If you need to add SSH key to VS Code to set up an SSH connection using key exchange, this tutorial is for you. In this tutorial, you’re going to learn, step-by-step, how to configure VS code to connect over SSH via key exchange for both a user with sudo rights (homelab in this guide) and the built in root user.
Prerequisites
- Visual Studio Code for Windows. This tutorial will be using version 1.5.1.1.
- Windows 10 (SSH is needed and comes pre-installed)
- A remote SSH host – This tutorial will be using an OpenSUSE host with SSH enabled.
- You’ve already set up an SSH Host in VS Code (see this article).
Creating the SSH Key
To begin, you’ll first need to generate a private and public SSH key on your Windows machine.
- Open up PowerShell on your local computer and run ssh-keygen. The default path for your keys is C:\users\<user>\.ssh.
- Provide the folder path to save the private and public key. The default is C:\Users\<user>\.ssh\id_rsa.
- Provide an optional passphrase. If you provide a passphrase, this passphrase will be used to encrypt the private key.
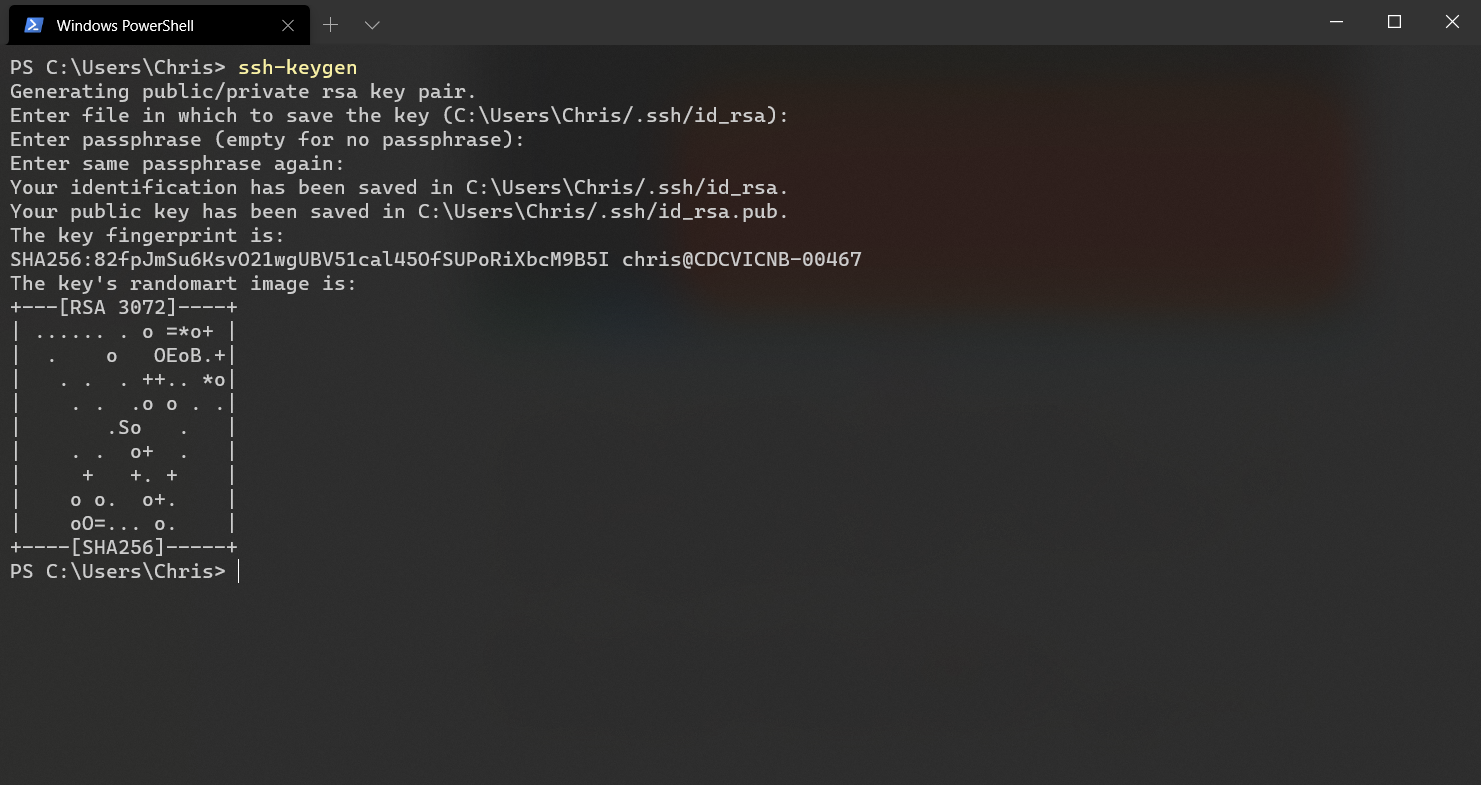
When complete, you’ll now have two files (keys) in the folder you saved the keys into called id_rsa.pub (public key) and id_rsa (private key). By default, these keys will be in the C:\Users\<user>\.ssh folder.
