the multi-threaded nature of the transfer.
On occasion the
/zcommand can slow down performance, you may need to test with and without to maximize performance and reliability.
With all of these commands combined, you will have a robust solution for mirroring files over the network. To demonstrate this capability, we are mirroring files from a local directory to a remote file share using the fully qualified domain name (FQDN) of the remote server.
Utilizing restartable backup mode, multi-threading, share error handling, FAT file timing, and optimized retry and wait times you should have a robust but performant solution to sending files over the network.
robocopy D:\Articles\SourceDirectory \\server1.fqdn\DestinationShare /mir /zb /mt:16 /tbd /r:1 /w:3 /fft /npYou may notice that in this example, we are not using the /sec or /secfix commands. The reason for this is dependant on your environment. If you are copying files between shares in the same domain then any permissions should properly transfer, unless they are unique local permissions.
If you are transferring files between operating systems, or between shares in different domains or non-domain joined computers, then omitting these commands may work best.
Adjust the multi-threading as necessary to find the proper balance between system performance, bandwidth allowance, and transfer speeds.
Conclusion
System administrators often have complex file transfer needs. Despite many recent tools and solutions that have entered the scene, Robocopy /mir remains a popular solution. Built-in to Windows and updated continuously over new Windows releases, Robocopy remains a key tool when transferring files.
Robocopy is a very powerful tool and specifically, the Robocopy /mir command allows for robust and useful file and folder mirroring across folders and network shares. With the addition of a few useful commands, Robocopy becomes even more powerful and reliable copying files over a network using the Robocopy /mir command.




