Featured Tutorials
Securing Server Access with Gravitational Teleport
Fortify your infrastructure with Gravitational Teleport for enhanced server security. Streamline access management effortlessly today!
Solve Azure AD Connect Errors via the Microsoft IdFix Tool
Fix Azure AD Connect errors fast with the Microsoft IdFix tool—your go-to solution for seamless synchronization and efficient directory management!
Become a Student of ATA Learning
In-depth, straight to the point, no-nonsense technical tutorials that teach you all the in and outs of the latest (and time-tested) technology today.
- Example-driven tutorials from subject matter experts.
- Carefully edited to ensure ATA quality.
- Written so everyone can understand.
Share your knowledge (and get paid)
Do you know a thing or two about IT, cloud or DevOps? Join us an instructor to share your knowledge, improve your writing and get paid!
- Earn money for your years of hard-earned knowledge!
- Grow as a tech writer with our extensive feedback and proven editing process.
- Meet other technology experts by joining our community.
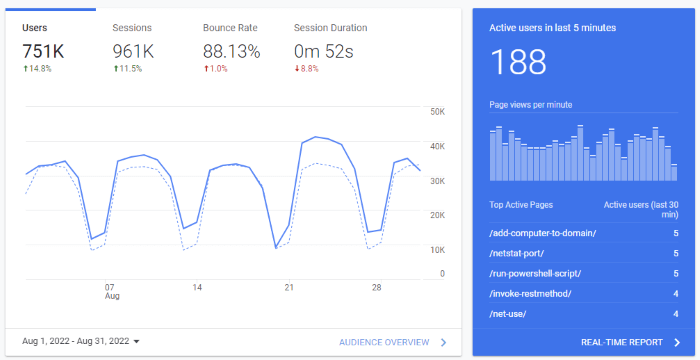
Reach hundreds of thousands of tech learners every month
Over 1 million monthly IT, DevOps and cloud professionals can't be wrong. Get your product or service in front of our engaged audience.
- Over 1 million monthly visitors and growing!
- Flexible advertising and sponsorship opportunities.
- Custom content creation around your product target to your customers.
Our Team

Adam Bertram
Founder

Adam Listek
Director

Rochella Caguin
Content Manager

Matt Zandee
Partnership Manager

Arman Castillote
Editor