Uploading the Public Key to the SSH Host and Associating your SSH user
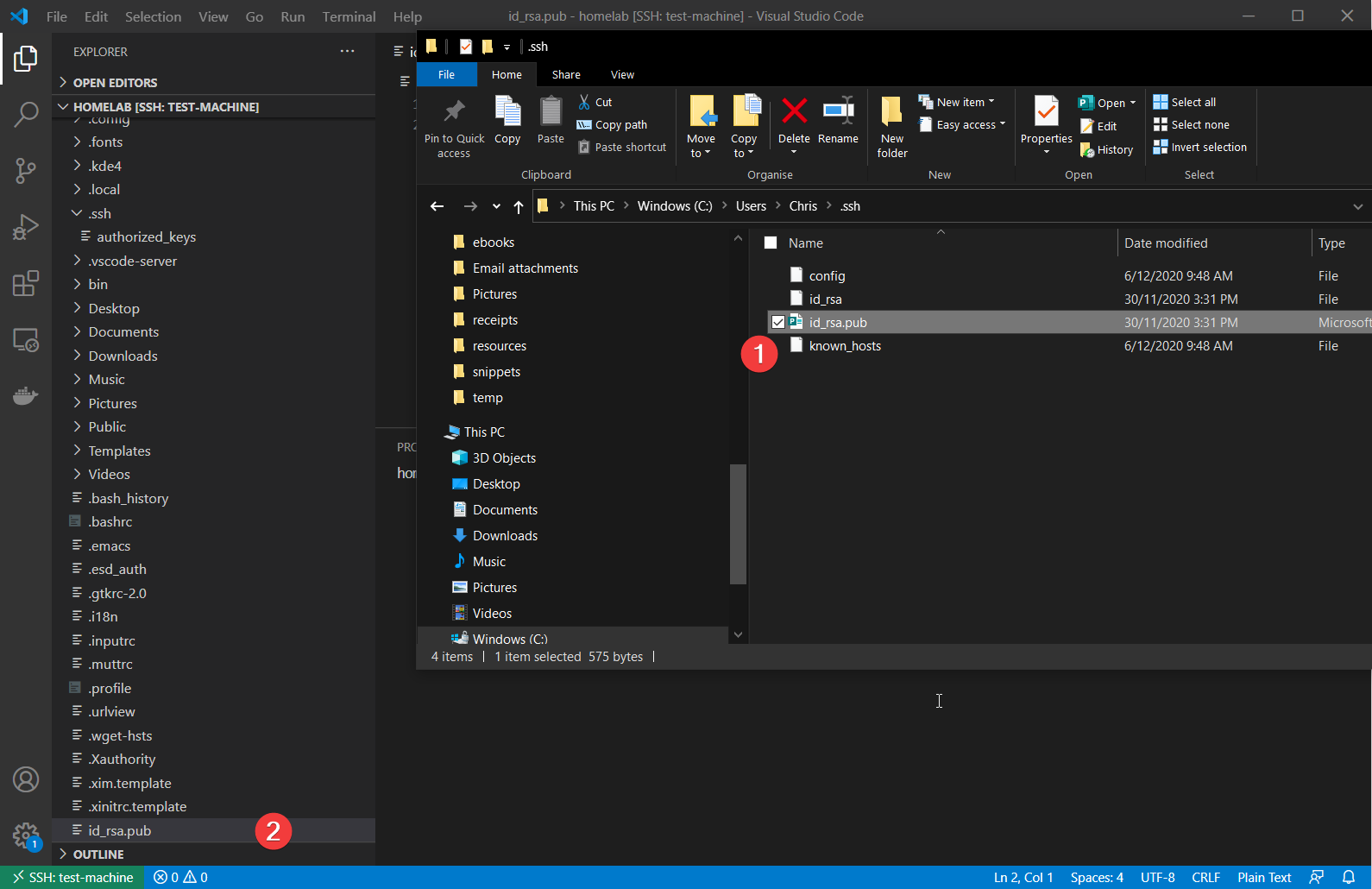
You’ll next need to transfer the public key (id_rsa.pub) to the remote SSH user’s authorized keys location. By using VSCode, you can use its built-in explorer to upload the key.
