There are a few different ways you can delegate access to resources in Azure. One way is via a Shared Access Signature (SAS) token. A SAS token is a way to granularly control how a client can access Azure data. You can control many things such as what resources the client can access, what permission the client has, how long the token is valid for and more.
Not a reader? Watch this related video tutorial!One common use of SAS token is to secure Azure storage accounts through the use of an account SAS.
In this article, you’re going to learn how to create an Azure SAS token both via the Azure portal and via PowerShell. By the time you’re done, you’ll have a SAS token to then pass to various client commands to authenticate and authorize Azure storage management.
Prerequisites
You’ll learn hands-on how to perform a few different tasks in this article. If you’d like to follow along, be sure you have the following prerequisites met.
- An Azure subscription. If you do not have this yet, you can request for a trial subscription.
- Azure Storage Account. Please refer to Create a storage account to learn more.
- The Az PowerShell module (optional). This is required only if you will generate Shared Access Signature tokens using PowerShell
- Windows PowerShell 5.1 or PowerShell Core 6+ if generating a SAS token via PowerShell
Generating a SAS Token using the Azure Portal
The most straightforward way to generate a SAS token is using the Azure Portal. By using the Azure portal, you can navigate the various options graphically.
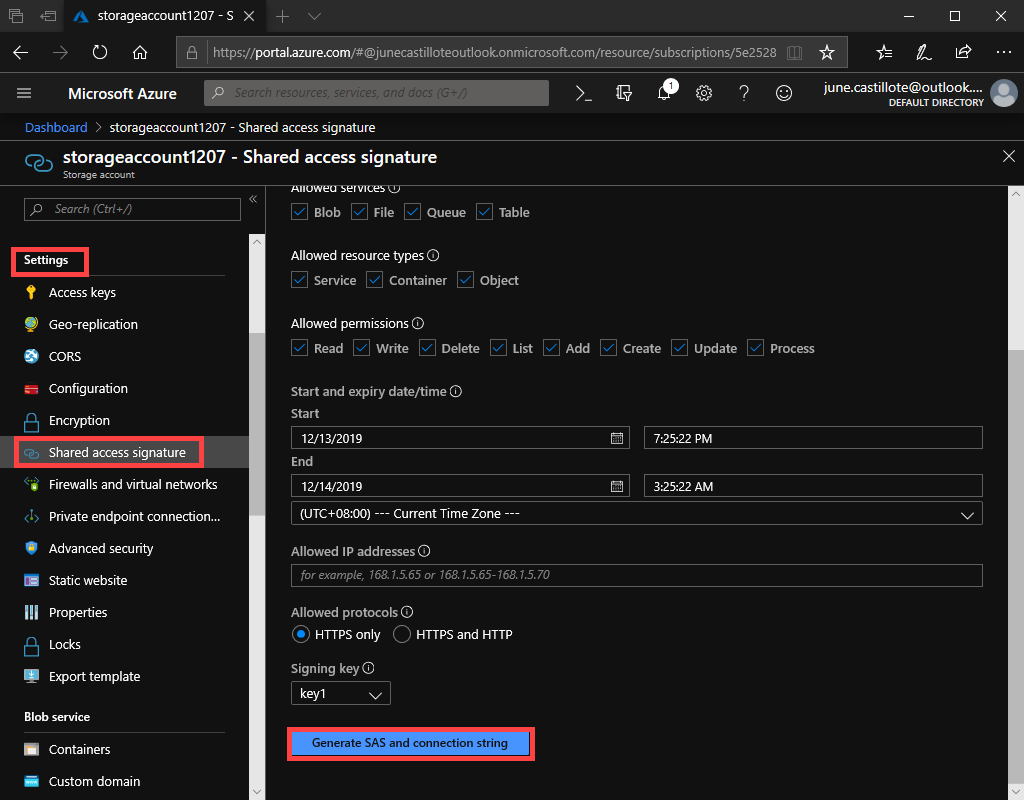
To create a token via the Azure portal, first, navigate to the storage account you’d like to access under the Settings section then click Shared access signature. You can see an example of what this might look like below.
There are many permissions you can grant SAS tokens and start/end times. For this article, you’re going to assign full permissions and leave the default expiration time of eight hours. If you’d like a breakdown and explanation of each permission, check out the Microsoft docs.
Leave all of the default checkboxes and click the Generate SAS and connection string button as shown below.
Once the token is generated, you will see it listed in the boxes below the Generate SAS and connection string button as shown below.
