Login-AzAccount, Add-AzAccount or Connect-AzAccount there appears to be a lot of different ways to authenticate to an Azure subscription if you’re using PowerShell!
When in Doubt, use Connect-AzAccount
When I first started working with Azure in PowerShell, I was severely confused. I’d find some articles talking about using Login-AzAccount while others mentioned using Add-AzAccount but few mentioning Connect-AzAccount. Which one do I use in what kind of circumstances? What is going on here?!?
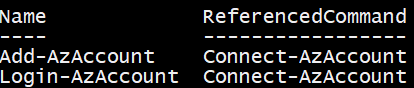
I’m here to tell you if you’re struggling with the same problem I was, the solution is a lot easier than you might expect. Although there may seem to be three different commands to authenticate to Azure with PowerShell, in reality, there’s only one. It is Connect-AzAccount. Both Login-AzAccount and Add-AzAccount are only aliases to the Connect command.
I’m here to tell you to just use Connect-AzAccount and you’ll be good as gold. I don’t recommend using aliases, if possible just because it makes things confusing as you can vouch for. With people using different ways to accomplish the same task, it’s hard to figure out what exactly is happening.
Feel free to verify me by using Get-Alias.
Authenticating with Connect-AzAccount
There are lots of ways to authenticate to Azure using Connect-AzAccount. The method to do so depends on what resources you’re authenticating to. For example, there are roughly five different ways to authenticate to Azure.
- Interactively
- Using a service principal
- Using an Azure Managed Service Identity
- As a Cloud Solution Provider (CSP)
- Into a non-public cloud
Signing in Interactively
The most common way people just starting to work with Azure will connect interactively. This means, they will run Connect-AzAccount and will be prompted for credentials.
This method works if you have a Microsoft or organizational Office 365 account and don’t need to automate the task.
Signing in with a Service Principal
You can also use a service principal to authenticate. This along with the managed service identity is the way to go if you need to authenticate in an automated script. However, this requires creating an Azure Active Directory application along with the service principal itself which is a little set up ahead of time. For a full overview of how to get that set up, you can check out this TechSnips video entitled How To Create And Authenticate To Azure With A Service Principal Using PowerShell. It covers all of the steps you need to get one set up.
Authenticating with a service principal will force you to use the Connect-AzAccount Credential and ServicePrincipal parameters.
The ServicePrincipal parameter indicates that this account authenticates by providing service principal credentials. The Credential parameter specifies a PSCredential object.
Signing in with a Managed Service Identity
Another way is used managed service identities which, to be honest, I have never done before. I’ve provided a link in this section to get an overview of that. Some of the commands used with Connect-AzAccount when authenticating with managed service identities are:
ManagedServiceHostName– Host name for managed service loginManagedServicePort– Port number for managed service loginManagedServiceSecret– Secret, used for some kinds of managed service login.
Signing in as a Cloud Solution Provider (CSP)
If your company is a Microsoft partner and uses Azure services to directly provide resources to your customers, you may use Connect-AzAccount and use the TenantId parameter. This is required to specify a different Azure AD tenant.
Signing into a Non-Public Cloud
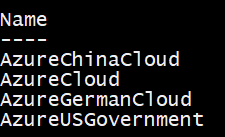
Finally, although not too common is the ability to authenticate to a non-public cloud like a government or country cloud. These clouds are represented by an Azure environment using the Environment parameter on Connect-AzAccount. If you don’t know the environment name, you can always use the Get-AzEnvironment command.
Wrap Up
As you can see, there are a lot of different ways to authenticate to Azure because Azure is a big service! Using Connect-AzAccount with PowerShell, you’ll able to provide all of the necessary parameters Azure needs to interactively or non-interactively process your credentials and allow you to get going!