Related: Setting up an SSH Key Exchange Connection with VS Code and SSH
- If you’ve already set up an SSH host in VS Code, open up the home folder of the user. In this case, the tutorial is using the
homelabuser. - Create the .ssh folder in your home directory and upload the id_rsa.pub file.
- Rename the file to authorized_keys (lower case). You can see this example below.
You have now successfully associated your public key with your SSH user. You should be able to reconnect without requiring a password.
Associating the Public Key with the root User
Associating the same key with the root user gives you the ability to SSH in as either your regular user or the built-in root user.
For the root user this will be copying ~/.ssh/authorized_keys to /root/.ssh/authorized_keys. You can do so by running the below command:
sudo mkdir -p /root/.ssh && sudo cp ~/.ssh/authorized_keys /root/.ssh/authorized_keys
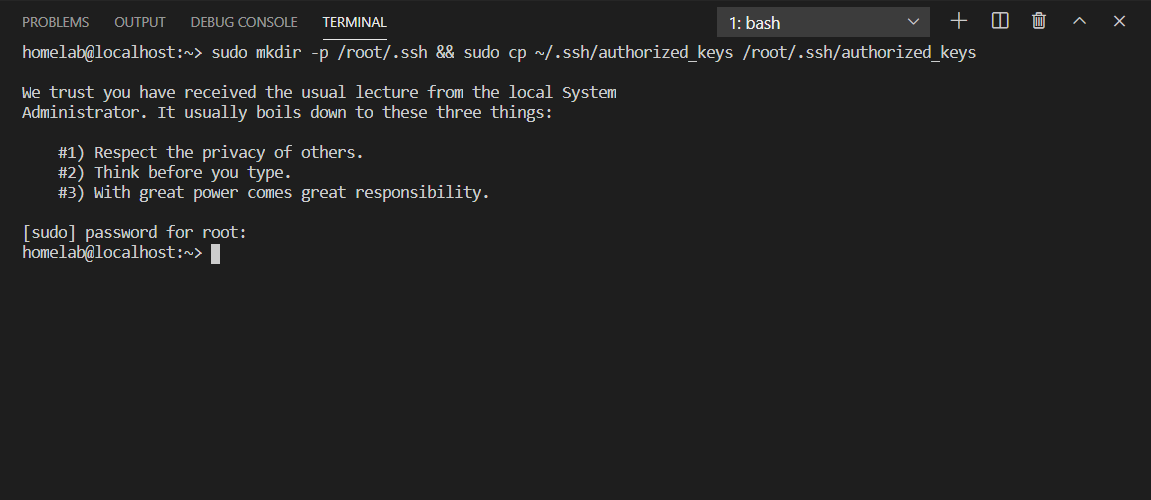
Associating your key with the
rootuser requiressudoadministrative rights. You can read more about sudo here.
You should now be able to log into the root user via SSH without requiring a password in Windows.
Graphically Adding your Public Key to the root user using YaST
If you are more of a visual learner, you can perform the same task using OpenSUSE’s YaST configuration utility. This will be functionally the same as copying the authorized_keys file to the root user, in a more friendly way.
YaST is a configuration tool that is specific to the OpenSUSE distribution.
Related post: A Windows Guy in a Linux World: YaST and the Desktop
- Navigate to the VS Code terminal and upload your id_rsa.pub file to the home directory:
2. Run sudo yast in the VSCode Terminal.
3. Once in YaST, navigate to Security and Users —> User and Group Management using the arrow keys. Press Enter to enter the Users and Group Management section. This step brings you to YaST’s user management screen.