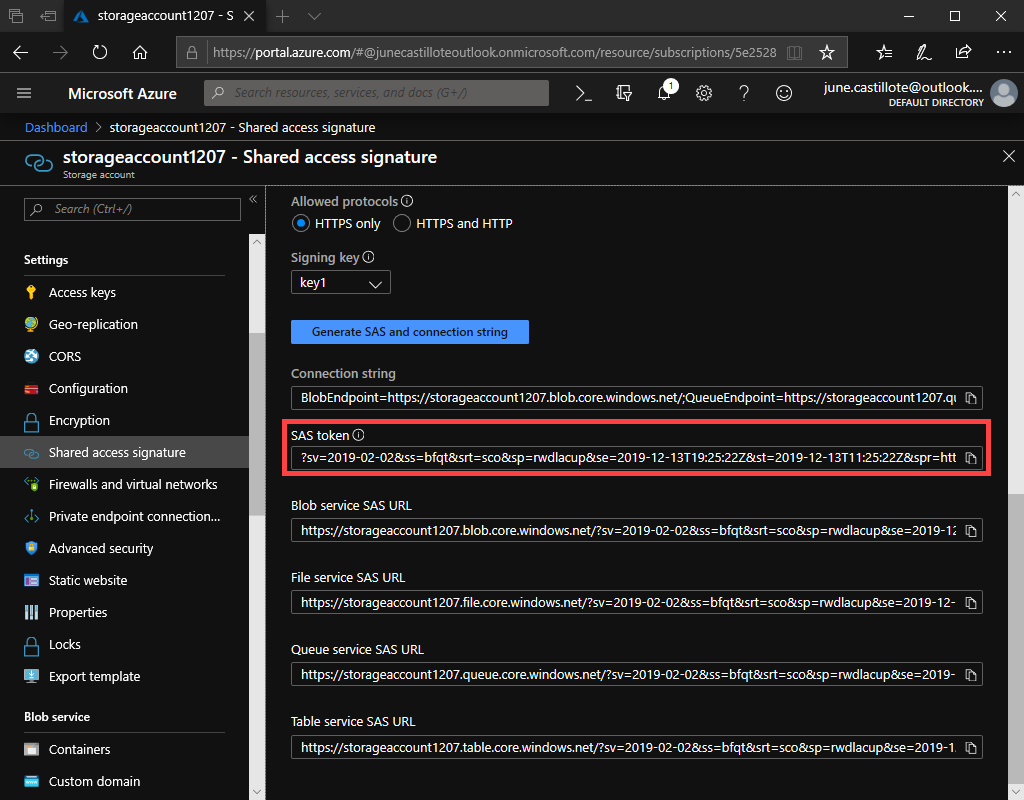
At this point, you can copy the SAS token and paste its value wherever you need to use it.
Generating a SAS Token using PowerShell
To prevent having to log into the Azure portal or, perhaps, if you’re generating SAS tokens for many storage accounts at once, you can use PowerShell. PowerShell uses Azure’s REST API to make calls to Azure to generate the token.
To create a SAS token via PowerShell, first, open up a PowerShell console and authenticate with Connect-AzAccount. Once authenticated, then find the storage account you’d like to access. Below you can see an example of querying a storage account called demo_account in the demo_rg resource group. Using the value of $context, you’ll then pass this to the token-generation command.
$context = (Get-AzStorageAccount -ResourceGroupName 'demo_rg' -AccountName 'demo_account').contextOnce the storage account context is found, then create a SAS token using the New-AzStorageAccountSASToken command. The below example shows generating a SAS token giving full permission to the storage account and all subcomponents.
New-AzStorageAccountSASToken -Context $context -Service Blob,File,Table,Queue -ResourceType Service,Container,Object -Permission racwdlupWhen creating SAS tokens via
New-AzStorageAccountSASToken, the token will be valid for one hour. If you’d like to extend this time, you can use theExpiryTimeparameter.
Limiting SAS Token Permissions
One reason to use a SAS token is giving access to other parties for a limited time and set of permissions. The previous example generated a SAS token with full access permissions. Giving full access is not always the best-case scenario.
The Service parameter defines access to a service or services. For example, use blob to allow access only to the Azure Blob Storage service. Other services include File, Table, and Queue.
The ResourceType parameter limits access to specific types of resources. Using the container as a value, for example, permits access to container resources only. Other valid resource types Service and Object.
The Permission parameter allows you to define allowed permissions. Specify one or more permissions as needed. The value of rwd is equal to giving read, write and delete permissions. Other valid permission values are (l)ist, (a)dd, (u)pdate, and (p)rocess.
Using the SAS Token
There are many ways to use the SAS token generated. One of the most common ways is to use it in a storage context. A storage context is a way you can “package” up credentials to then pass to various commands.
A common way to use the SAS token is via PowerShell. Using the New-AzStorageContext command that’s part of the Az PowerShell module. You can see an example below using the SAS token to upload a file to an existing storage container.
$StorageAccountName = 'foo'
$ContainerName = 'bar'
Create a storage context
$sasToken = ''
$StorageContext = New-AzStorageContext $StorageAccountName -SasToken $sasToken
Upload a file
$storageContainer = Get-AzStorageContainer -Name $ContainerName -Context $StorageContext
$storageContainer | Set-AzStorageBlobContent –File 'C:\file.txt' –Blob 'file.txt'Summary
Creating a SAS token can be done a few different ways. In this article, you learned a couple of the most common ways. Once created, a SAS token can be used in many different ways but deciding that way is up to you.




