Stay tuned to this article for how to modify dynamic DNS record updates and credential permissions in Active Directory and fix them automatically using PowerShell.
Want to learn more about managing DNS records with PowerShell? Why not pick up and begin learning about DNS records in this detailed, step-by-step, tutorial on managing DNS records.
If you’ve been following some of my past blog posts you’d notice I’ve been fighting some extremely hard to track down DNS problems. The problem reared its ugly head months ago when some important DNS records kept getting removed.
No one could figure out a pattern or timeline as to when or why this was happening. After a ton of research and troubleshooting I believe I have at least discovered all of the root causes. This is my solution to one of them.
One of the problems I was seeing was that the credential permissions on the records that were created via the Microsoft dynamic DNS process were hosed up.
I’m working in an Active Directory environment and all of the zones are AD-integrated which means all of the DNS records are actually AD objects; more specifically dnsNode objects located in the DC=%MYZONE%,CN=MicrosoftDNS,DC=ForestDnsZones,DC=my,DC=domain,DC=local context. These are the objects that kept losing the proper DNS permissions in Active Directory.
I found five records using my DNS record ACL script showing this behavior. After some Sherlock Holmes style sleuthing I managed to find a pattern. All of the servers for these records were re-imaged around the same time. Bingo!
It turns out whenever a computer is brought onto a domain and registers its DNS record, re-imaged or the OS is just reinstalled without removing the DNS record nor removing the AD computer account as part of the process problems can crop up.
In my case, the DNS record still had an orphaned SID.
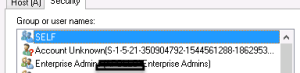
This was the SID of the previous computer account object pre-OS reinstall. The dynamic DNS credential permissions don’t get automatically updated with the new computer object.
If you’re going to repurpose a name it’s best practice to simply remove the computer from the domain and delete the DNS record and then reinstall the OS. However, if you’re in a large enterprise and don’t have this scripted ahem it can be forgotten. This is why I created this solution.
I have this script setup under a scheduled task running every day. It enumerates all of the dynamically-created records in a zone and does three checks
- ensures the owner of the record is the computer account (or the DHCP service account)
- an ACE exists for the computer account (or the DHCP service account)
- the ACE has at least Modify or Full Control access
If any of these are off, it will correct them and create a log of the activity into C:\Windows\Temp\Resolve-DynamicDnsRecordPermissionProblem.ps1.log and email the log afterwards.
I admit this script can be improved upon greatly. For fixing dynamic dns update credential permissions it’s way too big for what I normally like to do and I can see chances for optimization everywhere but getting this far took me a long time and, honestly, I’m too lazy to fix it now. It works.
I’d love to hear from anyone that tries it out in their environment! I highly suggest using -WhatIf first. To get the most updated version of this script feel free to download it or any other of my scripts from my GitHub repo.
.\ResolveDynamicDnsRecordPermissionProblem.ps1 -Zone myzone.com -WhatIfIt won’t delete any records (this is v2, v1 was a niiiiiightmare) but it will make unattended modifications.