4. Press Alt+S in YaST to change the filter from normal users to system users.
5. Navigate down to root. Hit alt+i to edit and then alt+s again to move to the keys section. You can see that in the animation below:
6. Press alt+a and navigate to the id_rsa.pub file you uploaded earlier and hit alt+o to OK. You should see the fingerprint added to the root user.
7. Keep hitting alt+o to OK out of the menus and finally alt+q to quit. You can see that in the below animation:
At this stage, you’ve successfully performed a key exchange for root! Now delete that uploaded /home/<user>/id_rsa.pub on your Linux host, if you wish.
Authenticating with the Key
Finally, you should test out the connection using the newly created key. To do that:
Open up a PowerShell console and try running ssh <user>@<ip> to test logging in as both your user and the root user. This guide is using the homelab user as the normal user. If all goes well, you should immediately be logged in to either account. You can see this below:
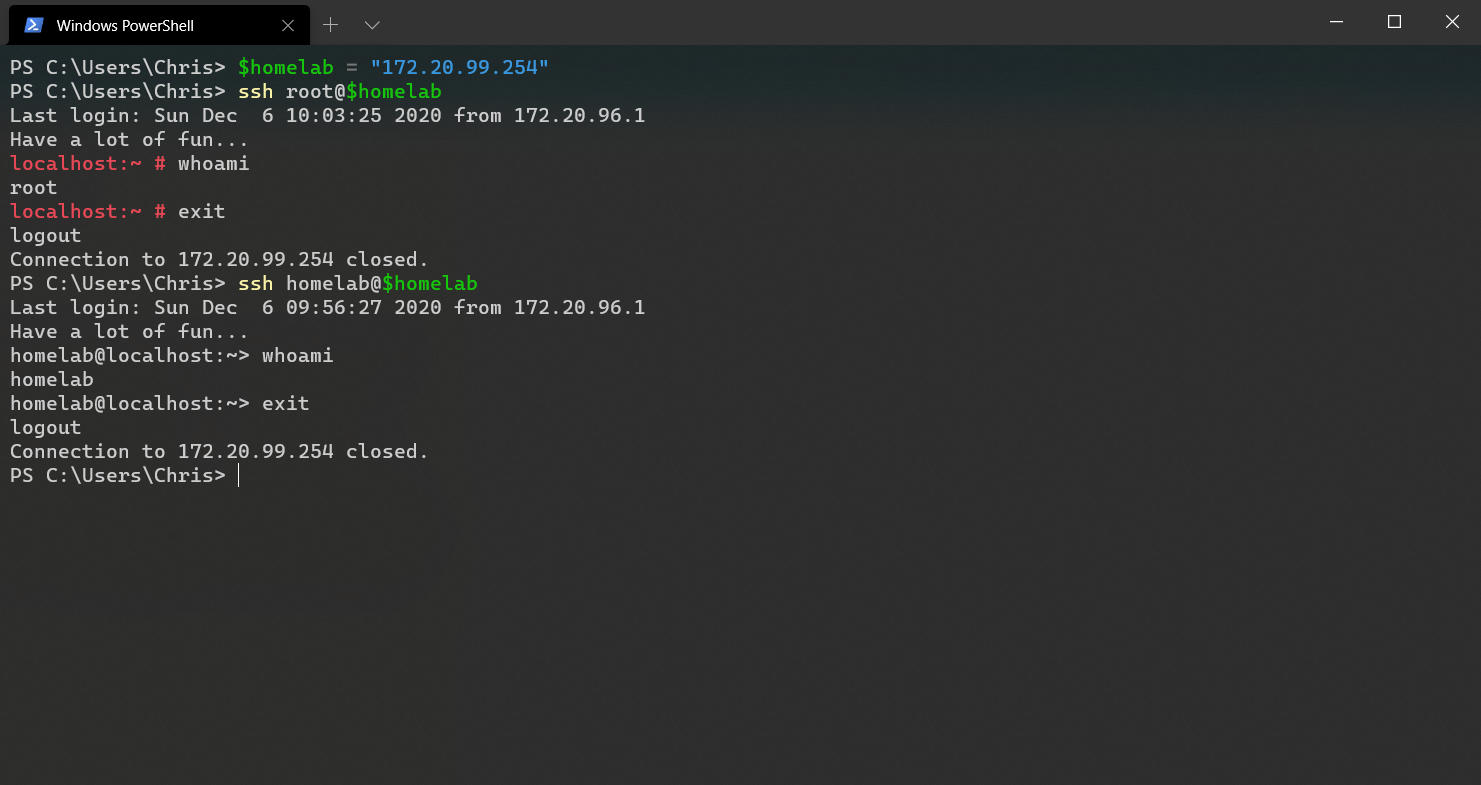
You can now SSH in as root and the terminal didn’t even ask for a password. SSH for Windows knew where to look for your private key (C:\users\<user>\.ssh\id_rsa), and used that automatically to authenticate.
Configuring VS Code to use Either User
What if you need to connect to your remote SSH host using both the root user account and a standard admin user? You can set this scenario up using two different configurations in VS Code.
- In VS Code, click on the Remote Explorer icon in the sidebar and click on the cog under SSH Targets as shown below.
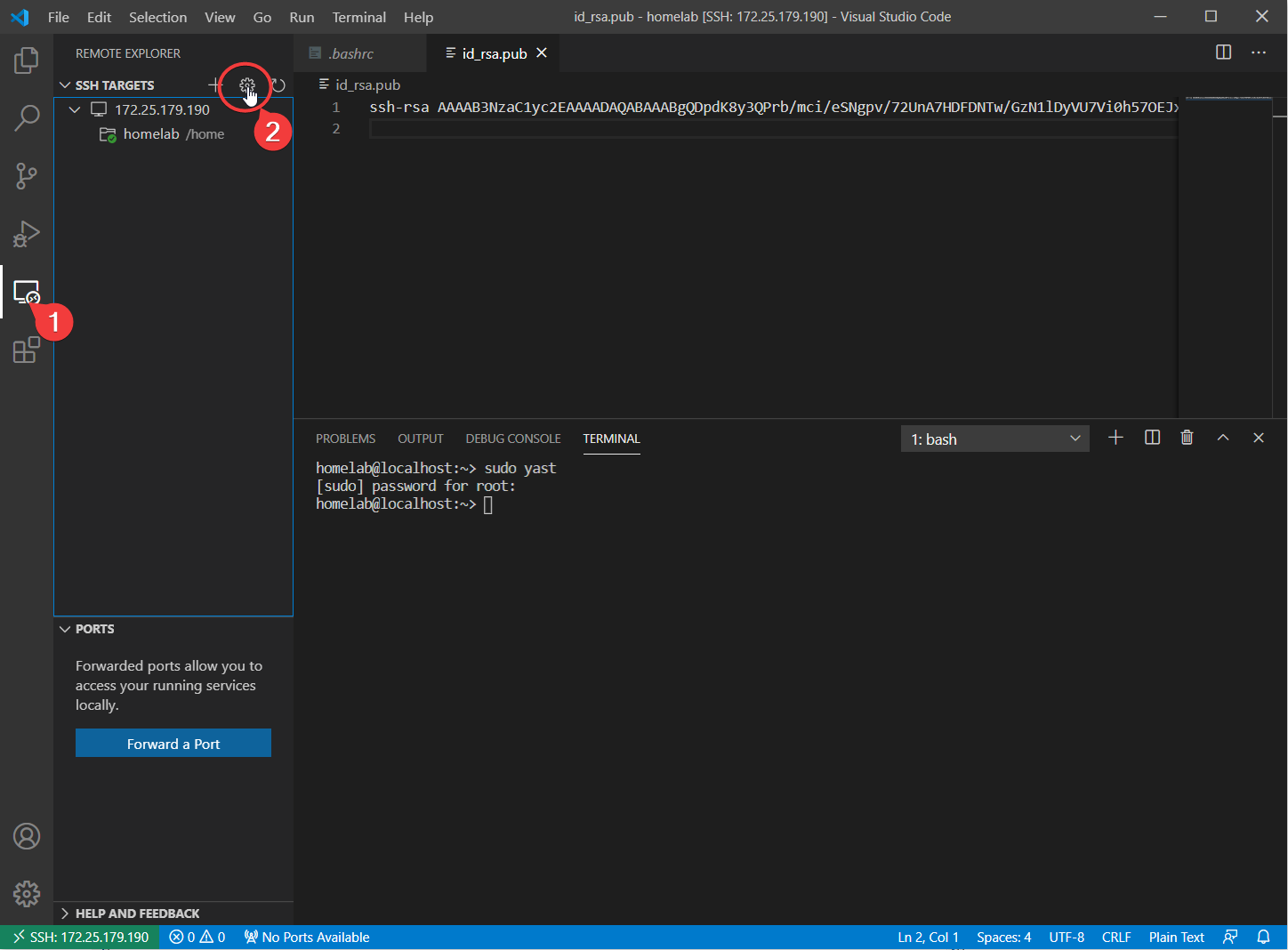
2. VS Code will ask for a file to choose. Press Enter to to choose the default file you generated earlier in this article. VS Code will open up a config file to edit as shown below.
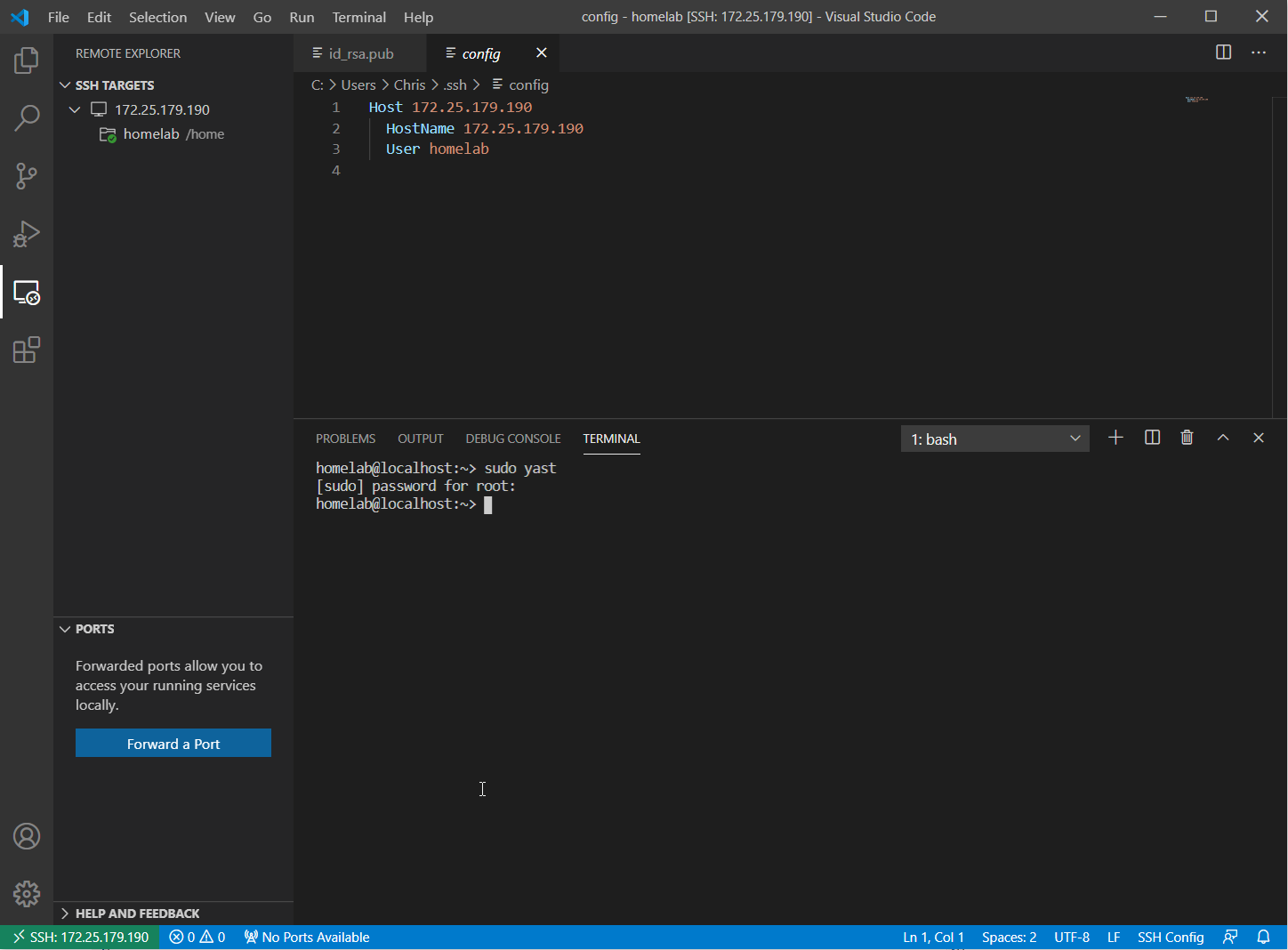
3. Copy the first three lines of the config and paste them below separated with a blank line.
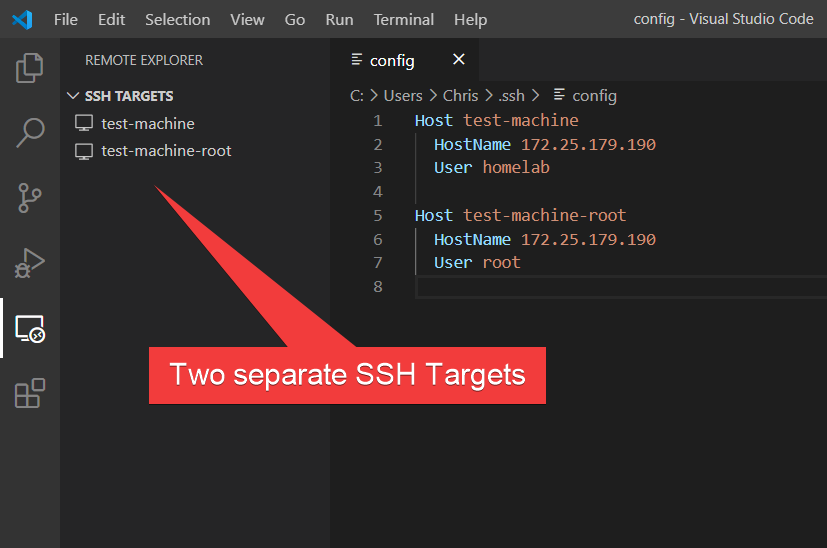
4. Change the second user from <your user> (homelab in the below screenshot) to root. Also, give them more descriptive names (The Host parameter) so you can tell the two configurations apart. Press Control+s to save:
The
Hostparameter is sensitive to spaces and special characters. Name your host only using hyphens and alphanumeric letters.Hostnameis equivalent to either IP or DNS name. The above example is using an IP of172.25.179.190
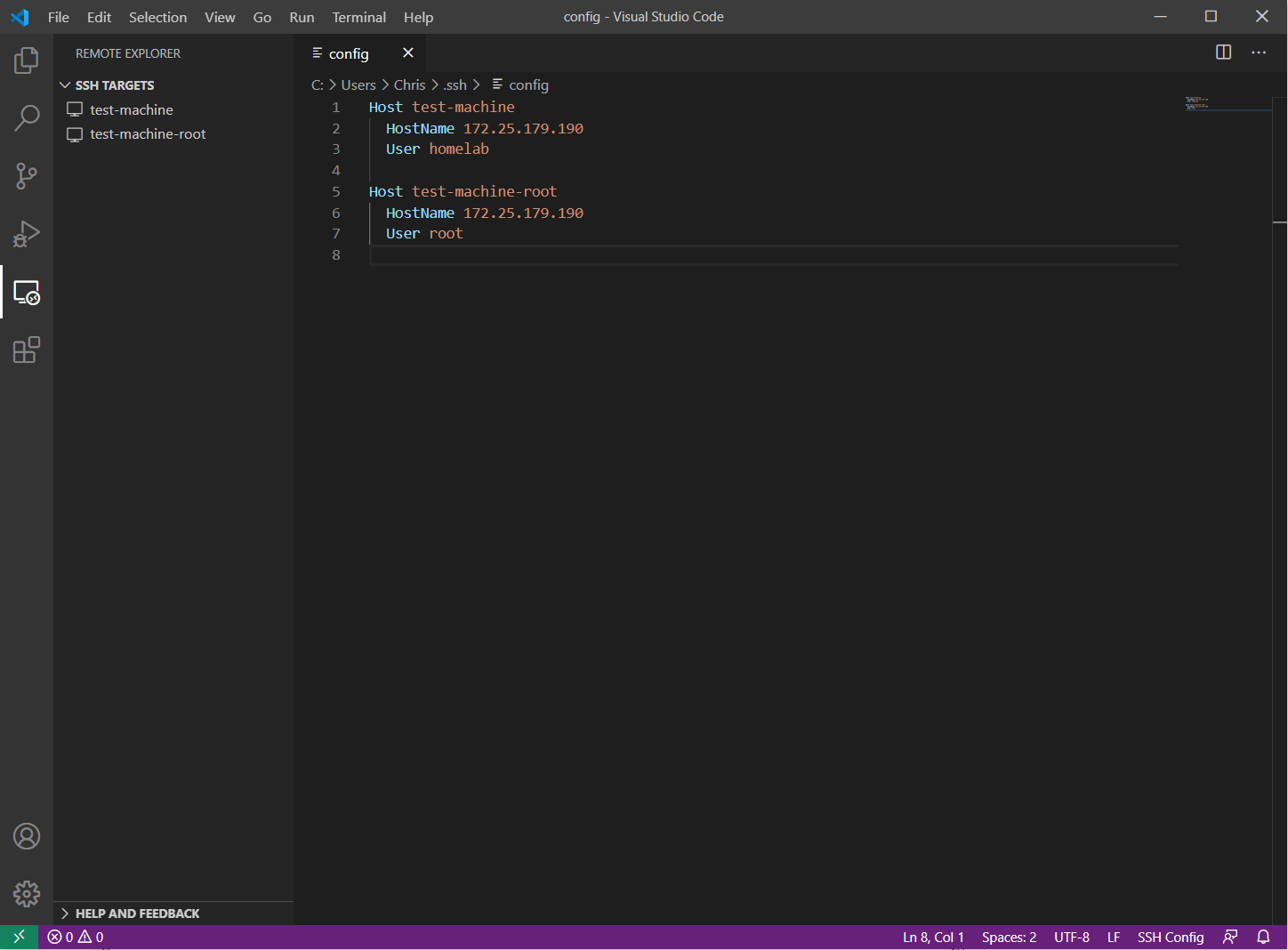
You can now see (in the screenshot below) you have two SSH targets: test-machine, and test-machine-root.
5. Now connect to either host by right-clicking the SSH target and clicking Connect to Host in Current Window as shown below.
If you connect as root, you have full access rights to your machine — including protected files.
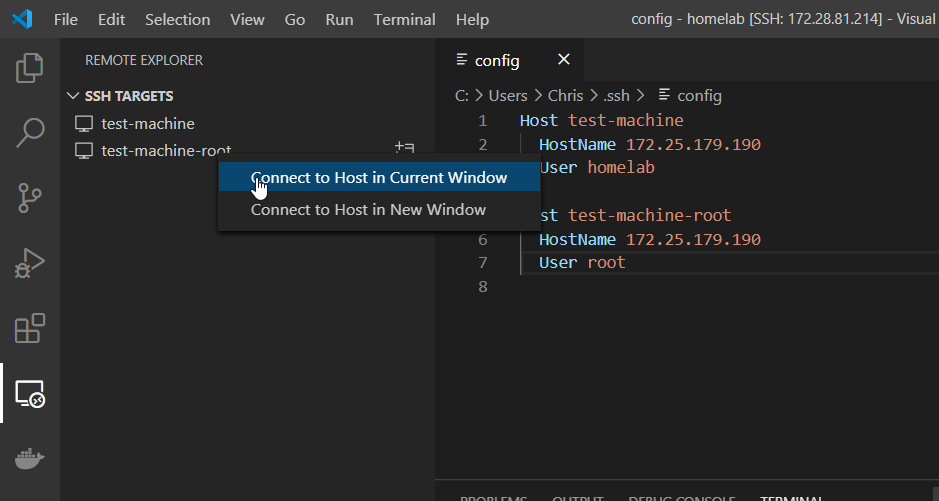
If you Connect to Host in New Window, VSCode will launch a separate instance with the new connection. This lets you have both
rootand<user>open simultaneously in two separate sessions. Do not mix up which is which!